New Phishing Kit Hijacks WordPress Sites for PayPal Scam
Dark Reading
JULY 14, 2022
Attackers use scam security checks to steal victims' government documents, photos, banking information, and email passwords, researchers warn.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Krebs on Security
AUGUST 17, 2023
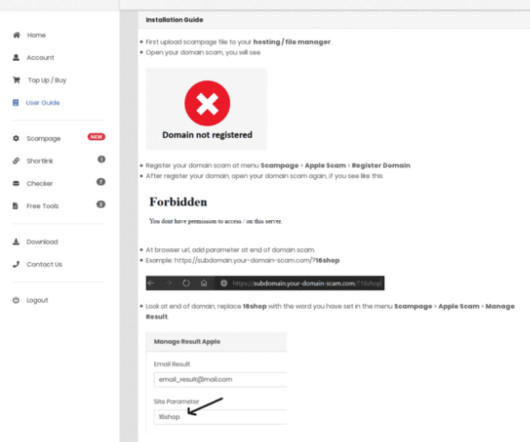
You’ve probably never heard of “ 16Shop ,” but there’s a good chance someone using it has tried to phish you. A 16Shop phishing page spoofing Apple and targeting Japanese users. Image: Akamai.com. The INTERPOL statement says the platform sold hacking tools to compromise more than 70,000 users in 43 countries.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Krebs on Security
MAY 22, 2019
Some of the most convincing email phishing and malware attacks come disguised as nastygrams from a law firm. Such scams typically notify the recipient that he/she is being sued, and instruct them to review the attached file and respond within a few days — or else. Note: The password for the document is 123456.
Identity IQ
APRIL 20, 2023
Tax Season Scams: How to Protect Your Identity IdentityIQ While it’s important to be on high alert and protect your identity all year long, tax season is an especially vulnerable time. Every tax season, identity thieves run a variety of scams to get their hands on taxpayers’ personal information. It’s probably a scam.

Adam Levin
NOVEMBER 17, 2020
Here are 50 ways to avoid getting scammed on Black Friday — and beyond. Make sure your smartphone, tablet and laptop are password-protected, particularly if you’re in the habit of carrying them around wherever you go. Popular browsers, like Safari or Firefox, frequently issue updates to protect against scams. Lock your devices.

Krebs on Security
NOVEMBER 2, 2018
Thieves are combining SMS-based phishing attacks with new “cardless” ATMs to rapidly convert phished bank account credentials into cash. Recent arrests in Ohio shed light on how this scam works. Image: Mastercard.us. A graphic from Mastercard touting the potential benefits of cardless ATM transactions.

SecureWorld News
OCTOBER 30, 2023
When it comes to impactful types of internet-borne crime, phishing is the name of the game. According to Verizon's 2023 Data Breach Investigations Report (DBIR), a whopping 74% of breaches involve a human element, which is exactly what phishing aims to exploit. And for good reason. Tactics matter a lot, too.

Krebs on Security
APRIL 14, 2019
site that helps him manage more than 500 scam properties and interactions with up to 100 (soon-to-be-scammed) “guests” looking to book the fake listings. The Land Lordz administrative panel for a scammer who’s running dozens of Airbnb scams in the United Kingdom. The price is € 250 + €500 secure deposit.

Malwarebytes
AUGUST 18, 2021
Phishing scammers love well known brand names, because people trust them, and their email designs are easy to rip off. DocuSign is a service that allows people to sign documents in the Cloud. DocuSign is a service that allows people to sign documents in the Cloud. Signing documents electronically saves a lot of paper and time.

The Last Watchdog
SEPTEMBER 28, 2022
Phishing attacks are nothing new, but scammers are getting savvier with their tactics. The Iranian hacker group TA453 has recently been using a technique that creates multiple personas to trick victims , deploying “social proof” to scam people into engaging in a thread. Spear phishing. Phishing via texting.

SecureWorld News
NOVEMBER 1, 2022
Halloween may have just passed, but things are getting spooky for Twitter users that are being scammed by cybercriminals taking advantage of Elon Musk's purchase of the social media behemoth. Signs that the campaign is a phishing scam: Poor grammar and writing that no business would publish (a hallmark of phishing scams).

