Cloud Security Podcast by Google?—?Popular Episodes by Topic
Anton on Security
APRIL 7, 2022
Popular Episodes by Topic This is simply a post that categorizes our podcast episodes by topic and then by download/listen count.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Anton on Security
APRIL 7, 2022
Popular Episodes by Topic This is simply a post that categorizes our podcast episodes by topic and then by download/listen count.

Thales Cloud Protection & Licensing
MAY 17, 2018
at least, the chapters that I understand), our systems engineers have found that actual secure cloud migration tends to cut across many domains of cloud security. The post Secure Cloud Migration and the Cloud Security Alliance appeared first on Data Security Blog | Thales e-Security.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CyberSecurity Insiders
FEBRUARY 2, 2022
HEAT attacks leverage one or more of the following core techniques that bypass legacy network security defenses: Evades Both Static and Dynamic Content Inspection: HEAT attacks evade both signature and behavioral analysis engines to deliver malicious payloads to the victim using innovative techniques such as HTML Smuggling.
Security Boulevard
APRIL 7, 2022
Data Security in the Cloud“. The Mysteries of Detection Engineering: Revealed! “. EP58 SOC is Not Dead: How to Grow and Develop Your SOC for Cloud”. EP58 SOC is Not Dead: How to Grow and Develop Your SOC for Cloud”. The Mysteries of Detection Engineering: Revealed! “. Cloud migration (top 5).

The Last Watchdog
AUGUST 1, 2023
. “Cloud-born edge infrastructure solutions are altering the way we engage with each other and interact with physical spaces in offices, schools, and venues. Patel “Cloud migration strategies for anywhere access to enterprise apps is top of mind for all IT executives, creating a tremendous opportunity for Nile.

Anton on Security
MARCH 3, 2022
“A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next” Top 5 Cloud Security Podcast by Google episodes: Episode 1“Confidentially Speaking” Episode 2 “Data Security in the Cloud” Episode 8 “Zero Trust: Fast Forward from 2010 to 2021” Episode 27 “The Mysteries of Detection Engineering: Revealed!”

The Last Watchdog
MAY 9, 2023
This was all part of the Lehi, Utah-based vendor’s efforts to support enterprise cloud migration and the rise of IoT systems, which were both gaining steam. We went out and hired engineering talent from our competitors, gave them a clean slate and tremendous executive commitment,” he says. “We
Anton on Security
AUGUST 9, 2023
Cloud Migration Security Woes” “Move to Cloud: A Chance to Finally Transform Security?” “Is Is Your Fate In the Cloud?” 2020 Anton’s Security Blog Quarterly Q3 2023 was originally published in Anton on Security on Medium, where people are continuing the conversation by highlighting and responding to this story.

The Last Watchdog
APRIL 30, 2023
I spoke with Token CEO John Gunn and his engineering VP Evan K. The trick in today’s operating environment is how to do this well with cloud migration accelerating. about the role of advanced wearable authentication devices, going forward. Leveraging threat intelligence at the platform level, or course, remains vital, as well.

The Last Watchdog
APRIL 28, 2023
The trick in today’s operating environment is how to do this well with cloud migration accelerating. about the role of advanced wearable authentication devices, going forward. Operationalizing threat intel Collecting and using good threat intelligence has always been important — and never been easy to do well.

Cisco Security
MAY 3, 2021
In addition to “Best Security Company,” Cisco has also won the SC Media award for “Best Small and Medium Enterprise (SME) Security Solution,” based on our Cisco Umbrella cloud-based security. We have also been named “Best Network Access Control (NAC) Solution” for the Cisco Identity Services Engine (ISE).

The Security Ledger
SEPTEMBER 6, 2021
Nir helped discover the recent CHAOS DB flaw in Azure COSMOS DB, the flagship database for Microsoft’s Azure cloud platform. Related Stories Episode 224: Engineering Trust In The Cyber Executive Order Encore Podcast: Chris Valasek on Hacking The Jeep Cherokee Encore Podcast: Is Autonomous Driving Heading for a Crash?

Anton on Security
MAY 25, 2022
“A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next” Top 5 Cloud Security Podcast by Google episodes: Episode 1“Confidentially Speaking” Episode 2 “Data Security in the Cloud” Episode 47 “Megatrends, Macro-changes, Microservices, Oh My! Is Your Fate In the Cloud?”

The Last Watchdog
OCTOBER 10, 2019
Yet, somehow, catastrophic cloud breaches continued to occur, ala Capital One recently losing 100 million customer records kept in its Amazon Web Services S3 data storage buckets. I had the chance to speak with Mahesh Rachakonda, vice president of products and solution engineering at CipherCloud, a San Jose, CA-based CASB, about this.

The Security Ledger
SEPTEMBER 6, 2021
Nir helped discover the recent CHAOS DB flaw in Azure COSMOS DB, the flagship database for Microsoft’s Azure cloud platform. Related Stories Episode 224: Engineering Trust In The Cyber Executive Order Encore Podcast: Chris Valasek on Hacking The Jeep Cherokee Encore Podcast: Is Autonomous Driving Heading for a Crash?

