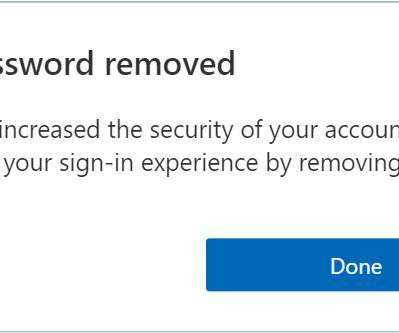
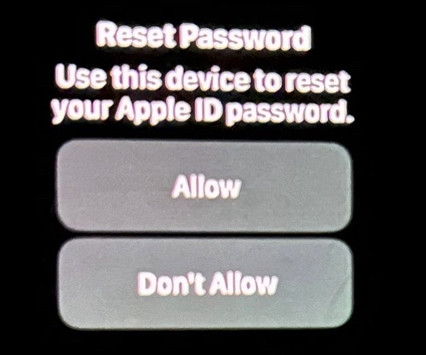
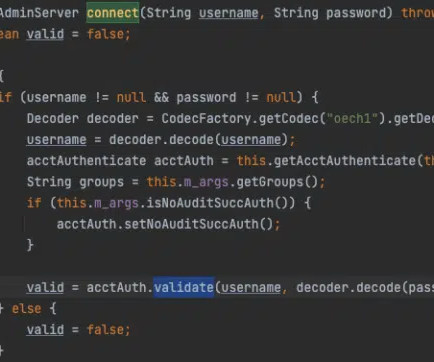
Bypassing Two-Factor Authentication
Schneier on Security
APRIL 1, 2022
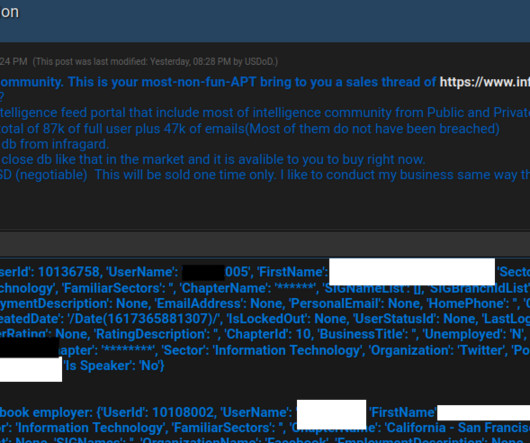
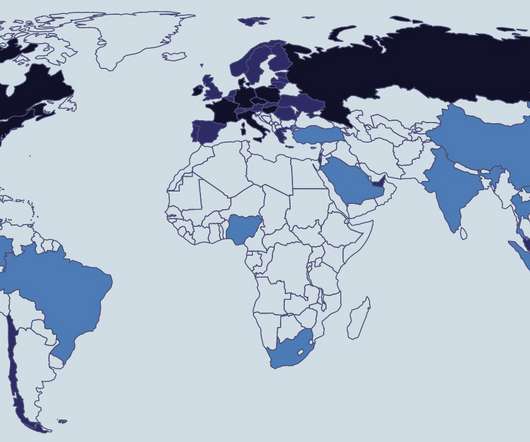
In the past few months, suspected script kiddies like the Lapsus$ data extortion gang and elite Russian-state threat actors (like Cozy Bear, the group behind the SolarWinds hack) have both successfully defeated the protection. […].





































Let's personalize your content