Most Popular Cybersecurity Blogs from 2023
Lohrman on Security
JANUARY 14, 2024
What were the top government technology and security blogs in 2023? The metrics tell us what cybersecurity and technology infrastructure topics were most popular.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Lohrman on Security
JANUARY 14, 2024
What were the top government technology and security blogs in 2023? The metrics tell us what cybersecurity and technology infrastructure topics were most popular.
Anton on Security
APRIL 11, 2024
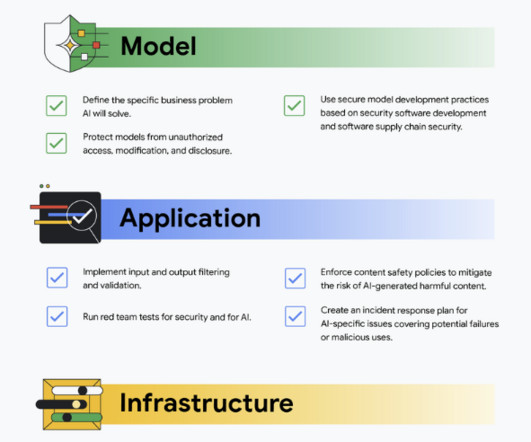
Recently our team has written several papers and blogs focused on securing AI. Here are 5 gen AI security terms busy business leaders should know” defines five key generative AI security terms that busy business leaders should understand to navigate the potential risks and benefits of this technology.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Lohrman on Security
JANUARY 15, 2023
What were the top government technology and security blogs in 2022? The metrics don’t lie, and they tell us what cybersecurity and technology infrastructure topics were most popular.

Security Boulevard
APRIL 4, 2024
5G technology impacts not just our daily lifestyle but the Internet of Things (IoT) as well. Unlike […] The post Impact of IoT Security for 5G Technology appeared first on Kratikal Blogs. Unlike […] The post Impact of IoT Security for 5G Technology appeared first on Kratikal Blogs.

Security Boulevard
JANUARY 14, 2024
What were the top government technology and security blogs in 2023? The metrics tell us what cybersecurity and technology infrastructure topics were most popular. The post Most Popular Cybersecurity Blogs from 2023 appeared first on Security Boulevard.

Schneier on Security
FEBRUARY 25, 2021
I am a co-author on a report published by the Hoover Institution: “ Chinese Technology Platforms Operating in the United States.”

Lohrman on Security
JANUARY 9, 2022
What were the top government security blog posts in 2021? These metrics tell us what cybersecurity and technology infrastructure topics were most popular in the past year.

Heimadal Security
FEBRUARY 1, 2024
We have partnered with Jupiter Technology Corporation, who will distribute our cybersecurity products across Japan as part of a long-term sales and distribution agreement. It […] The post Heimdal Partners with Jupiter Technology to Distribute Cybersecurity Solutions in Japan appeared first on Heimdal Security Blog.
Security Boulevard
APRIL 11, 2024
Recently our team has written several papers and blogs focused on securing AI. Here are 5 gen AI security terms busy business leaders should know” defines five key generative AI security terms that busy business leaders should understand to navigate the potential risks and benefits of this technology.

Security Boulevard
FEBRUARY 22, 2024
However, technology also enables more sophisticated and harmful network attacks. DDoS attacks threaten […] The post NSFOCUS Innovative DDoS Protection Technology Secures Your Network Perimeter appeared first on NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

Schneier on Security
NOVEMBER 14, 2019
Technology is now deeply intertwined with policy. It's all changing fast; technology is literally creating the world we all live in, and policymakers can't keep up. The answer requires a deep understanding of both the policy tools available to modern society and the technologies of AI. Today, it's a crisis.

NSTIC
OCTOBER 24, 2023
During this week’s blog series, we sat down with two of our NIST experts from the Visualization and Usability Group at NIST — Shanée Dawkins and Jody Jacobs — who discussed the importance of recognizing and reporting phishing. We work in the Information Technology Lab, but our

Heimadal Security
OCTOBER 4, 2022
The technological revolutions taking place in practically every aspect of our lives are causing a significant change in the dynamics of society. European industry leaders, policymakers, innovators, pioneers, and investors gathered last week in London for the Bloomberg Technology […].

Heimadal Security
JULY 12, 2023
The switch from a hand-on approach to IAG means much more than taking advantage of emerging technologies; one would call it an authentic epistemological shift; an […] The post Access Governance Strategy and Technology: How to Plan It Well appeared first on Heimdal Security Blog.

CompTIA on Cybersecurity
DECEMBER 15, 2020
This year’s list of CompTIA’s top technology business blogs demonstrates how the tech industry responded to the pandemic, how our businesses pivoted in the midst of unprecedented chaos and change, and, ultimately, how we’ve emerged tougher and more resilient.

