SHARING INTEL: Why full ‘digital transformation’ requires locking down ‘machine identities’
The Last Watchdog
OCTOBER 16, 2019
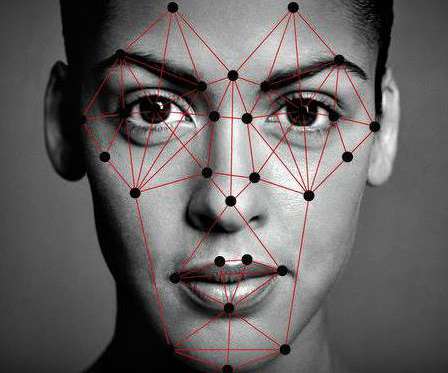
This is so in spite of the fact that machine identities are exploding in numbers and have come to saturate digital transformation. Machine identities are divvied out as digital certificates issued by Certificate Authorities (CAs) — vendors that diligently verify the authenticity of websites.













































Let's personalize your content