Preparing for Ransomware: Are Backups Enough?
eSecurity Planet
SEPTEMBER 10, 2021
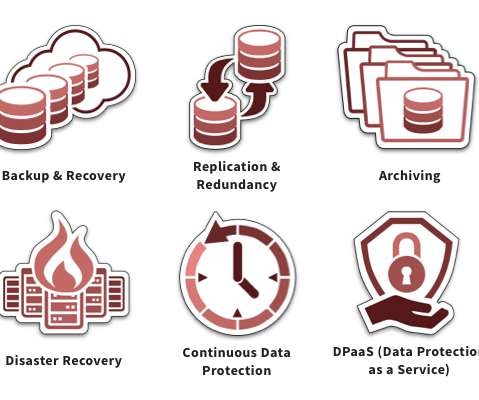
In a year where ransomware has raised the alert levels everywhere, the go-to answer from many is redundancy through offline, remote backups – but are they enough? Backups are a critical component of any enterprise cybersecurity posture, but they are not an airtight strategy. Why Are Backups Critical? The Argument for Backups.














































Let's personalize your content