NordVPN: How to protect your organization from DDoS attacks
Tech Republic Security
AUGUST 19, 2020
Without early threat detection, you may not know your website has been hit by a DDoS attack until it slows down or stops, says NordVPN Teams.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
AUGUST 19, 2020
Without early threat detection, you may not know your website has been hit by a DDoS attack until it slows down or stops, says NordVPN Teams.

Tech Republic Security
SEPTEMBER 15, 2020
Without early threat detection, you may not know your website has been hit by a DDoS attack until it slows down or stops, says NordVPN Teams.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CyberSecurity Insiders
OCTOBER 16, 2022
Cloudflare, a web performance and security company, revealed the news in its latest ‘DDoS Threat Report’ that included insights and trends that are being followed in the distributed denial of service attacks threat landscape in 2022. But as the threat detection service was automated, the response was on time and curated.
CyberSecurity Insiders
MARCH 24, 2023
Most were distributed denial of service attacks aka DDoS and a mixture of other attack patterns. Microsoft issued a clarification that those enrolled in Azure DDoS Network Protection and Web Application Firewall services need not worry as all such attacks will be mitigated by the threat detection teams of the company.

CyberSecurity Insiders
JUNE 15, 2022
It ensures protection against known and zero-day attacks with an integrated WAF, anti-DDoS, bot management, and API protection. DDoS Attack Protection. Anti-DDoS solutions secure on-premise as well as cloud-based assets no matter where they’re hosted (Microsoft Azure, AWS, or Google Publish Cloud). Real-Time Attack Analytics.
Security Affairs
MAY 5, 2020
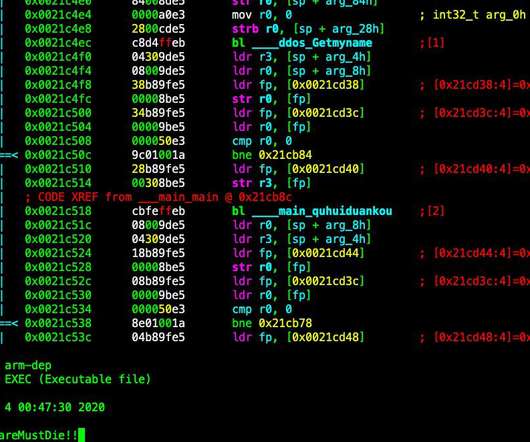
Security researchers spotted a new piece of DDoS bot dubbed Kaiji that is targeting IoT devices via SSH brute-force attacks. The malicious code was designed to target Linux-based servers and Internet of Things (IoT) devices and use them as part of a DDoS botnet. You may want to block #C2 at: 1[.]versionday[.]xyz versionday[.]xyz

The Last Watchdog
OCTOBER 5, 2023
Byron: On the software side of things, some exciting breakthroughs are about to gain meaningful traction in leveraging machine learning and automation to shape new security platforms and frameworks that are much better suited to helping companies implement cyber hygiene, as well as execute effective, ongoing threat detection and incident response.

SecureList
DECEMBER 14, 2022
Taking sides: professional ransomware groups, hacktivists, and DDoS attacks. DDoS attacks and, to a lesser extent, defacement of random websites have always been regarded as low-sophistication and low-impact attacks by the security community. Kaspersky DDoS protection also reflects this trend.

CyberSecurity Insiders
JANUARY 12, 2022
Our Omnis® Cybersecurity advanced threat detection and response platform offers comprehensive network visibility, threat detection, highly contextual investigation, and automated mitigation at the network edge.

CyberSecurity Insiders
APRIL 20, 2023
The WAAP market is diverse and includes DDOS, bot management, web application protection and API security. The AT&T Cybersecurity booth will be a hub of activity with demo stations, presentations, and other social networking activities.

