The EARN IT Act Is Back
Schneier on Security
FEBRUARY 4, 2022
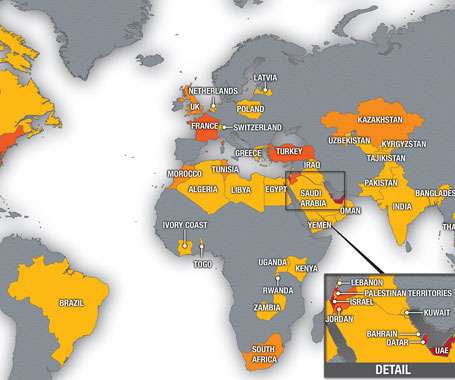
Senators have reintroduced the EARN IT Act, requiring social media companies (among others) to administer a massive surveillance operation on their users: A group of lawmakers led by Sen. The EARN IT Act could ensure that anything hosted online — backups, websites, cloud photos, and more — is scanned. Slashdot thread.


























Let's personalize your content