Mastering NIST Penetration Testing: Your Essential Guide to Robust Cybersecurity
Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.

eSecurity Planet
JUNE 28, 2023
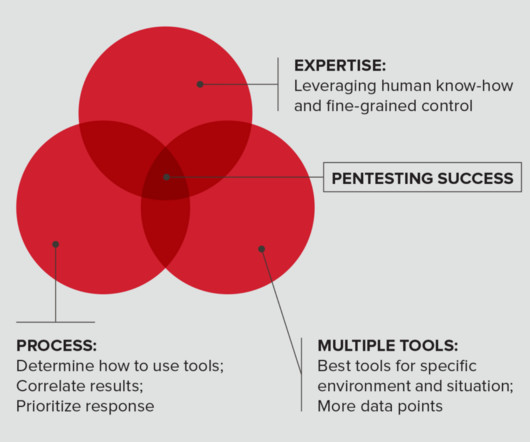
Penetration tests are vital components of vulnerability management programs. In these tests, white hat hackers try to find and exploit vulnerabilities in your systems to help you stay one step ahead of cyberattackers. Here we’ll discuss penetration testing types, methods, and determining which tests to run.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
JUNE 23, 2023
All organizations should perform penetration tests, yet many worry about not receiving the full value of their investment. Organizations have two choices: perform penetration tests with their internal teams, or hire an external vendor and find ways to lower costs.

eSecurity Planet
FEBRUARY 25, 2022
Many cybersecurity audits now ask whether penetration testing is conducted and how vulnerabilities are detected and tracked. These questions ask IT teams to consider how frequently security is tested from the outside via penetration testing and from the inside via vulnerability testing.

eSecurity Planet
MARCH 7, 2023
Penetration tests are simulated cyber attacks executed by white hat hackers on systems and networks. There are different types of penetration tests, methodologies and best practices that need to be followed for optimal results, and we’ll cover those here. However, they are also the most realistic tests.

Pen Test
OCTOBER 12, 2023
Introduction Radio Frequency (RF) penetration testing, popularly referred to as RF pentesting, stands as a vital domain within ethical hacking. The rapid advancement of technology has woven a complex fabric of wireless networks, each interwoven with vulnerabilities waiting to be exposed. What is Radio Frequency (RF)?
eSecurity Planet
FEBRUARY 24, 2022
A penetration test , or pen test, is the simulation of a cyber attack. This critical IT security practice isn’t the same as a vulnerability assessment or vulnerability scanning, though, as pen testing involves an actual attack similar to what hackers would do in real-world conditions. Best Pen Testing Frameworks.

Penetration Testing
APRIL 26, 2024
Hanwha Vision, a leader in surveillance technology, has swiftly responded to significant cybersecurity threats identified in several of its network video recorders (NVR) and digital video recorders (DVR).

Pentester Academy
MARCH 29, 2023
Penetration testing is an integral part of cybersecurity, so it’s no surprise that it’s a rapidly growing role. O’Net Online reports that penetration testing roles will grow by almost 35,000 jobs by 2031, a faster-than-average growth rate. The entire thing is open book, just like in real life. Sign up now.

CyberSecurity Insiders
MAY 3, 2023
Penetration testing (pentesting) is one of the fundamental mechanisms in this area. In contrast to this, red teaming focuses on exploiting a segment of a network or an information / operational technology (IT/OT) system over an extended period. They do overlap in quite a few ways, but each has its unique hallmarks.

Penetration Testing
NOVEMBER 2, 2023
Boeing, a pivotal entity in the aerospace industry and defense technology, has confirmed it fell victim to a cyberattack, presumably orchestrated by the notorious hacking collective LockBit, accused of illicit access to confidential information... The post LockBit’s Latest Victim: Boeing’s Cybersecurity Compromise Unveiled appeared (..)

The Last Watchdog
FEBRUARY 8, 2024
8, 2024 – Diversified , a leading global technology solutions provider, today announced a partnership and trio of solutions with GroCyber. Newfield “Diversified has deep expertise in AV and media, and our conversations with clients have made clear that they want and need help navigating the complex cybersecurity landscape.

BH Consulting
APRIL 17, 2024
Delivering cybersecurity testing services, such as but not limited to penetration testing services (including web app, mobile app, and network), vulnerability assessments, phishing campaigns, and red teaming exercises. Expert knowledge of, or willingness to learn, cloud cybersecurity best practices. is required.

The Last Watchdog
MAY 8, 2024
May 8, 2024, CyberNewsWire — Security Risk Advisors (SRA) announces the launch of their OT/XIoT Detection Selection Workshop, a complimentary offering designed to assist organizations in selecting the most suitable operational technology (OT) and Extended Internet of Things (XIoT) security tools for their unique environments.

