Best Practices Q&A: The importance of articulating how cybersecurity can be a business enabler
The Last Watchdog
APRIL 1, 2024
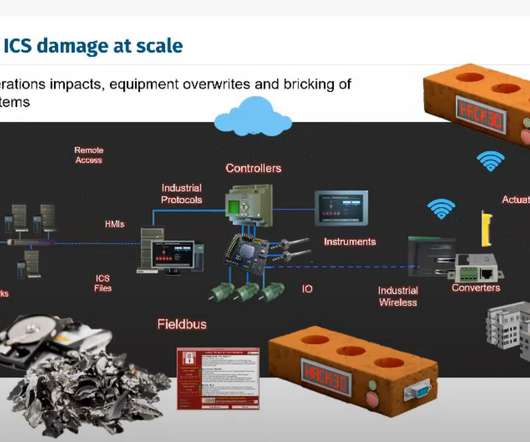
These key capabilities fall under the four competencies of oversight, process risk management, technology risk management, and human risk management. We operate in a world today where your business is the risk and how you adapt is the opportunity. There is also a benefit of stronger business partnerships.
































Let's personalize your content