Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
The Hacker News
MAY 27, 2024
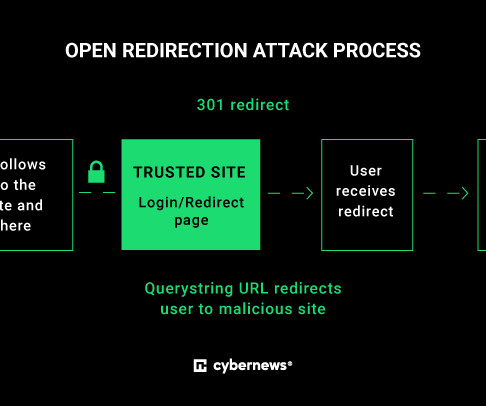
The transition to the cloud, poor password hygiene and the evolution in webpage technologies have all enabled the rise in phishing attacks. But despite sincere efforts by security stakeholders to mitigate them - through email protection, firewall rules and employee education - phishing attacks are still a very risky attack vector.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
DECEMBER 15, 2023
Security flaws in Netgate pfSense firewall solution can potentially lead to arbitrary code execution on vulnerable devices. pfSense is a popular open-source firewall solution maintained by Netgate, researchers discovered multiple security issues affecting it. ” reads the analysis published by SonarSource. and pfSense Plus 23.09.
The Hacker News
MARCH 28, 2024
A sophisticated phishing-as-a-service (PhaaS) platform called Darcula has set its sights on organizations in over 100 countries by leveraging a massive network of more than 20,000 counterfeit domains to help cyber criminals launch attacks at scale.

Identity IQ
FEBRUARY 8, 2024
How to Spot an Email Phishing Attempt at Work IdentityIQ In the modern workplace, technology is just as common as the typical morning cup of coffee. Among these ever-present threats is phishing, which is a deceptively simple yet effective method cybercriminals use to compromise both business and personal accounts. What Is Phishing?
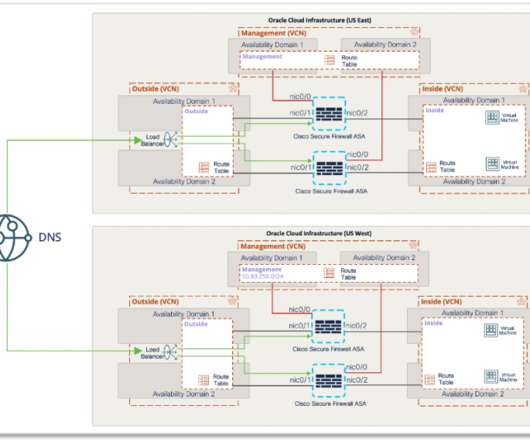
Cisco Security
JULY 9, 2021
With Cisco Secure Firewall, organizations are able to build a scalable RAVPN architecture on OCI, providing employees secure remote access to their organization’s resources from any location or endpoint. It enforces security at the DNS layer to block malware, phishing, and command and control callbacks over any port.
SecureWorld News
JUNE 6, 2023
In our most recent Remote Sessions webcast, Roger Grimes, computer security expert and Data-Driven Defense Evangelist for KnowBe4, gave a deep dive on phishing and how to properly mitigate and prevent phishing attacks. What is phishing? Also known as spamming, phishing is typically done through email, SMS, and phone attacks.

SecureWorld News
OCTOBER 30, 2023
When it comes to impactful types of internet-borne crime, phishing is the name of the game. According to Verizon's 2023 Data Breach Investigations Report (DBIR), a whopping 74% of breaches involve a human element, which is exactly what phishing aims to exploit. And for good reason. Tactics matter a lot, too.

Adam Levin
MARCH 23, 2020
As more employees are working remotely in the wake of the Covid-19 pandemic, businesses are being targeted by an increasing number of phishing campaigns. . Take your time: Phishing scams targeting businesses are often marked urgent and/or time-sensitive, and rely on the target responding too quickly to notice anything suspicious.

