A Reactive Cybersecurity Strategy Is No Strategy at All
CyberSecurity Insiders
MAY 18, 2022
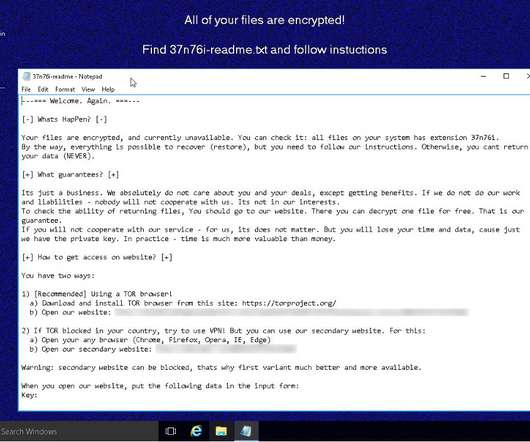
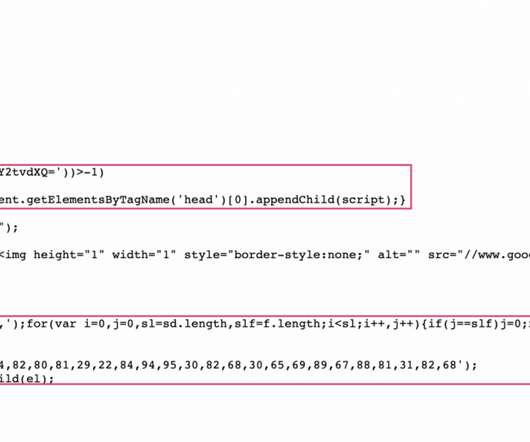
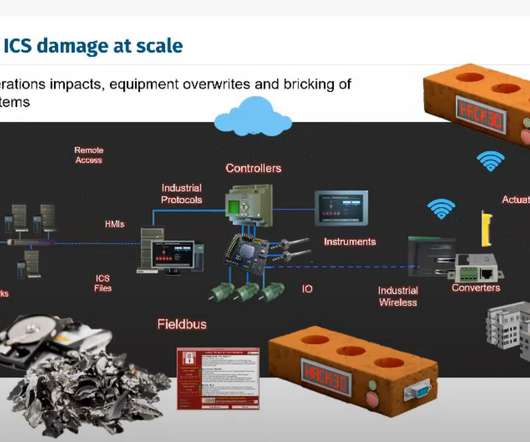
These developments have made the perimeter so porous that the old approach of simply hiding behind a firewall and keeping the rest of the world at bay is no longer feasible. However, this reconnaissance or dwell period also presents an opportunity to stop the malware before it has activated. So where do we go from here?






























Let's personalize your content