A Deep Dive on the Recent Widespread DNS Hijacking Attacks
Krebs on Security
FEBRUARY 18, 2019
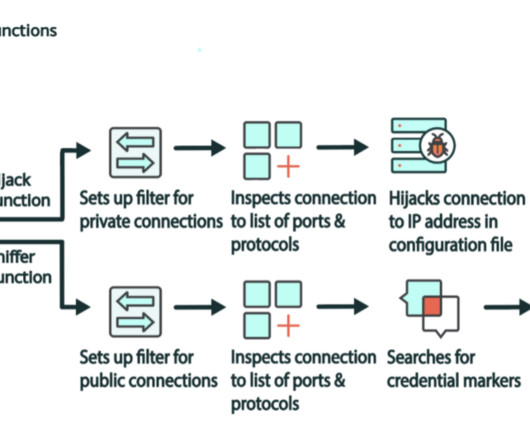
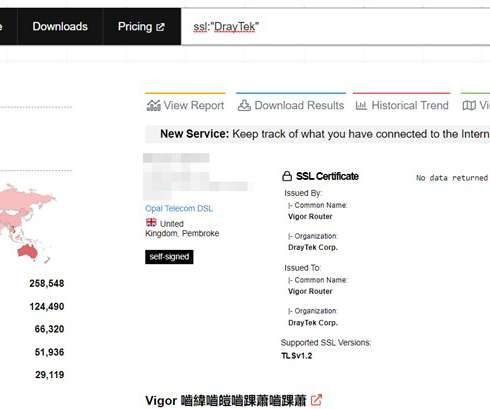
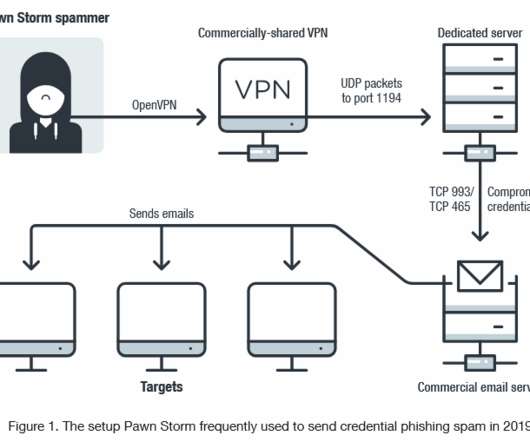
government — along with a number of leading security companies — recently warned about a series of highly complex and widespread attacks that allowed suspected Iranian hackers to siphon huge volumes of email passwords and other sensitive data from multiple governments and private companies.




































Let's personalize your content