Webroot
MARCH 9, 2021
One of the most common methods of infiltration includes internet-based attacks, such as Denial of Service (DoS), Distributed Denial of Service (DDoS) and DNS poisoning. Aside from arming yourself with the knowledge you need to identify attacks, it’s important to install threat detection and remediation software on your devices.

eSecurity Planet
JANUARY 18, 2024
Cloud Storage Security Risks Despite its obvious benefits, cloud storage still faces common challenges, including misconfiguration, data breaches, insecure interface, unauthorized access, DDoS attacks, insider threats, lack of control, encryption problems, patching issues, compliance, and monitoring issues.
CyberSecurity Insiders
APRIL 30, 2021
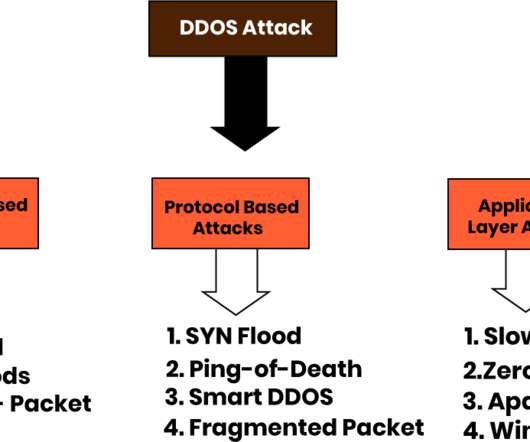
Is your organization prepared to mitigate Distributed Denial of Service (DDoS) attacks against mission-critical cloud-based applications? A DDoS attack is a cyber attack that uses bots to flood the targeted server or application with junk traffic, exhausting its resources and disrupting service for real human users. Source: Testbytes.

CyberSecurity Insiders
DECEMBER 16, 2021
According to a Netlab blog on December 13, 2021, Netlab identified 10 different implants using the vulnerability to spread: Muhstik, DDoS+backdoor. DDoS family Elknot. JNDI related scans across honeypots. Mining family m8220. SitesLoader. xmrig.pe / xmrig.ELF. Meterpreter variants.
Cisco Security
SEPTEMBER 22, 2021
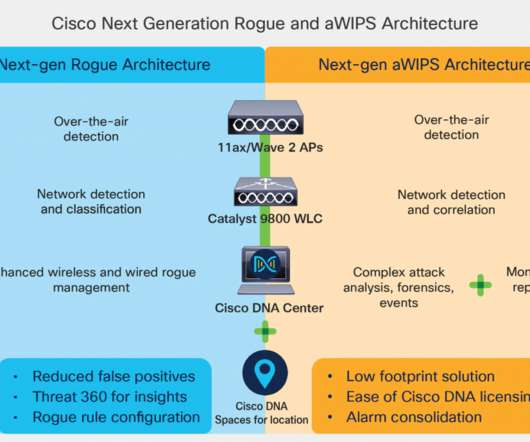
Distributed Denial of Service (DDoS) attacks alone are up 33% from last year , with a 37% increase in attack bandwidth. Cisco’s Advanced Wireless Intrusion Prevention System (aWIPS) and Rogue Management is a fully infrastructure-integrated solution that constantly monitors radio spectrum to detect, analyze, and thwart attacks.

eSecurity Planet
FEBRUARY 13, 2023
CNAP provides encryption, access control, threat detection and response features for enhanced security. Distributed denial of service (DDoS) attacks remain an ever-present threat to web applications, with their ability to overwhelm web servers with a flood of traffic.

Anton on Security
JUNE 10, 2022
are now joined by DDR (one vendor claimed “Data Detection and Response”) and ITDR (no, not for IT, silly: “Identity Threat Detection and Response”). An anti-DDoS vendor promised “better zero trust visibility.” XDR’s older brothers?—?EDR EDR and NDR?—?are I have not spotted CDR this time, but maybe I should have?—?more
CyberSecurity Insiders
APRIL 13, 2021
Piecemeal security solutions fragment visibility, limiting threat detection as well as complicating a unified response to threats once they are discovered. Without a clear view of security events across all of your web applications, you are exposing your applications—and your organization—to unnecessary and serious risk.

SiteLock
AUGUST 27, 2021
Knowing where the most likely threats are really coming from is the first step to preventing them from harming your business. Although new threats are being created every day, most successful hacks are variations on old themes, like the DDoS attacks that are as old as the internet itself. Learn from the past.

