Leaked Chats Show LAPSUS$ Stole T-Mobile Source Code
Krebs on Security
APRIL 22, 2022
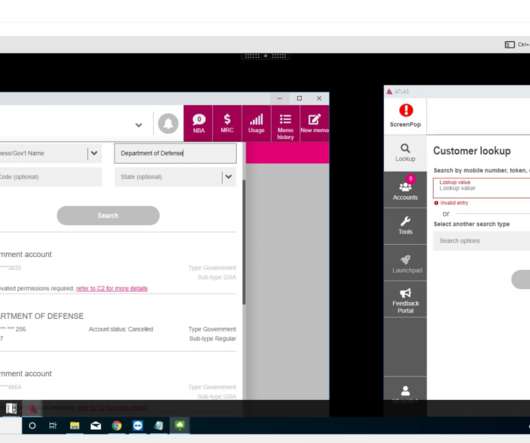
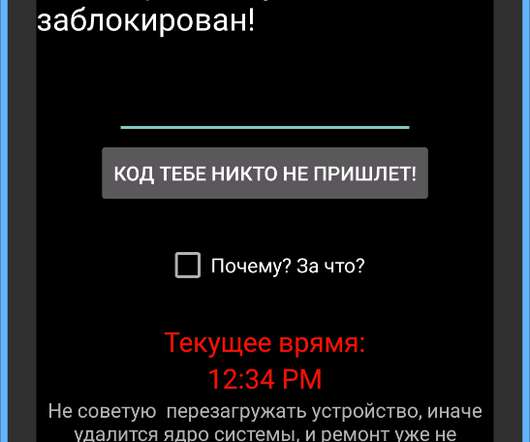
The logs show LAPSUS$ breached T-Mobile multiple times in March, stealing source code for a range of company projects. T-Mobile says no customer or government information was stolen in the intrusion. White is viewing the page via a T-Mobile employee’s virtual machine. “Parents know I simswap,” Amtrak said.







































Let's personalize your content