Interview With a Crypto Scam Investment Spammer
Krebs on Security
MAY 22, 2023
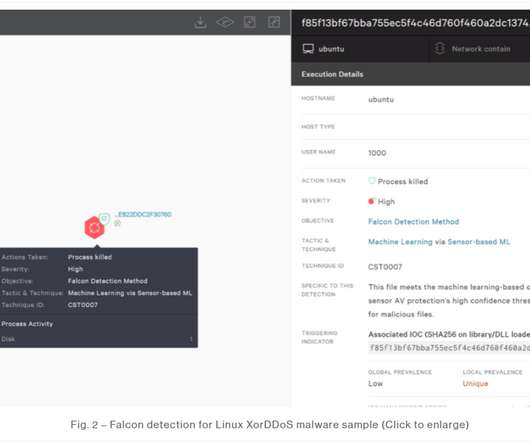
Shortly after that, those same servers came under a sustained distributed denial-of-service (DDoS) attack. Chaput said whoever was behind the DDoS was definitely not using point-and-click DDoS tools, like a booter or stresser service. “On Twitter, more spam and crypto scam.”

























Let's personalize your content