NSTIC
OCTOBER 10, 2023
Today’s blog is the second one in our 2023 Cybersecurity Awareness Month series and examines different factors associated with using strong passwords and a password manager. Yee-Yin : At NIST, I’ve been conducting research on human factors and the usability aspects of human-technology interactions. One research area is human

Security Boulevard
DECEMBER 8, 2021
The post The Evolving Technology of Cybercrime appeared first on Ericom Blog. The post The Evolving Technology of Cybercrime appeared first on Security Boulevard.
Heimadal Security
MAY 12, 2023
ABB, a leading provider of electrification and automation technology, has been hit by a Black Basta ransomware attack, which has reportedly affected business operations. As part of its services, ABB develops industrial control systems (ICS) and SCADA systems for manufacturers and energy suppliers.

CSO Magazine
JUNE 9, 2023
Google, owner of the generative AI chatbot Bard and parent company of AI research lab DeepMind, said a framework across the public and private sectors is essential for making sure that responsible actors safeguard the technology that supports AI advancements so that when AI models are implemented, they’re secure-by-default.

TrustArc
MAY 4, 2023
How has information technology impacted data privacy and protection? Explore technology's explosive growth on data security and public safety. The post How Information Technology Impacts Data Privacy appeared first on TrustArc Privacy Blog.

Heimadal Security
JANUARY 4, 2023
Following a recent cyberattack on the Queensland University of Technology, the Royal ransomware gang has begun leaking data they allegedly stole during the intrusion. Queensland University of Technology (QUT) has 52,672 students and operates on a budget exceeding one billion Australian dollars.

SecureWorld News
FEBRUARY 13, 2024
This morning, I read an article about how brain scanning technology is causing Colorado and Minnesota to propose legislation that is aimed at establishing rights and protections for information collected from our thoughts through the neural signals that can be scanned and collected from our brains. federal Computer Fraud and Abuse Act.

Security Boulevard
JANUARY 8, 2024
2023 Wrapped: Most Viewed Blogs of 2023 ltabo Mon, 01/08/2024 - 13:05 It’s hard to believe that 2023 is over and we are helping our customers plan their 2024 SAP security strategies. Corporate Virginia Satrom The post 2023 Wrapped: Most Viewed Blogs of 2023 appeared first on Security Boulevard. 5000 list for the third year in a row.

Security Boulevard
MARCH 21, 2024
Healthcare organizations increasingly rely on technology to store, manage, and transmit sensitive patient information. The post Safeguarding Patient Data with HITRUST Compliance: A Comprehensive Guide for Healthcare Technology Companies appeared first on Hyperproof.

Identity IQ
JANUARY 10, 2023
Top 10 IdentityIQ Blog Posts of 2022. With a final look back at 2022, we’re rounding up the most searched and visited blog posts from last year. The top 10 most popular blog topics on the IdentityIQ website last year include: What to Do if My Email Is Found on the Dark Web? IdentityIQ. How Important are Phone Software Updates?
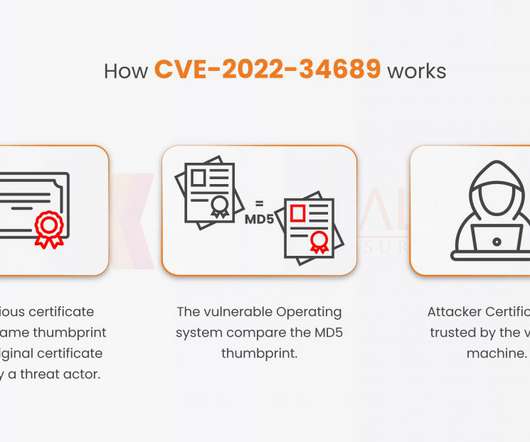
Security Boulevard
FEBRUARY 13, 2023
The CryptoAPI function enables programmers to select the algorithms and protocols that […] The post “Securing Your technology from Crypto API Bug” appeared first on Kratikal Blogs. The post “Securing Your technology from Crypto API Bug” appeared first on Security Boulevard.

Security Boulevard
AUGUST 3, 2023
However, this data is … Safeguarding User Data: How Innovative Technologies Are Bolstering Client Security Read More » The post Safeguarding User Data: How Innovative Technologies Are Bolstering Client Security appeared first on TechSpective.

Security Boulevard
FEBRUARY 17, 2022
In my last blog post, we discussed the need for businesses to adopt distributed development and delivery models in order to bring value to their customers. Cloud technologies have come to the forefront in providing solutions that organizations can leverage in order to meet and drive consumer demand.

Security Boulevard
JANUARY 17, 2023
Still, recent technological developments, Read More. The post Cybersecurity: It’s More Than Just Technology – The Human Element Matters Too appeared first on Nuspire. The post Cybersecurity: It’s More Than Just Technology – The Human Element Matters Too appeared first on Security Boulevard.

Security Boulevard
MARCH 18, 2022
Cyber Attackers Tap Cloud Native Technologies in Russia-Ukraine War. This once again shows that today you don’t have to be a skilled hacker to take part in cyber war. ”. -- Cloud Native Technologies Used in Russia-Ukraine Cyber Attacks , Aqua , March 15, 2022. brooke.crothers. Fri, 03/18/2022 - 16:58. Sometimes for good. Related Posts.