The Last Watchdog
NOVEMBER 1, 2023
1, 2023 — AdviserCyber , a cybersecurity service provider for Registered Investment Advisers (RIAs) with $500M to $3B Assets Under Management (AUM) who must comply with the Securities and Exchange Commission (SEC) cybersecurity requirements, announced its formal launch today. Phoenix, Ariz. —

NopSec
AUGUST 9, 2022
Once you’ve started a vulnerability scanning system , you may want to take the next step in identifying vulnerabilities: penetration testing, commonly referred to as pentesting. The Basics of Penetration Testing Pentesting can be as broad or narrow as the client wishes. This more closely simulates an actual cyber attack.

Penetration Testing
DECEMBER 7, 2023
Cybersecurity and Infrastructure Security Agency (CISA) unraveled a cyber attack that not only breached technological defenses but also posed a threat to public safety. This incident involved the active... The post Hackers attacked US water facility via CVE-2023-6448 vulnerability appeared first on Penetration Testing.
NetSpi Executives
APRIL 27, 2024
Table of Contents What is penetration testing? How penetration testing is done How to choose a penetration testing company How NetSPI can help Penetration testing enables IT security teams to demonstrate and improve security in networks, applications, the cloud, hosts, and physical locations.

Penetration Testing
NOVEMBER 17, 2023
In the realm of cybersecurity, JSON Web Tokens (JWTs) have become an indispensable tool for secure communication and data exchange. However, even the most widely used technologies can harbor vulnerabilities, and a recent discovery... The post CVE-2023-48238: A Critical Vulnerability in json-web-token for Node.js

The Last Watchdog
MARCH 15, 2021
When we look at society today, we can see that we are moving further and further ahead with technology. In fact, there is evidence that technology grows exponentially fast. Since we are quickly putting out large technologies, security risks always come with this. Related: Integrating ‘pen tests’ into firewalls.

eSecurity Planet
OCTOBER 17, 2022
NetSPI, a top penetration testing and vulnerability management company, recently announced a $410 million funding round, a huge amount in a year in which $100+ million rounds have become a rarity. According to data from Crunchbase , the total amount of investments in cybersecurity startups came to $2.6

eSecurity Planet
OCTOBER 31, 2023
A penetration testing report discloses the vulnerabilities discovered during a penetration test to the client. Penetration test reports deliver the only tangible evidence of the pentest process and must deliver value for a broad range of readers and purposes.

The Last Watchdog
JULY 11, 2023
Conduct regular penetration testing. Regular and thorough penetration testing is crucial for identifying vulnerabilities within trading systems. Having access to a partner focused in cybersecurity brings fresh perspectives and allows for an unbiased evaluation of the systems in use.
NetSpi Executives
FEBRUARY 21, 2024
Like many technologies that came before it, AI is advancing faster than security standards can keep up with. The most successful technology innovations start with security from the ground up. Learn about our AI/ML Penetration Testing or contact us for a consultation.

IT Security Guru
JUNE 30, 2023
With cyber threats constantly dominating headlines, the draw of a career in cybersecurity has never been higher for young professionals. Degrees Paving the Path A degree often acts as a stepping stone for a career in cybersecurity. Moreover, universities and colleges across the UK offer specialised programmes in cybersecurity.

Penetration Testing
NOVEMBER 26, 2023
Cybersecurity and Infrastructure Security Agency (CISA) and the UK National Cyber Security Centre (NCSC) have joined forces to unveil the “Guidelines for Secure AI System Development.” In a groundbreaking collaboration, the U.S.

Penetration Testing
NOVEMBER 20, 2023
Launched in 2013, this initiative has become a cornerstone of Microsoft’s cybersecurity strategy, awarding over $60 million... The post $60 Million and Counting: Microsoft Rewards Bug Bounty Hunters appeared first on Penetration Testing.

The Hacker News
JANUARY 24, 2021
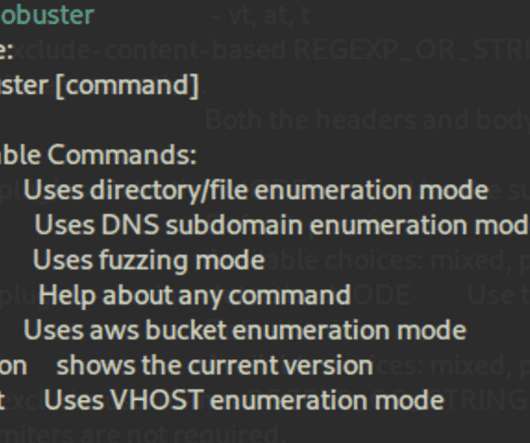
Over the years, penetration testing has had to change and adapt alongside the IT environments and technology that need to be assessed. Broad cybersecurity issues often influence the strategy and growth of pen-testing.

