NEW TECH: Exabeam positions SIEM technology to help protect IoT, OT systems
The Last Watchdog
MARCH 9, 2020
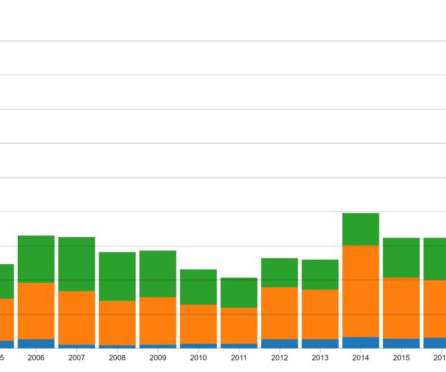
Security information and event management systems — SIEMs — have been around since 2005, but their time may have come at last. Related: Digital Transformation gives SIEMs a second wind After an initial failure to live up to their overhyped potential, SIEMs are perfectly placed to play a much bigger role today.



































Let's personalize your content