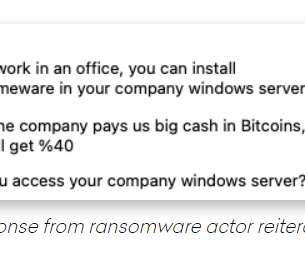
Manual work is better than automated operations, suggests Kaseya Ransomware Attack
CyberSecurity Insiders
JULY 6, 2021
But the Colonial Pipeline cyber attack that took place in May this year and the latest Kaseya Ransomware attack suggests that the need for manual operations is still in demand and those skills can only be got from the veterans generation who are above 50-60 in age.
































Let's personalize your content