CyberSecurity Insiders
MAY 10, 2023
The cybersecurity workforce gap also increased by 26.2% As a fresh new batch of cybersecurity graduates enter the workforce, I’d like to offer a few bits of advice. Going Beyond Technical Credentials What distinguishes candidates who will fare well in the high-stress, continually evolving cybersecurity industry?

eSecurity Planet
OCTOBER 13, 2023
Penetration testing is a critically important cybersecurity practice, but one that many organizations lack the on-staff skills to do themselves. Fortunately, there are many pentesting services out there that can do the job for them across a range of budgets and needs.
eSecurity Planet
JULY 20, 2023
Kevin Mitnick, who turned legendary hacking exploits and two prison terms into a career as an esteemed cybersecurity leader, died Sunday at age 59 after a 14-month battle with pancreatic cancer, KnowBe4 revealed today. KnowBe4 has been ranked in the top 20 on our list of the top cybersecurity companies for several years.

eSecurity Planet
JUNE 21, 2022
” Also read: Cybersecurity Employment in 2022: Solving the Skills Gap. “Certifications range from penetration testers , government/industry regulatory compliance , ethical hacking , to industry knowledge,” he said. Also read: How to Get Started in a Cybersecurity Career. The Top Cybersecurity Certifications.

The Last Watchdog
JANUARY 2, 2024
Related: How AI is transforming DevOps The constant evolution of technology, increased connectivity, and sophisticated cyber threats pose significant challenges to organizations of all sizes and industries. Organizations must stay ahead of these threats, but it can be challenging due to the dynamic nature of the cybersecurity landscape.

The Last Watchdog
AUGUST 29, 2022
Penetration testing – pen tests – traditionally have been something companies might do once or twice a year. Horizon3 supplies “autonomous” vulnerability assessment technology. businesses need to take a wartime approach the cybersecurity. Related : Cyber espionage is on the rise. Bad news is always anticipated.

CompTIA on Cybersecurity
JULY 21, 2021
As more entities adopt cloud technology, the way we execute penetration testing changes. Learn about these new challenges.

NopSec
JUNE 28, 2017
The car question is very much akin to asking “How much does a great penetration test cost ?” One man’s great penetration test is another man’s disaster. A quick search on Google for “great penetration test” yields 1,130,000 results. What’s your definition of a “great” penetration test?

SecureWorld News
APRIL 17, 2022
It can certainly be said that advances in technology have had a huge impact on cybersecurity in recent years. It was once the case that cybersecurity technology consisted of little more than a firewall and antivirus software. A diminished role in cybersecurity? Are humans still needed in cybersecurity?

BH Consulting
JUNE 2, 2022
Job Title: (Technical) Cybersecurity Consultant. BH Consulting is an ever-expanding cybersecurity and data protection consulting service – with offices in Dublin, London and New York. Communicating the results of the above tests – via the production of high quality reports, executive summaries and board-level presentations.

NetSpi Executives
FEBRUARY 21, 2024
Like many technologies that came before it, AI is advancing faster than security standards can keep up with. The most successful technology innovations start with security from the ground up. Learn about our AI/ML Penetration Testing or contact us for a consultation.

Security Boulevard
JANUARY 17, 2023
When California allowed car owners to opt for “digital license plates” which could be customized to add personal messages, few who opted into the new technology suspected that they were permitting the government to track their location anywhere they were.

Zigrin Security
SEPTEMBER 13, 2023
This article is not about “How to use the benefits of AI language models while conducting penetration test”. This article is about “How to conduct a penetration test towards AI language models”. In this article you will find: The famous ChatGPT Why Should You Arrange a Penetration Test for Your AI Model as an Executive?

CyberSecurity Insiders
JUNE 7, 2023
Therefore, it’s crucial that small businesses make cybersecurity a top priority. What drives more cybersecurity attacks on small businesses? The influx of remote working culture has added new challenges and cybersecurity risks for small businesses. They also have a limited budget to spend on effective cyber security measures.

Security Affairs
SEPTEMBER 11, 2023
For a more detailed analysis, a deeper penetration testing would be required,” Cybernews researchers noted. The Latin American Technology University Online (UTEL) website was leaking JSON Web Token secrets, Google Cloud secrets, credentials, hosts for multiple databases, and Git URL (without credentials).

IT Security Guru
JANUARY 26, 2024
In the current digital era, technology has become an integral part of various industries, and the transport industry is not left behind. Nevertheless, the development of IoT and fleet management systems brings up issues with cybersecurity risks.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content