Malwarebytes
APRIL 14, 2023
In addition to launching DDoS attacks, botnets like Mirai can aid hackers in weakening website security, stealing credit card information, and distributing spam. If successful in its malicious login attempts, Mirai compromises the device and integrates it into the existing botnet. This excludes the following network ranges: 10.0.0.0/8

CyberSecurity Insiders
JUNE 1, 2023
With the widespread use of technology and the increasing amount of data being stored and shared electronically, financial institutions must ensure that they have robust cybersecurity measures in place to protect against evolving threats. Sometimes theft of PII can lead to identity theft too.

Security Boulevard
MAY 9, 2022
As far as the actual ransom process goes, Blackcat group has adopted several of the more recently common practices when interacting with victims: threats to release small batches of data upon lack of payment, showing non-payers in a public ‘wall of shame’, and using contractors and customers to gain payment from victims.

Security Boulevard
JUNE 10, 2022
are now joined by DDR (one vendor claimed “Data Detection and Response”) and ITDR (no, not for IT, silly: “Identity Threat Detection and Response”). An anti-DDoS vendor promised “better zero trust visibility.” XDR’s older brothers?—?EDR EDR and NDR?—?are I have not spotted CDR this time, but maybe I should have?—?more

eSecurity Planet
SEPTEMBER 1, 2023
Denial of Service (DoS) Attacks DDoS attacks target the availability and performance of cloud services, inundating them with malicious traffic or exploiting weaknesses to interrupt routine operations. Attackers may occasionally use DDoS assaults to divert attention from other actions like data theft or malware installation.

eSecurity Planet
AUGUST 4, 2023
CWPP provides strong defenses against a wide range of risks such as malware , ransomware , DDoS attacks , configuration errors , insider threats, and data breaches. The performance of cloud workloads may be impacted by monitoring and real-time threat detection. Some CWPP products could have difficulty scaling.

CyberSecurity Insiders
SEPTEMBER 27, 2021
CHALLENGE: Increasing number of ransomware and DDoS attacks, new vulnerabilities introduced by work-from-home, and the need to protect rapidly growing volumes of IoT devices, has put many enterprise security organizations at a crossroads. This shift requires them to re-think their approach to secure-edge networking, and connected endpoints.

SecureWorld News
JUNE 13, 2023
Recent findings from Nokia's Threat Intelligence Report 2023 reveal a sharp increase in such malicious activities, highlighting the need for strong cybersecurity measures. However, this threat has since expanded globally, affecting various parts of the world.

CyberSecurity Insiders
FEBRUARY 2, 2022
Exploitation. System failure. Overheating in Room. Out of Electricity. Unauthorized Access. Open Ports. Old Cooling Devices (AC). Malicious Payloads. Policies & Procedures. Rogue Devices. Misconfiguration. Not updating devices. Each asset is given a risk level or grade during risk assessment.

CyberSecurity Insiders
APRIL 6, 2023
: Digital Realty, Equinix, Splunk, USM Anywhere ( USMA ), Rapid7) Servers and networking gear administrative account management (Firewalls, routers, VPN, WAF, load balancer, DDoS prevention, SIEM, database, Wi-Fi) Internal user account management, (Active Directory, LDAP or equivalent, and third parties who may act as staff augmentation or maintenance (..)

CyberSecurity Insiders
SEPTEMBER 23, 2021
For a DDoS attack, use the macof tool again to generate traffic. The image below shows IP address is generating requests to another device with the same data size repeatedly. This sort of traffic shows a standard network DoS attack. Observe the fake source and destination IP addresses are sending many packets with similar data sizes.

eSecurity Planet
JANUARY 27, 2022
Intelligence: Global threat intelligence, advanced threat detection, and integrated incident response. Metrics: Monitors more than 195 billion NetFlow sessions daily, and mitigates 120 DDoS attacks per day. AT&T was named as a Niche Player in Gartner’s most recent Magic Quadrant for MSSPs. million devices.

eSecurity Planet
JULY 19, 2023
It offers real-time API discovery and threat prevention across your entire portfolio, regardless of the protocol, in multi-cloud and cloud-native environments. AWS quotes Reblaze pricing starting at $5,440 a month for comprehensive web application protection, including API, web application firewall and DDoS protection.

eSecurity Planet
AUGUST 22, 2023
Application and website security monitors and manages tools to prevent incidents such as server attacks, distributed denial of service (DDoS), and cross-site scripting (XSS) attacks. Email security deploys tools , uses techniques, and implements protocols such as SPF , DKIM , and DMARC to prevent threats delivered via email and attachments.

