Mastering NIST Penetration Testing: Your Essential Guide to Robust Cybersecurity
Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.

eSecurity Planet
JUNE 23, 2023
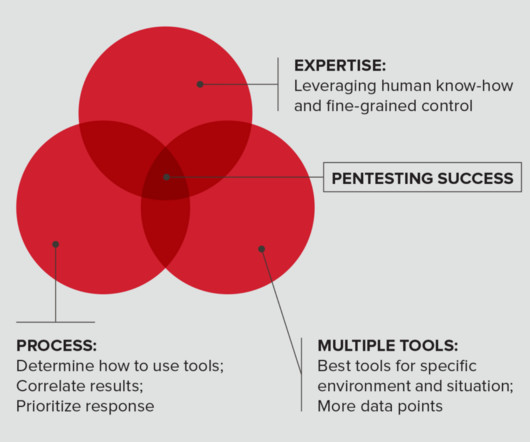
All organizations should perform penetration tests, yet many worry about not receiving the full value of their investment. Organizations have two choices: perform penetration tests with their internal teams, or hire an external vendor and find ways to lower costs.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
FEBRUARY 25, 2022
Many cybersecurity audits now ask whether penetration testing is conducted and how vulnerabilities are detected and tracked. These questions ask IT teams to consider how frequently security is tested from the outside via penetration testing and from the inside via vulnerability testing.

eSecurity Planet
JUNE 28, 2023
Penetration tests are vital components of vulnerability management programs. In these tests, white hat hackers try to find and exploit vulnerabilities in your systems to help you stay one step ahead of cyberattackers. Here we’ll discuss penetration testing types, methods, and determining which tests to run.

The Last Watchdog
FEBRUARY 24, 2022
Let us run you through the various aspects of penetration testing, or pen test, and why it is a critical component to protect a company’s network. A pen test is a simulated cyber attack on your systems to identify the loopholes that hackers can exploit. I am sure you do care for your site and digital assets.

eSecurity Planet
OCTOBER 23, 2022
Organizations use penetration testing to strengthen their security. During these tests, simulated attacks are executed to identify gaps and vulnerabilities in the IT environment. Penetration testing can use different techniques, tools, and methods. See the Best Penetration Testing Tools.

CyberSecurity Insiders
JANUARY 28, 2022
For many businesses, penetration testing is an important part of their security protocol. In order to build a reputation and gain their customer’s trust, they need to ensure that they are secure against any risks that the digital realm may pose. Why is penetration testing important? Duration of the test.

Penetration Testing
MARCH 10, 2024
... The post Canva Uncovers Critical Font Vulnerabilities, Exposes Cybersecurity Risks appeared first on Penetration Testing. The company’s investigation revealed three previously unknown vulnerabilities (CVEs) in popular tools used for font processing and manipulation....

eSecurity Planet
MARCH 7, 2023
Penetration tests are simulated cyber attacks executed by white hat hackers on systems and networks. There are different types of penetration tests, methodologies and best practices that need to be followed for optimal results, and we’ll cover those here. However, they are also the most realistic tests.

Mitnick Security
APRIL 4, 2023
If you want to see how your organization would stack up against threat actors, there is a way to do so without risking a data breach. Red Team vs. Blue Team penetration testing is a safe way to identify vulnerabilities within your systems, networks, and internal infrastructure. But it doesn’t stop there.
Penetration Testing
APRIL 16, 2024
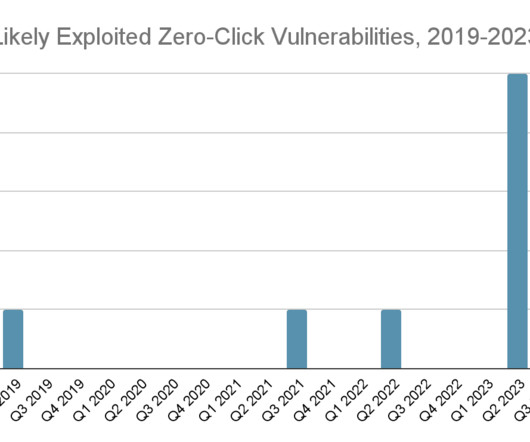
According to a detailed report by Recorded Future’s Insikt Group, the cybersecurity landscape faces a formidable threat in the form of “Mobile NotPetya,” a potential zero-click, wormable mobile malware that could spread autonomously and... The post Unstoppable Malware?

Mitnick Security
MARCH 15, 2023
Penetration tests are an extremely useful exercise to mitigate risks and patch your security gaps. If you’ve been asking yourself why do penetration testing more than once, look no further than the pentest report for your answer.
eSecurity Planet
APRIL 7, 2023
Kali Linux turns 10 this year, and to celebrate, the Linux penetration testing distribution has added defensive security tools to its arsenal of open-source security tools. Also read: 24 Top Open Source Penetration Testing Tools What Is Penetration Testing? Watch this tutorial by Hackersploit to learn more.

