A Deep Dive Into the Residential Proxy Service ‘911’
Krebs on Security
JULY 18, 2022
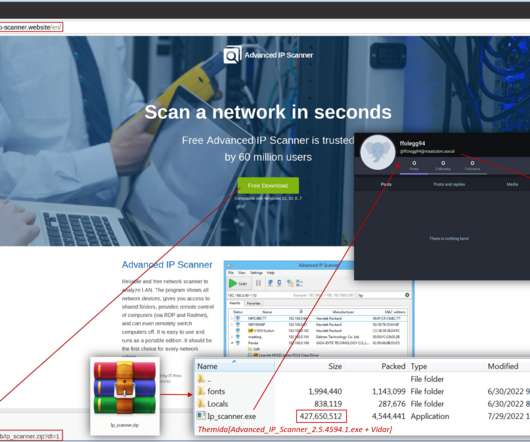
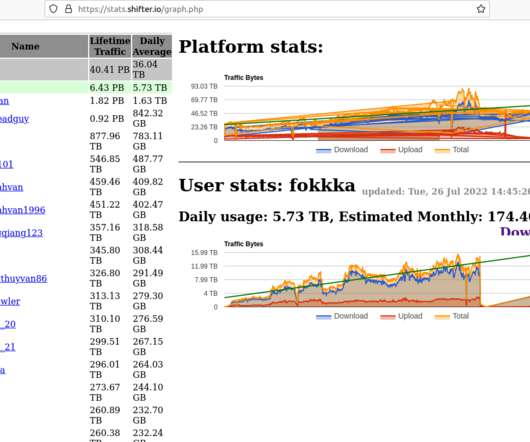
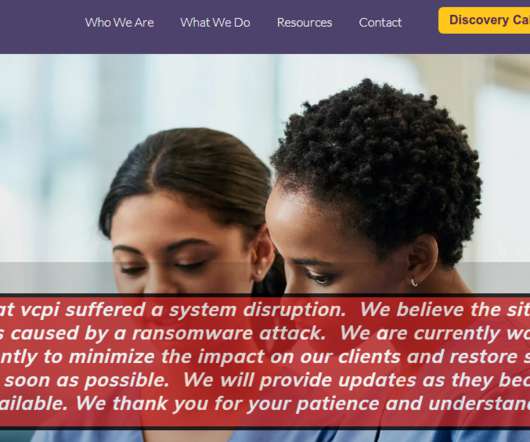
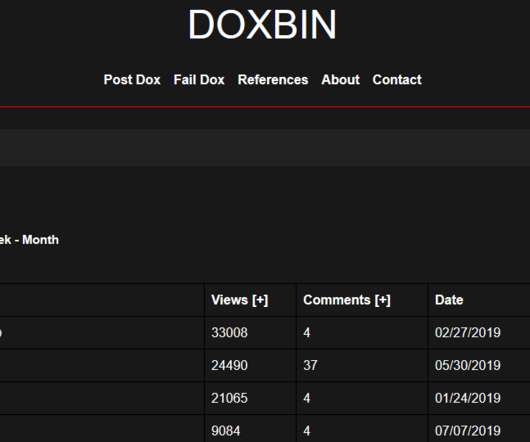
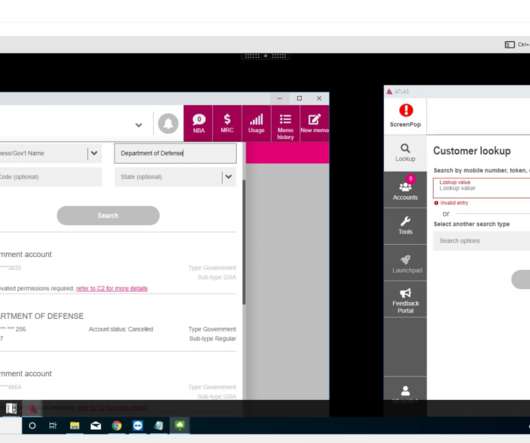
For the past seven years, an online service known as 911 has sold access to hundreds of thousands of Microsoft Windows computers daily, allowing customers to route their Internet traffic through PCs in virtually any country or city around the globe — but predominantly in the United States. “The 911[.]re su between 2016 and 2019.

































Let's personalize your content