How to Build an Integrated Security Posture Using XDR
Cisco Security
DECEMBER 6, 2021
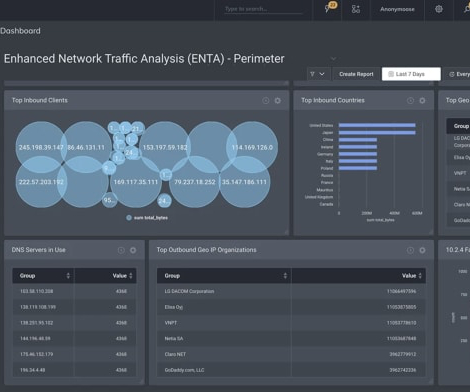
Many organizations today need to integrate their technologies so that their data doesn’t exist in silos. By knocking down the barriers of disparate data, threats are quickly detected by combining multiple sources of intelligence from across their entire network. The solution: extended threat detection and response (XDR).












































Let's personalize your content