Penetration Testing
NOVEMBER 26, 2023
The paper, titled “The Internet of Insecure Cows – A Security Analysis of Wireless Smart Devices Used for Dairy Farming,” authored by Samuel Barnes-Thornton, Joseph Gardiner, and Awais Rashid of the University of Bristol,... The post Cybersecurity Risks in Smart Dairy Farming appeared first on Penetration Testing.

eSecurity Planet
FEBRUARY 20, 2023
Penetration tests find security vulnerabilities before hackers do and are critical for keeping organizations safe from cyber threats. Penetration test services have become common, with many security companies offering them. The program answers what, when, why, and where tests should run.

Security Boulevard
APRIL 29, 2021
A Vulnerability Scan Or A Penetration Test? Vulnerability scanning and penetration tests are two very different ways to test your system for any vulnerabilities. In a brief summary, a vulnerability scan is an automated, high-level test that looks for and reports potential vulnerabilities in your system.

Penetration Testing
JANUARY 7, 2024
In the rapidly evolving world of cybersecurity, staying ahead of threats is a daunting task for organizations across the globe.

CyberSecurity Insiders
JUNE 3, 2021
Businesses are venturing into using automated penetration testing to replace or complement their conventional cyber threat assessments. It’s no surprise, considering how time-consuming and tedious running manual pen tests can be. But first… What is automated penetration testing?

Pen Test
OCTOBER 12, 2023
Introduction Radio Frequency (RF) penetration testing, popularly referred to as RF pentesting, stands as a vital domain within ethical hacking. In the contemporary digital era, Radio Frequency (RF) penetration testing, commonly known as RF pentesting, is indispensable due to several pivotal factors that underscore its significance.

The Last Watchdog
JANUARY 2, 2024
In today’s digital landscape, organizations face numerous challenges when it comes to mitigating cyber risks. Here are some of the key challenges that organizations encounter in their efforts to mitigate cyber risks in the current environment. Inadequate security testing. Lack of security awareness and education.

Penetration Testing
MARCH 24, 2024
A bombshell discovery from top-tier cybersecurity researchers has unveiled a critical vulnerability affecting the heart of both Apple and Intel processors.

Mitnick Security
JUNE 27, 2023
As a Chief Information Security Officer (CISO), you have the responsibility of not only directing your organization’s security but also conveying your risk status to leadership. According to Cybersecurity Magazine, 60% of small businesses go out of business within six months of falling victim to a data breach or cyber attack.

Thales Cloud Protection & Licensing
MARCH 8, 2023
Your Cannot Secure Your Data by Network Penetration Testing divya Thu, 03/09/2023 - 06:05 Organisations continue to experience serious data breaches, often causing harm to their customers, society, and their hard-earned reputations. The reason was that the cybersecurity team had told the business leadership team that the data was safe.

CyberSecurity Insiders
MAY 3, 2023
Penetration testing (pentesting) is one of the fundamental mechanisms in this area. This method is an extremely important prerequisite for maintaining OT cybersecurity , an emerging area geared toward safeguarding industrial control systems (ICS) at the core of critical infrastructure entities.

Penetration Testing
JANUARY 17, 2024
Shopware, an open-source ecommerce platform that helps businesses of all sizes create and manage their online stores, recently found itself in the cybersecurity spotlight.

The Last Watchdog
FEBRUARY 20, 2024
While AI chatbots have cybersecurity vulnerabilities, adopting proactive measures like secure development practices and regular assessments can effectively mitigate risks. About the essayist: Zac Amos writes about cybersecurity and the tech industry, and he is the Features Editor at ReHack.

Penetration Testing
NOVEMBER 14, 2023
The United States Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning to federal agencies about the necessity of bolstering the security of Juniper devices within their networks.

Malwarebytes
JUNE 1, 2021
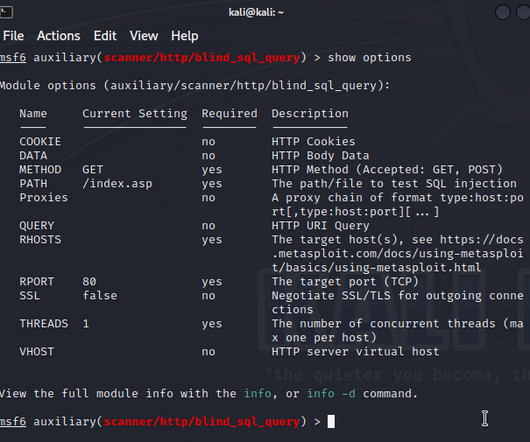
Metasploit—probably the best known project for penetration testing—is an exploit framework, designed to make it easy for someone to launch an exploit against a particular vulnerable target. The need for pen-testing. Maybe only Metasploit could give it a run for the first place ranking. What is Cobalt Strike?

eSecurity Planet
APRIL 29, 2024
Integrated risk management (IRM) is a discipline designed to embed risk considerations for the use of technology throughout an organization. In other words, it links technology spending directly to the value of the resource protected and the associated risks controlled by that technology.

