5 Misconceptions About Penetration Testing for Mobile Apps
Appknox
AUGUST 7, 2022
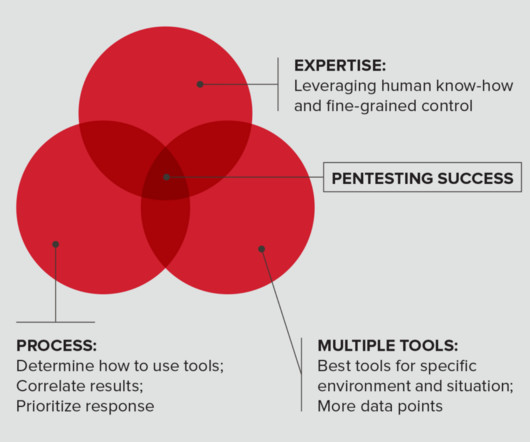
Penetration Testing has become indispensable to most companies' secure software development lifecycle. Unfortunately, because of widespread misconceptions, several businesses still don't understand the true potential of pen testing and refrain from using it to ensure mobile app security. Penetration Testing Overview.












































Let's personalize your content