How to protect backup servers from ransomware
CyberSecurity Insiders
FEBRUARY 16, 2023
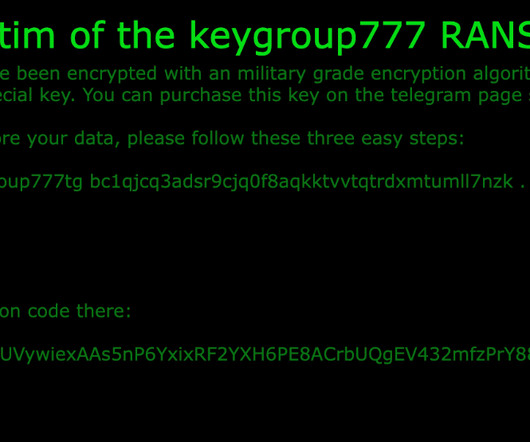
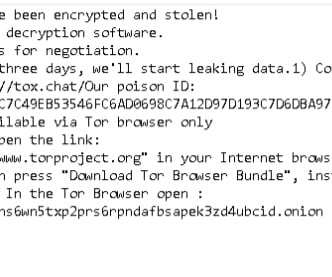
We all know that backup servers are only the sole saviors to an organization when a ransomware incident strikes their IT infrastructure. Block outbound DNS Requests – Whenever a malware strikes a server, the first thing it does is to establish a connection with a command-and-control server.






































Let's personalize your content