Security Boulevard
JULY 17, 2023
There are plenty of documented examples of truly impressive feats built on this technology: writing reports or outputting code in seconds. The post Forbes Technology Council: Why Large Language Models (LLMs) Alone Won’t Save Cybersecurity appeared first on Security Boulevard. At its core, LLMs basically ingest A LOT of text (e.g.,

TrustArc
MAY 31, 2023
The post Privacy Technology Brief: Managing Third-Party Vendor Risk with TrustArc appeared first on TrustArc Privacy Blog. TrustArc’s Assessment Manager gives companies automated tools and a powerful risk management framework to help privacy and security professionals evaluate third-party vendor risk.

Security Boulevard
FEBRUARY 10, 2022
Over the past few years, we’ve seen almost every company that runs software change their strategies to include some type of cloud technology to support their workloads. The post GitHub Actions Blog Series, Part 2: Deploying with Amazon EKS appeared first on Security Boulevard.

Security Boulevard
NOVEMBER 24, 2023
A strong grasp of high-tech devices can help aging … Cultivating Digital Inclusion: Empowering Aging Adults Through Technology Read More » The post Cultivating Digital Inclusion: Empowering Aging Adults Through Technology appeared first on TechSpective.

Schneier on Security
MARCH 8, 2019
Government Needs You : Travis Moore, TechCongress; Hashim Mteuzi, Senior Manager, Network Talent Initiative, Code for America; Gigi Sohn, Distinguished Fellow, Georgetown Law Institute for Technology, Law and Policy; and Ashkan Soltani, Independent Consultant. Here is my blog post about the event. Video here.).
Security Boulevard
JULY 20, 2022
We are in the middle of a doctrinal shift in the security industry that requires new technology innovation. These blogs provide an overview. The post ICYMI: Top 5 Blogs on Securing the Atomized Network appeared first on Netography.

Security Boulevard
AUGUST 5, 2021
The post How Cloud Native Technology will Impact 5G Mobile Networks appeared first on Radware Blog. The post How Cloud Native Technology will Impact 5G Mobile Networks appeared first on Security Boulevard. CSPs understand today that they need more from cloud.
Security Boulevard
NOVEMBER 22, 2021
Internet of Things (IoT) technology has brought many advantages to our life. Among them, there are Identity management and object recognition, which are IoT enabling Technologies. This technology provides an effective solution to the security [.]. This technology provides an effective solution to the security [.].

Security Boulevard
DECEMBER 28, 2021
Our insightful blogs helped millions of people globally understand, implement, and enhance their platform experience by leveraging cutting-edge technology in the CIAM landscape in 2021. The post Top 10 Performing Identity Blogs in 2021 appeared first on Security Boulevard.
Security Affairs
JUNE 1, 2023
The BlackCat ransomware gang claims to have hacked the Casepoint legal technology platform used US agencies, including SEC and FBI. Casepoint legal technology platform used by the SEC, USDA and US Courts has allegedly been breached by BlackCat. We encourage you to get in touch or we’ll start posting your data on our blog soon.
Heimadal Security
JANUARY 18, 2022
Since at least 2019, a massive cyber-espionage operation targeting mainly renewable energy and industrial technology entities has been operational, impacting more than fifteen organizations all over the world.

CompTIA on Cybersecurity
DECEMBER 14, 2021
The list of CompTIA's Top 10 membership blogs for 2021 includes a diverse mix of content focused on four overarching themes: emerging technologies, cybersecurity, solutions selling and the tech workforce.

Security Boulevard
JUNE 3, 2022
Weekly Blog Post. At The Corner Of Cyber And Blog. Cybersecurity experts, including global technology companies like Cisco, Google, and Amazon, have had their share of attacks. The post Weekly Blog Post appeared first on Security Boulevard. Should Being Hacked Lead To A Termination Of Employment? What happened, people?”.
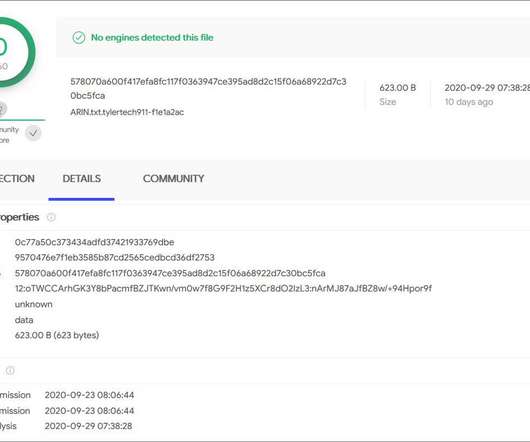
Heimadal Security
JUNE 17, 2021
The Tyler Technology Ransomware attack is one of the most important attacks that happened in the past years as Tyler Technologies, Inc. The post The Tyler Technology Ransomware Attack Overview appeared first on Heimdal Security Blog. represents the largest provider of software to the United States public sector.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content