IT Security Guru
JANUARY 26, 2024
Nevertheless, the development of IoT and fleet management systems brings up issues with cybersecurity risks. With this in mind, it is crucial for organizations to understand the possible implications of cybersecurity breaches in fleet management systems and take proactive actions to circumvent these risks.

The Last Watchdog
NOVEMBER 1, 2023
1, 2023 — AdviserCyber , a cybersecurity service provider for Registered Investment Advisers (RIAs) with $500M to $3B Assets Under Management (AUM) who must comply with the Securities and Exchange Commission (SEC) cybersecurity requirements, announced its formal launch today. Phoenix, Ariz. —

CyberSecurity Insiders
MAY 28, 2023
In today’s digital landscape, cybersecurity has become a critical concern for individuals and organizations alike. Aspiring cybersecurity researchers often wonder where to start and what areas to explore. By focusing on these areas, newcomers can gain a solid foundation and understanding of cybersecurity principles and practices.

NopSec
AUGUST 9, 2022
Once you’ve started a vulnerability scanning system , you may want to take the next step in identifying vulnerabilities: penetration testing, commonly referred to as pentesting. The Basics of Penetration Testing Pentesting can be as broad or narrow as the client wishes. This more closely simulates an actual cyber attack.

eSecurity Planet
OCTOBER 31, 2023
A penetration testing report discloses the vulnerabilities discovered during a penetration test to the client. Penetration test reports deliver the only tangible evidence of the pentest process and must deliver value for a broad range of readers and purposes.

The Last Watchdog
FEBRUARY 8, 2024
Together, the companies are empowering AV and media companies to improve their cybersecurity stance by providing a “clean bill of health” for their digital media environments, ensuring hardware and software are current, and protecting media storage and devices against the threat of malware. Kenilworth, NJ, Feb. Vulnerability management.
NetSpi Executives
APRIL 27, 2024
Table of Contents What is penetration testing? How penetration testing is done How to choose a penetration testing company How NetSPI can help Penetration testing enables IT security teams to demonstrate and improve security in networks, applications, the cloud, hosts, and physical locations.

The Last Watchdog
JULY 11, 2023
Conduct regular penetration testing. Regular and thorough penetration testing is crucial for identifying vulnerabilities within trading systems. Having access to a partner focused in cybersecurity brings fresh perspectives and allows for an unbiased evaluation of the systems in use.

Penetration Testing
DECEMBER 27, 2023
In a digital landscape increasingly dotted with sophisticated surveillance solutions, the discovery of a critical vulnerability in QNAP’s VioStor Network Video Recorder (NVR) devices serves as a stark reminder of the ever-present cybersecurity risks....

eSecurity Planet
JULY 5, 2023
A pentest framework, or penetration testing framework, is a standardized set of guidelines and suggested tools for structuring and conducting effective pentests across different networks and security environments. However, pentests are used for a variety of reasons, and pentest frameworks have a few different use cases as well.

Penetration Testing
DECEMBER 19, 2023
Apache Superset, a cutting-edge business intelligence web application, has recently been under the cybersecurity spotlight due to three significant vulnerabilities.

Penetration Testing
DECEMBER 5, 2023
In the constantly evolving domain of cybersecurity, a new vulnerability has surfaced, striking at the heart of Atos Unify’s OpenScape products.

Security Boulevard
AUGUST 12, 2022
Penetration testing and vulnerability scanning are two different things. Penetration testing will give you information about exploiting vulnerabilities whereas a vulnerability scan will just provide you with potential avenues for exploitation. Insight #1.

Security Boulevard
JULY 14, 2023
Conducting regular penetration tests (pentests) is a proactive option that identifies, evaluates and mitigates risks. The post Why Pentesting-as-a-Service is Vital for Business Security appeared first on Security Boulevard.

CyberSecurity Insiders
APRIL 25, 2023
In times of economic downturn, companies may become reactive in their approach to cybersecurity management, prioritizing staying afloat over investing in proactive cybersecurity measures. However, it’s essential to recognize that cybersecurity is a valuable investment in your company’s security and stability.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content