Security Boulevard
MARCH 3, 2022
Top 5 Cloud Security Podcast by Google episodes: Episode 1“Confidentially Speaking”. Episode 2 “Data Security in the Cloud”. Episode 27 “The Mysteries of Detection Engineering: Revealed!”. Not just compliance: reimagining DLP for today’s cloud-centric world” [GCP Blog]. Cloud Migration Security Woes”. “Is

Spinone
DECEMBER 12, 2018
There are certainly challenges with migrating between public clouds as many organizations may suffer from certain “vendor lock in” that takes place when services and virtual resources exist in one public cloud provider vs. another. TRY IT FREE The post Cloud Migration Guide Introduction first appeared on SpinOne.
Anton on Security
FEBRUARY 8, 2022
“On Threat Detection Uncertainty” “Is Your Fate In the Cloud?” Move to Cloud: A Chance to Finally Transform Security?” Cloud Migration Security Woes” “A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next” “EP27 The Mysteries of Detection Engineering: Revealed!” (on

Security Boulevard
MAY 18, 2023
This repeated recognition by Gartner is a testament to not only the commitment and hard work of our product and engineering teams but also to the trust placed in us by our customers. (In In fact, you can see what many have already said about us on Gartner Peer Insights.)

Identity IQ
DECEMBER 8, 2021
During his career, Glennon has built software and infrastructure teams from the ground up, managed complex datacenter and cloud migrations, managed transitions from legacy to modern engineering standards and recruited top-tier talent while building scalable business models to drive long-term success.
CyberSecurity Insiders
JANUARY 26, 2022
41% of large enterprises will invest in IT modernization projects such as resolving technical debt and cloud migration in the next two years. The finance industry has the highest percentage of companies planning to spend over $1 million in 2022 on digital initiatives (31%), followed by Research/Engineering (26%).

McAfee
NOVEMBER 3, 2020
In this role, Diane is accountable for the security of the retail stores, cyber-security, infrastructure, security/network engineering, data protection, third-party risk assessments, Directory Services, SOX & PCI compliance, application security, security awareness and Identity Management.

Thales Cloud Protection & Licensing
AUGUST 9, 2018
This market demand for more control of cloud-migrated data spawned Bring Your Own Key (BYOK) APIs. Although every cloud provider seems to have a different service name, API, and process for importing keys or key material, the big guys all offer a solution. Azure Information Protection tenant key with Azure Key Vault.

Security Boulevard
SEPTEMBER 16, 2021
Episode 2 “Data Security in the Cloud”. Episode 27 “The Mysteries of Detection Engineering: Revealed!”. Not just compliance: reimagining DLP for today’s cloud-centric world” [GCP Blog]. Cloud security: “Not the Final Answer on NDR in the Cloud … ”. Move to Cloud: A Chance to Finally Transform Security?”.
Security Boulevard
DECEMBER 20, 2021
Episode 2 “Data Security in the Cloud”. Episode 27 “The Mysteries of Detection Engineering: Revealed!”. Not just compliance: reimagining DLP for today’s cloud-centric world” [GCP Blog]. Cloud security: “Not the Final Answer on NDR in the Cloud … ”. Move to Cloud: A Chance to Finally Transform Security?”.

The Last Watchdog
MAY 30, 2023
Companies can prevent social engineering attacks by steeping employees in cyber hygiene and warning them about the sneaky ways cybercriminals launch cyberattacks. Riccardi: The human factor is the weakest link in cybersecurity, and that’s why cybercriminals zero in on the company’s employees to bypass cybersecurity defenses.

Anton on Security
APRIL 14, 2022
when you think of a center of excellence, say for cloud migration , do you imagine a vast room with blinking lights? When you think that some organization has a center of excellence in cloud security?—?does It is about engineering better detections , but also making the environment support D&R work better.

Anton on Security
JUNE 2, 2023
Yet I reckon that while they play a role in security incidents, they don’t plan an outsized role that cloud misconfigurations do. Similarly, to compromise a modern mobile device, you probably would use social engineering or an exploit, not a configuration weakness. Is Your Fate In the Cloud?” “How

Anton on Security
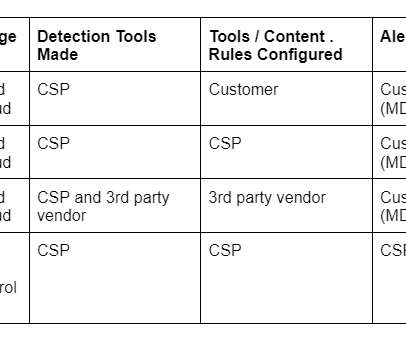
JULY 20, 2022
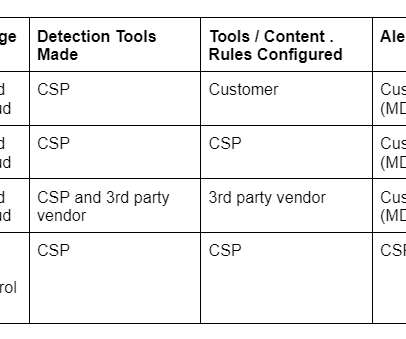
Precise threat model: naturally, customers know their threats best; in theory, this means they can develop the best detections (in practice, many lack detection engineering skills needed) Business / vertical knowledge : similarly, customers also possess superior knowledge of their business, assets, and industry specifics.