eSecurity Planet
AUGUST 23, 2023
Spear phishing is a more targeted and effective phishing technique that attempts to exploit specific individuals or groups within an organization. While phishing uses a broader range of tactics, such as mass emailing to random recipients, spear phishing is often well-researched and tailored to high-value targets.
Security Affairs
FEBRUARY 16, 2021
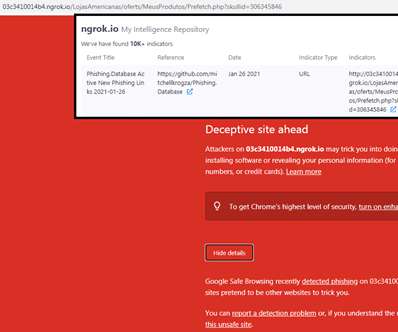
Researchers from threat intelligence Cyble have discovered threat actors abusing the Ngrok platform in a fresh phishing campaign. Researchers at the threat intelligence firm Cyble discovered a new wave of phishing attacks targeting multiple organizations that are abusing the ngrok platform, a secure and introspectable tunnel to the localhost.
Security Boulevard
DECEMBER 1, 2023
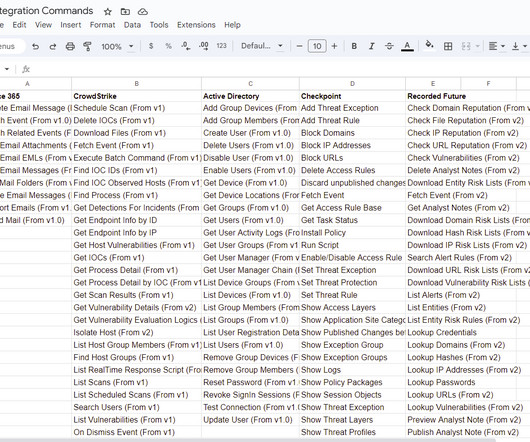
Automating response to phishing attacks remains one of the core use-cases of SOAR platforms. In 2022, the Anti-Phishing Working Group (APWG) logged ~4.7 million phishing attacks. Since 2019, the number of phishing attacks has increased by more than 150% yearly.

eSecurity Planet
MARCH 31, 2022
Approximately 83 percent of organizations said they faced a successful phishing attempt in 2021, up from 57 percent in 2020. This guide breaks down the different types of phishing attacks and provides examples to help organizations better prepare their staff to deal with them. What is Phishing? Spear Phishing.
Security Affairs
NOVEMBER 12, 2021
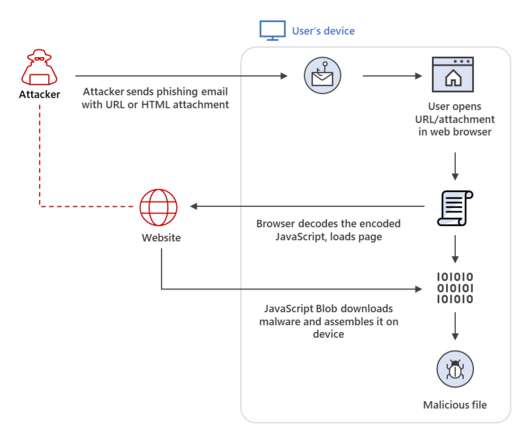
Threat actors are increasingly using the HTML smuggling technique in phishing campaigns, Microsoft researchers warn. Microsoft experts warn that threat actors are increasingly using the HTML smuggling technique in phishing campaigns to stealthily deliver threats. SecurityAffairs – hacking, phishing). Pierluigi Paganini.

Tech Republic Security
JULY 19, 2017
Leon Kuperman, CTO of CUJO IoT Security, why your small business and home office needs a firewall, and why your ISP can't protect you from bad IPs, phishing links, and sites loaded with malware.

SiteLock
AUGUST 27, 2021
However, research indicates that phishing attacks are the most common threat — by far. Microsoft’s “ Security Intelligence Report, Volume 24 ” shows a 250% increase in the number of phishing emails and attacks since 2018. To avoid becoming a victim, it’s critical to prevent phishing attacks. Pick a Strong Password Manager.

CyberSecurity Insiders
JANUARY 11, 2022
Next-generation firewalls from Palo Alto Networks with AT&T Multi-Access Edge Computing (MEC) solutions are designed to help protect enterprises while optimizing security performance for these new use cases. They also help reduce complexity by assisting the customer with ongoing configuration changes to their firewall policies.

eSecurity Planet
MAY 6, 2021
Web application firewalls (WAFs) are a critical component for robust application security. At the same time, WAF technology is increasingly a part of more comprehensive security solutions like next-generation firewalls (NGFW), unified threat management (UTM), and more. Best Web Application Firewalls (WAFs). Amazon Web Services.
SiteLock
AUGUST 27, 2021
In this week’s post, we take a look at “in-the-wild” phishing attacks and talk about how to protect against a phishing attack and how to counter them. Phishing Attack Examples. Here are two examples of phishing attacks that were carried out. Data URI and phishing page. We don’t want that. Malicious VBScript.

