Zanubis in motion: Tracing the active evolution of the Android banking malware
SecureList
MAY 28, 2025
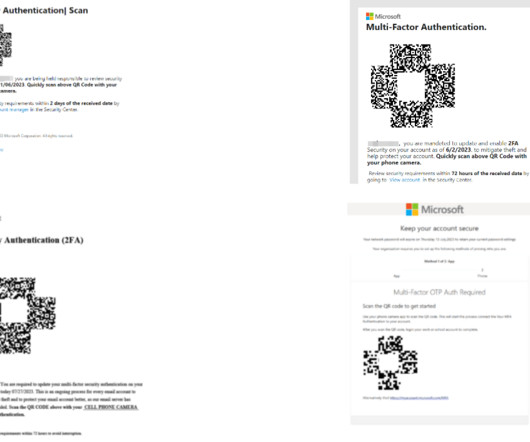
The threat actors behind Zanubis continue to refine its code adding features, switching between encryption algorithms, shifting targets, and tweaking social engineering techniques to accelerate infection rates. The once-broad range of targets, including cryptocurrency wallets, has been abandoned.


























Let's personalize your content