Anton on Security
DECEMBER 20, 2021
Cloud Migration Security Woes” “Is Your Fate In the Cloud?” Random fun new posts: “SOC Technology Failures?—?Do Do They Matter?” Kill SOC Toil, Do SOC Eng” “Anton and The Great XDR Debate, Part 1” Fun posts by topic.

Anton on Security
SEPTEMBER 16, 2021
Cloud Migration Security Woes” “Is Your Fate In the Cloud?” Now, posts by topic. Security operations / detection & response: “Security Correlation Then and Now: A Sad Truth About SIEM” “Can We Have “Detection as Code”?” 10X Transformation of the Security Operations Center”” Enjoy!
Security Boulevard
JULY 20, 2022
Precise threat model: naturally, customers know their threats best; in theory, this means they can develop the best detections (in practice, many lack detection engineering skills needed). Move to Cloud: A Chance to Finally Transform Security?”. Cloud Migration Security Woes”. “A Why is Threat Detection Hard?”. “On
Security Boulevard
FEBRUARY 8, 2022
Is Your Fate In the Cloud?”. Move to Cloud: A Chance to Finally Transform Security?”. Cloud Migration Security Woes”. “A A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next”. EP27 The Mysteries of Detection Engineering: Revealed!” (on “On Threat Detection Uncertainty”. “Is

Security Boulevard
JUNE 2, 2023
Yet I reckon that while they play a role in security incidents, they don’t plan an outsized role that cloud misconfigurations do. Similarly, to compromise a modern mobile device, you probably would use social engineering or an exploit, not a configuration weakness. Is Your Fate In the Cloud?” “How

Security Boulevard
APRIL 14, 2022
when you think of a center of excellence, say for cloud migration , do you imagine a vast room with blinking lights? When you think that some organization has a center of excellence in cloud security?—?does It is about engineering better detections , but also making the environment support D&R work better.

Security Boulevard
FEBRUARY 1, 2021
Those team members included Sue McTaggart, Senior Application Security Architect; Bindiya Pradhan, DevOps/Release Engineer II; Vladimir Shuklin, Senior Software Engineer; Yuri Shcherbakov, Senior Software Developer/Software Engineer III; and Clay Corrello, Lead Software Engineer. Bindiya : I???m Clay : I???ve Yuriy : I???ve

Veracode Security
FEBRUARY 1, 2021
Those team members included Sue McTaggart, Senior Application Security Architect; Bindiya Pradhan, DevOps/Release Engineer II; Vladimir Shuklin, Senior Software Engineer; Yuri Shcherbakov, Senior Software Developer/Software Engineer III; and Clay Corrello, Lead Software Engineer. Bindiya : I???m Clay : I???ve Yuriy : I???ve

The Last Watchdog
OCTOBER 17, 2023
SOAR uses the output of detection engines and investigations and recommends workflows or playbooks to build a response plan, saving time and effort. The incorporation of edge networking, cloud migration, and identity and access data is changing how we look at security and its interaction with IT.

Spinone
DECEMBER 26, 2018
Microsoft has engineered Office 365 to allow you to access any Office 365 resources anywhere and from any device, no matter what the platform. Office 365 Lockbox defines how Office 365 support engineers can access your data. Customer Key allows you to control your own encryption keys.

Spinone
JANUARY 14, 2019
Innovation is in Google’s DNA, and by being focused on core business processes, the company has put over a thousand hours of the user experience research engineers into this. Migrating to Team Drives often seems a challenging and critical endeavour, and error prone migrations may cause significant business disruption.

The Last Watchdog
SEPTEMBER 20, 2021
Meanwhile, control system engineers needed a way to assess how well deployed software worked together in the field. This is precisely why there’s a push to develop and implement new cloud-centric security tools and frameworks. Security typically got bolted on, post-deployment.

IT Security Guru
DECEMBER 20, 2023
Mike Newman, CEO of My1Login: Cloud migration will expand the attack surface “In the last year organisations have continued to transform by moving more of their applications and data into the cloud. While this has improved the efficiency and availability of services, it has also expanded the enterprise attack surface.

CyberSecurity Insiders
JUNE 14, 2021
The hackers conducting these attacks are going for the gold – which is why 65% of organizations saw their IT administrators targeted most frequently, followed by engineers and developers (21%) and the C-suite (19%). Zero Trust has been gaining momentum (62% of respondents are familiar with it) as a modern approach to security.

Spinone
JANUARY 27, 2019
Key Factors Driving Migration of Banks and Financial Institutions to the Cloud There are many cloud migration factors in today’s business and customer landscape that are the driving force behind today’s financial institutions deciding to embrace cloud as a major part of their infrastructure.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content