Security Boulevard
MARCH 3, 2023
Malvertising Enters a New Age While Google grapples with the potential threat that ChatGPT poses to its advertising business, cybercriminals are taking advantage of Google Ads to ramp up their phishing attacks on unsuspecting victims. Your firewall had no problems letting the requested HTTPS traffic through.

SC Magazine
APRIL 22, 2021
And on the change from international expansion: our business is unique in that it’s not just translating phishing attacks to different languages. You can’t send a Bank of America phishing attack in France. So we pour in a huge amount of resources to get all our core modules and related collateral, like phishing in 34 languages.
The Hacker News
APRIL 1, 2021
In 2020, hospitals, retirement communities, and medical centers bore the brunt of an ever-shifting phishing campaign that distributed custom backdoors such as KEGTAP, which ultimately paved the way for RYUK

Adam Levin
MARCH 23, 2020
You can also create an extra firewall by configuring your router to block unwanted incoming internet traffic. Beware of Phishing Links: Phishing scams are on the rise. Confirm requests for data or personal information with a quick phone call to protect against spear phishing.

The Last Watchdog
MARCH 6, 2021
Set up firewalls. Firewalls act as a defense line in preventing the possibility of threats entering your system. Firewalls create a barrier between the device and the internet by closing the ports to communication, preventing malicious programs from entering networks, and stopping a potential data breach on your device.

Digital Shadows
AUGUST 17, 2021
What is Phish(ing)? But, never mind the dozens of other reports and white papers about phishing that come out every year from security industry leaders, let’s take a look at the 2021 Verizon DBIR. Why should I care about Phish? The reason why phishing is still reigning supreme?

CSO Magazine
MARCH 16, 2022
Cloudflare is bolstering its suite of web infrastructure and security offerings with a free WAF (web application firewall) managed ruleset service, a new API management gateway, and — once it closes its recently announced acquisition of Area 1 Security — a set of email tools designed to thwart phishing and malware attacks.

Security Boulevard
FEBRUARY 25, 2022
CitiBank is hit with a large-scale phishing campaign, a massive cyber attack has a devastating impact at a logistics giant and a warning for Cisco’s Firepower firewalls customers. The post Cybersecurity News Round-Up: Week of February 21, 2022 appeared first on Security Boulevard.

Tech Republic Security
JUNE 30, 2023
Get VPN, Firewall and SmartDNS protection in one package! Combining five top-rated security apps, the MonoDefense Security Suite offers complete protection — and lifetime subscriptions are now 62% off. The post Protect Your Data With the MonoDefense Security Suite for $149.99 appeared first on TechRepublic.

The Last Watchdog
MAY 2, 2023
Related: Training employees to mitigate phishing It pressures working analysts to perform 24 hours’ worth of work in an 8-hour day. Experts must monitor firewalls, test business continuity plans and identify vulnerabilities with seemingly little payoff. An increasingly digitized world means analysts can’t rest.

CyberSecurity Insiders
FEBRUARY 22, 2022
Trickbot Malware distribution is carried out via malicious macros spread done through phishing emails and is also found operating as an espionage software sometimes. And prima facie revealed that an email phishing campaign led to the spread of Emotet Trojan that then paved way for TrickBot, leading to the download of RYUK. .

Cisco Security
AUGUST 12, 2021
This requires a robust connection to the Internet (Lumen and Gigamon), firewall protection (Palo Alto Networks), segmented wireless network (Commscope Ruckus) and network full packet capture & forensics and SIEM (RSA NetWitness); with Cisco providing cloud-based security and intelligence support. SECURITY CATEGORY (PHISHING).

Hacker Combat
APRIL 22, 2022
Even if the attachment is from a trusted source, ensure that you run it through anti-phishing software before opening it. #2 5 Make use of windows firewall. Windows firewall protects your computer from malicious attacks by controlling who has access to your network. 2 Backup your data. 6 Use strong spam filters.

