Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IT Security Guru
MAY 20, 2024
Cybersecurity has never been more critical for businesses. In 2023, an astonishing 50 per cent of companies in the UK reported experiencing some form of cybersecurity breach or attack. Educate and Train Employees Regular training sessions on cybersecurity are crucial for keeping your organisation safe.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Identity IQ
FEBRUARY 8, 2024
How to Spot an Email Phishing Attempt at Work IdentityIQ In the modern workplace, technology is just as common as the typical morning cup of coffee. Among these ever-present threats is phishing, which is a deceptively simple yet effective method cybercriminals use to compromise both business and personal accounts. What Is Phishing?

The Last Watchdog
MAY 2, 2023
The rising complexity and prevalence of cybersecurity threats are making experts anxious. Related: Training employees to mitigate phishing It pressures working analysts to perform 24 hours’ worth of work in an 8-hour day. These feelings are a side effect of cybersecurity burnout.

CyberSecurity Insiders
MAY 28, 2023
In today’s digital landscape, cybersecurity has become a critical concern for individuals and organizations alike. Aspiring cybersecurity researchers often wonder where to start and what areas to explore. By focusing on these areas, newcomers can gain a solid foundation and understanding of cybersecurity principles and practices.
SecureWorld News
JUNE 6, 2023
In our most recent Remote Sessions webcast, Roger Grimes, computer security expert and Data-Driven Defense Evangelist for KnowBe4, gave a deep dive on phishing and how to properly mitigate and prevent phishing attacks. What is phishing? Also known as spamming, phishing is typically done through email, SMS, and phone attacks.

Adam Levin
MARCH 23, 2020
As more employees are working remotely in the wake of the Covid-19 pandemic, businesses are being targeted by an increasing number of phishing campaigns. . Take your time: Phishing scams targeting businesses are often marked urgent and/or time-sensitive, and rely on the target responding too quickly to notice anything suspicious.

CyberSecurity Insiders
JUNE 13, 2023
This article will provide you with a comprehensive guide on how to create cybersecurity awareness and protect yourself and your digital assets from potential threats. Understand the Cybersecurity Landscape: Begin by familiarizing yourself with the current cybersecurity landscape.

Security Boulevard
FEBRUARY 25, 2022
CitiBank is hit with a large-scale phishing campaign, a massive cyber attack has a devastating impact at a logistics giant and a warning for Cisco’s Firepower firewalls customers. The post Cybersecurity News Round-Up: Week of February 21, 2022 appeared first on Security Boulevard.

eSecurity Planet
AUGUST 23, 2023
Spear phishing is a more targeted and effective phishing technique that attempts to exploit specific individuals or groups within an organization. While phishing uses a broader range of tactics, such as mass emailing to random recipients, spear phishing is often well-researched and tailored to high-value targets.

Security Through Education
OCTOBER 27, 2021
That is why, for this October’s Cybersecurity Awareness Month , we encourage you to Do Your Part #BeCyberSmart! Cybersecurity First at Work. Owning your role in cybersecurity can seem cumbersome when approached by someone outside the security industry. Build a Human Firewall. Cybersecurity First at Home.

eSecurity Planet
MARCH 31, 2022
Approximately 83 percent of organizations said they faced a successful phishing attempt in 2021, up from 57 percent in 2020. This guide breaks down the different types of phishing attacks and provides examples to help organizations better prepare their staff to deal with them. What is Phishing? Spear Phishing.

CyberSecurity Insiders
NOVEMBER 1, 2021
Adopting and applying cybersecurity principles can help you secure your company and decrease the danger of a data breach. Since phishing attempts infect an individual’s system with malware, spyware, or viruses, it’s critical to use dedicated programs installed on all gadgets and throughout your system.

CyberSecurity Insiders
JANUARY 11, 2022
Next-generation firewalls from Palo Alto Networks with AT&T Multi-Access Edge Computing (MEC) solutions are designed to help protect enterprises while optimizing security performance for these new use cases. They also help reduce complexity by assisting the customer with ongoing configuration changes to their firewall policies.
Security Boulevard
DECEMBER 1, 2023
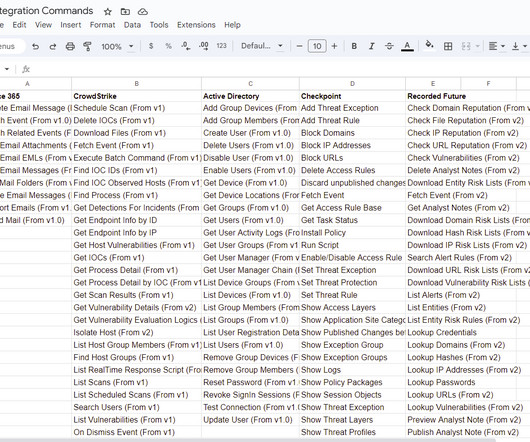
Automating response to phishing attacks remains one of the core use-cases of SOAR platforms. In 2022, the Anti-Phishing Working Group (APWG) logged ~4.7 million phishing attacks. Since 2019, the number of phishing attacks has increased by more than 150% yearly.