CyberSecurity Insiders
NOVEMBER 11, 2021
It also has different DDoS functionality. However, there is a difference between the Mirai malware and the new malware variants using Go, including differences in the language in which it is written and the malware architectures. Mirai is a botnet that initiates its communication with its command and control (C&C).

eSecurity Planet
FEBRUARY 9, 2022
Phishing , general malware , and Distributed Denial of Service ( DDoS ) attacks are more common. It provides a holistic view of an organization’s environment, with analysis for threat detection, investigation, and response. Also read: Top Endpoint Detection & Response (EDR) Solutions. DDoS Protection.

eSecurity Planet
MARCH 17, 2023
Vulnerability Management Product Guides 8 Best Vulnerability Scanner Tools Top 10 Open Source Vulnerability Assessment Tools 12 Top Vulnerability Management Tools Threat Intelligence and Detection At the most basic level, threat detection strategies and tools monitor networks for suspicious and anomalous activity.

eSecurity Planet
JANUARY 26, 2022
Kentik’s solutions can protect core, edge, and cloud networks while adding DDoS and botnet protection, supply chain analytics, and synthetics. In 2022, the Arizona-based vendor specializes in network performance monitoring and threat analysis with its Observer platform. Kentik Features. SolarWinds.

Spinone
MARCH 17, 2018
The biggest ever DDoS attack was recently carried out using over 150,000 hacked smart devices worldwide including cameras, printers, and fridges. Millions of smart TVs are at risk of click fraud, botnets, data theft, and ransomware. 75% of Bluetooth Smart door locks have been found to have vulnerabilities that allow them to be easily hacked.

eSecurity Planet
MAY 24, 2023
A cloud workload protection platform (CWPP) shields cloud workloads from a range of threats like malware, ransomware, DDoS attacks, cloud misconfigurations, insider threats, and data breaches. Real time threat detection. per server per month. AWS offers different pricing options calculated here.

IT Security Guru
MARCH 17, 2023
The threat landscape Organizations are wise to prioritize cybersecurity strategy and adequate budgeting to protect their networks and valuable private data. DDoS, SQL injections, supply chain attacks, DNS tunneling – all pervasive attacks that can arrive on your doorstep anytime. Cybercrime is predicted to reach an alarming $10.5

eSecurity Planet
SEPTEMBER 1, 2021
Unfortunately, threat actors can also take advantage of 5G’s enhanced connectivity, executing network attacks faster than ever before. Hackers can spread malware via IoT networks, disrupt supply chains in development, and use a fleet of routers as an IoT botnet to launch a DDoS attack. Network Slice Compromise.

CyberSecurity Insiders
MAY 10, 2023
DDoS versus ransomware – how does edge computing change the equation? I spoke about our research findings that indicate a change in perceived attacks: when it comes to edge computing, DDoS is perceived as a greater attack concern than ransomware.

eSecurity Planet
OCTOBER 26, 2023
DDoS Attacks DDoS attacks have the potential to interrupt and render cloud services inaccessible. DDoS prevention and mitigation is critical for maintaining service availability. Reliability and Security DDoS assaults may be mitigated by dispersing workloads over several cloud environments.

eSecurity Planet
SEPTEMBER 13, 2021
LogRhythm Threat Lifecycle Management (TLM) Platform delivers a coordinated collection of data analysis and incident response capabilities to enable organizations around the globe to rapidly detect, neutralize and recover from security incidents. Key Features: Automated threat detection. Learn more about LogRhythm.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content