Adam Levin
APRIL 15, 2020
Hospitals have been targeted by ransomware (despite initial assurances to the contrary), phishing scams are using pandemic-related scare tactics, and video conferencing apps have become the new go-to for everything from domain-spoofing attacks to zoombombing. Even NASA has reported a 100% increase in phishing and malware attacks. .

GlobalSign
FEBRUARY 25, 2022
CitiBank is hit with a large-scale phishing campaign, a massive cyber attack has a devastating impact at a logistics giant and a warning for Cisco’s Firepower firewalls customers

eSecurity Planet
DECEMBER 10, 2023
Firewalls monitor and control incoming and outgoing traffic while also preventing unauthorized access. Overlapping rules may impair firewall efficiency or expose flaws that allow attackers to circumvent regulations. Choose a centralized platform that is interoperable with several firewall suppliers.
Security Affairs
JANUARY 3, 2024
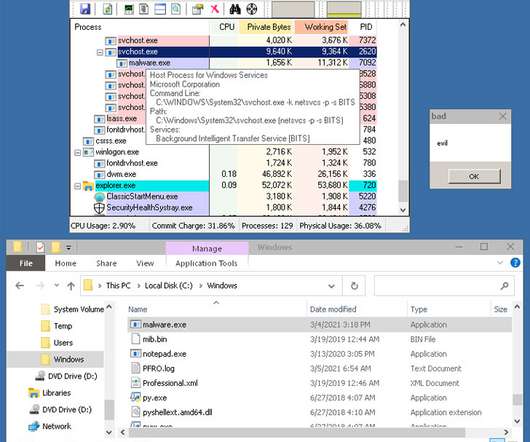
They were used to access the internal workplace systems for BMW dealers and could have been useful to attackers for spear-phishing campaigns or malware distribution. The firewall won’t block the malicious link in an email as the domain is legitimate. Imagine you get an email from your CEO or manager asking you to do something.
Security Affairs
SEPTEMBER 26, 2022
A China-linked cyberespionage group, tracked as TA413 (aka LuckyCat) , is exploiting recently disclosed flaws in Sophos Firewall (CVE-2022-1040) and Microsoft Office ( CVE-2022-30190 ) to deploy a never-before-detected backdoor called LOWZERO in attacks aimed at Tibetan entities. in Microsoft Office in attacks in the wild.

eSecurity Planet
JUNE 16, 2022
Cisco Umbrella , analyzing the threat environment for 2022, found that 86% of organizations experienced phishing, 69% experienced unsolicited crypto mining, 50% were affected by ransomware, and 48% experienced some form of information-stealing malware. Phishing attacks continue to dominate cyber threats. Firewalls have come a long way.

Cisco Security
FEBRUARY 15, 2022
Umbrella prevents phishing, malware, and ransomware anywhere users go – from the headquarters, to branch offices, to remote locations. Cisco Secure Firewall – Today’s more complex environments require a firewall that can keep up. It also safeguards connections to cloud applications without sacrificing performance.

Webroot
APRIL 13, 2021
This includes essential security measures like firewalls, endpoint protection and DNS protection. And, since even firewalls can be circumvented, it means keeping backups of all business data so you never have to pay a ransom to get your data back. Attacks like BEC are less about malware and more about manipulating people.

Security Affairs
APRIL 28, 2024
A credential stuffing attack is a type of cyber attack where hackers use large sets of username and password combinations, typically obtained from previous data breaches, phishing campaigns, or info-stealer infections, to gain unauthorized access to user accounts on various online services.

CyberSecurity Insiders
MAY 28, 2023
Network Security: Study network protocols, such as TCP/IP, and analyze common network attacks like DDoS, phishing, and man-in-the-middle attacks. Research network security mechanisms, such as firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs).

IT Security Guru
MAY 12, 2024
Employ Firewalls Firewalls act as a barrier between your website and potential attackers, especially if you work in industries that carry a lot of sensitive data including large corporations, insurance firms, medical practices and companies that offer bad credit loans.

CyberSecurity Insiders
NOVEMBER 1, 2021
Since phishing attempts infect an individual’s system with malware, spyware, or viruses, it’s critical to use dedicated programs installed on all gadgets and throughout your system. Enact robust data security processes and firewalls. Implementing local firewalls is another good way to give that extra layer of security.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content