SecureWorld News
JANUARY 21, 2024
Battling cybersecurity threats can often feel like an uphill struggle. Let's take a closer look at some key cybersecurity strategies for nonprofits to consider. Let's take a closer look at some key cybersecurity strategies for nonprofits to consider.

The Last Watchdog
MARCH 21, 2023
The cybersecurity landscape is constantly changing. While it might seem like throwing more money into the IT fund or paying to hire cybersecurity professionals are good ideas, they might not pay off in the long run. However, organizations in 2023 know one crucial area to spend money n is cybersecurity.

SecureWorld News
JANUARY 11, 2024
In an interview with SecureWorld News , Arun DeSouza shares his insights on the challenges and emerging trends in the cybersecurity sector and modern ways to adapt to the changing business landscape. What developments in the security landscape have sparked your enthusiasm, and how does it impact the future of cybersecurity?

eSecurity Planet
FEBRUARY 11, 2022
As data and IT infrastructure become more valuable by the day, cybersecurity risk management is increasingly important for enterprises with a steep cost for noncompliance or extensive, unaddressed vulnerabilities. What is Cybersecurity Risk Management? What IT Assets Need Protection? Maintaining Regulatory Compliance.

SiteLock
AUGUST 27, 2021
In the world of cybersecurity, the looming menace of advanced persistent threats and state-sponsored attack groups tend to dominate the headlines. However, research indicates that phishing attacks are the most common threat — by far. To avoid becoming a victim, it’s critical to prevent phishing attacks.

eSecurity Planet
MAY 6, 2021
Web application firewalls (WAFs) are a critical component for robust application security. At the same time, WAF technology is increasingly a part of more comprehensive security solutions like next-generation firewalls (NGFW), unified threat management (UTM), and more. Best Web Application Firewalls (WAFs). Amazon Web Services.

SiteLock
AUGUST 27, 2021
In the age of data, with organizations creating trillions of gigabytes of new information each year, it’s easy to think of cybersecurity as a mere synonym for “data protection.” But cybersecurity is so much more. The cybersecurity stakes are higher than ever and growing by the day. How does cybersecurity protect the tech stack?

CyberSecurity Insiders
MARCH 10, 2021
Check all Senders: Phishing attacks are one of the most common ways that cybercriminals will access a small business’s systems. Most of the time, phishing attacks are very subtle and can easily be mistaken for an email that has come from a reputable source such as the business bank, a top client, or even the CEO.

Security Boulevard
JUNE 1, 2022
There are many common perceptions about cybersecurity – but many are mis perceptions. For small and mid-sized businesses (SMBs), misinformation about cybersecurity can be confusing – and sometimes risky. Fiction: Outsourcing cybersecurity is not a realistic option for SMBs. Outsourcing cybersecurity is a great option for SMBs.

CyberSecurity Insiders
MARCH 31, 2022
It can be easy to understand then, that cybersecurity may not have been a huge priority for businesses . Another major element of the cybersecurity crisis is the fact that so many people are now working from home. Many in-office workers are used to doing their job with a degree of simplicity with regards to cybersecurity.

Security Boulevard
MARCH 3, 2023
Malvertising Enters a New Age While Google grapples with the potential threat that ChatGPT poses to its advertising business, cybercriminals are taking advantage of Google Ads to ramp up their phishing attacks on unsuspecting victims. Your firewall had no problems letting the requested HTTPS traffic through.

The Last Watchdog
MARCH 6, 2021
Your employers might be able to provide you with specific directions on how to handle certain aspects of your cybersecurity. Here are some cybersecurity best practices tips that apply more than ever when it comes to remote workers carrying out their duties securely. Set up firewalls. Keep an eye out for phishing emails.

SecureWorld News
OCTOBER 19, 2023
Global inflation can have, and is having, a significant impact on cybersecurity. As prices rise, organizations may be tempted to cut back on cybersecurity spending, making them more vulnerable to cyberattacks. Additionally, inflation can make it more difficult for organizations to keep up with the latest cybersecurity threats.

SecureWorld News
NOVEMBER 28, 2023
Whether applied to firewall rules or code execution permissions, Default Permit operates on the flawed assumption that allowing everything except known threats is a sound strategy. Users' susceptibility to phishing attacks and social engineering tactics remains a persistent challenge.
IT Security Guru
DECEMBER 1, 2022
As our digital world evolves, cybersecurity has never been more important and critical. As cybercrime continues to increase, the human element can play the most important role in cybersecurity posture and hygiene. After all, cybersecurity is a matter of proper human risk management. Armed Forces are an exemplary example.

SC Magazine
APRIL 22, 2021
On April 22, cybersecurity training and awareness company KnowBe4 launched an initial public offering, opening up sales of company stock to the public starting at $16 a share (that increased to just over $24 by the closing bell). You can’t send a Bank of America phishing attack in France. A group shot of the KnowBe4 team.

SiteLock
AUGUST 27, 2021
Cybersecurity threats aren’t going away anytime soon. Having an incident response plan to address several different cybersecurity threats and safety measures is an important step in this process. What Is Incident Response in Cybersecurity? Common Cybersecurity Threats. The good news? This type of attack is on the rise.

SiteLock
AUGUST 27, 2021
It’s safe to say that the volume and magnitude of high-profile data breaches and ransomware attacks that punctuated 2019 really kept the cybersecurity industry on its toes. We’ve analyzed the current state of the industry and packaged up our top five cybersecurity predictions for 2020. In comparison to last year, research.

Responsible Cyber
APRIL 8, 2020
Small and mid-sized enterprises (SMEs) are increasingly at risk of cyber-attacks, and often serve as a launch pad for larger threat campaigns, according to Cisco’s 2018 SMB Cybersecurity Report. Humans remain the biggest and most common cybersecurity threat to businesses of all sizes. Phishing and Spear Phishing.

The Last Watchdog
SEPTEMBER 27, 2021
Phishing scams, malware, ransomware and data breaches are just some of the examples of cyberthreats that can devastate business operations and the protection of consumer information. Here are five notable historical events that influenced cybersecurity assessment and transformed it into what it is today: The Battle of Midway (1942).

BH Consulting
JUNE 2, 2022
Job Title: (Technical) Cybersecurity Consultant. BH Consulting is an ever-expanding cybersecurity and data protection consulting service – with offices in Dublin, London and New York. Familiarity with security standards and frameworks e.g., ISO 27001, NIST Cybersecurity Framework, CIS Critical Security Controls.

GlobalSign
FEBRUARY 25, 2022
CitiBank is hit with a large-scale phishing campaign, a massive cyber attack has a devastating impact at a logistics giant and a warning for Cisco’s Firepower firewalls customers

CyberSecurity Insiders
SEPTEMBER 24, 2021
From phishing attacks to ransomware attacks, business owners need to be adequately prepared to prevent further damage. . This article discusses top areas in IT where you need to strengthen cybersecurity measures to avoid data breaches and information loss: Networks. Human Resources. Businesses require the input of human resources.

Digital Shadows
AUGUST 17, 2021
What is Phish(ing)? But, never mind the dozens of other reports and white papers about phishing that come out every year from security industry leaders, let’s take a look at the 2021 Verizon DBIR. Why should I care about Phish? The reason why phishing is still reigning supreme?

Cytelligence
MAY 24, 2023
Here are seven best practices for cybersecurity in small businesses: Employee Education and Training: Provide cybersecurity awareness training to your employees, teaching them about common threats such as phishing emails, social engineering, and the importance of strong passwords. WPA2 or WPA3).

eSecurity Planet
JUNE 16, 2022
However, basic cybersecurity tools and practices, like patching , strong passwords , and multi-factor authentication (MFA), “can prevent 80 to 90% of cyberattacks,” said Anne Neuberger, deputy national security advisor for cyber and emerging technologies, during a White House press conference in Sept. The average cost of a breach is $3.6

CyberSecurity Insiders
FEBRUARY 22, 2022
Trickbot Malware distribution is carried out via malicious macros spread done through phishing emails and is also found operating as an espionage software sometimes. And prima facie revealed that an email phishing campaign led to the spread of Emotet Trojan that then paved way for TrickBot, leading to the download of RYUK. .

IT Security Guru
FEBRUARY 13, 2023
With so many well known banking sites falling short when it comes to blocking fraudsters, cybersecurity experts at VPNOverview have compiled a list of 12 safety tips to keep your money safe from malware and phishing scams. What are the possible dangers of online banking?
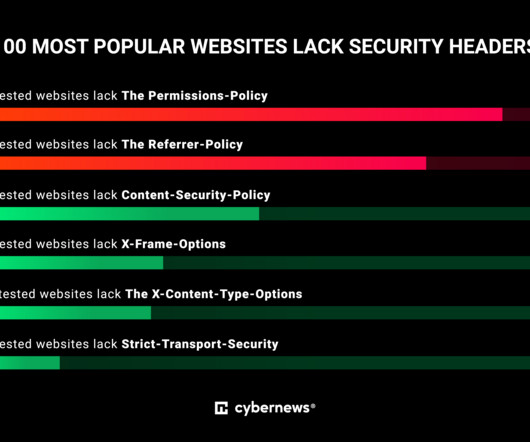
Security Affairs
AUGUST 17, 2023
The world’s most popular websites lack basic cybersecurity hygiene, an investigation by Cybernews shows. Often ignored by developers, HTTP security headers are good firewalls that can prevent a lot of common vulnerabilities from being exploited. Do you happen to love exploring DIY ideas on Pinterest?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content