Identity IQ
FEBRUARY 7, 2023
What is Phishing? One of the most common techniques used to exploit web users is the phishing scam. This article will cover what phishing is, cybercriminals’ different approaches, and how to prevent yourself from becoming a victim. What is Phishing? How Does Phishing Work? Spear Phishing.
Identity IQ
JANUARY 26, 2022
How Do You Avoid Tax Scams? Tax season is here, and it’s essential to watch out for common tax scams. The IRS reports that in the last nine years tax scams have cost victims more than $23 million. Here are two scams to be aware of and a few tips for how you can help avoid them. Phone Scams. Email Phishing Scams.

SecureList
FEBRUARY 16, 2023
Short-lived phishing sites often offered to see the premieres before the eagerly awaited movie or television show was scheduled to hit the screen. Thus, during the World Cup a brand-new scam appeared: it offered users to win a newly released iPhone 14 for predicting match outcomes.

Hot for Security
FEBRUARY 3, 2021
Fraudsters had an early start anticipating the buzz surrounding tax filing season, with phishing campaigns impersonating the government agency as early as November 25, 2020, according to Bitdefender Antispam Lab. The genuine format of the tax exemption document looks like this: Original W-8BEN form version. IRS phishing email sample.

Hot for Security
FEBRUARY 15, 2021
As millions of citizens prepare for what may be the most challenging tax season to date, identity thieves got a head start, deploying phishing campaigns impersonating the agency as early as November 25, 2020. Different versions of the scam will most likely pop up in the weeks preceding the April 15 deadline. © 2021 EFILE. Trademarks.

Hot for Security
JULY 2, 2021
According to Bitdefender Antispam Lab researchers, cyber thieves are actively targeting DocuSign and Sharepoint users in phishing attacks designed to mimic legitimate correspondence from the two web-based platforms. The phishing attack spotted on June 24 appears to have originated from the United States.

CyberSecurity Insiders
NOVEMBER 14, 2021
Even if you’ve never been scammed before, you may know somebody who has. 2020 was a high-water mark for online scams and fraud. Not every scam is strictly about money. Here are five things to remember if you’ve been scammed. Most fraud attempts begin with cybercriminals phishing for your personal information.

Krebs on Security
NOVEMBER 21, 2020
The attacks were facilitated by scams targeting employees at GoDaddy , the world’s largest domain name registrar, KrebsOnSecurity has learned. In due course, the malicious actor was able to partially compromise our infrastructure, and gain access to document storage.” ” In the early morning hours of Nov. PST on Nov.
SecureList
FEBRUARY 15, 2021
The Kaspersky Anti-Phishing component blocked 434,898,635 attempts at accessing scam sites. The most frequent targets of phishing attacks were online stores (18.12 The contact phone trick was heavily used both in email messages and on phishing pages. Agentb malware family. Trends of the year. Messengers targeted.

Krebs on Security
JANUARY 30, 2024
.” Group-IB dubbed the gang by a different name — 0ktapus — which was a nod to how the criminal group phished employees for credentials. The missives asked users to click a link and log in at a phishing page that mimicked their employer’s Okta authentication page. On July 28 and again on Aug. According to an Aug.

Duo's Security Blog
APRIL 20, 2023
Through the first two months of 2023 alone, the Australian Competition and Consumer Commission’s Scamwatch reported more than 19,000 phishing reports with estimated financial losses of more than $5.2 What is phishing? This is part of what makes phishing attacks so dangerous.
SecureList
FEBRUARY 9, 2022
Our Anti-Phishing system blocked 253 365 212 phishing links. Safe Messaging blocked 341 954 attempts to follow phishing links in messengers. This means the person who completes the full task not only gives the scammers money, but also recommends the scam to people in their list of contacts. Trends of the year.

Malwarebytes
MARCH 20, 2021
There’s been a number of scams targeting fans of major upcoming video game releases over the last week or two. Early access, where players are granted first look at a title by paying or for free, is where our latest scam lies. Scammers are using demos and early access promises as bait for phishing and other forms of attack.
Krebs on Security
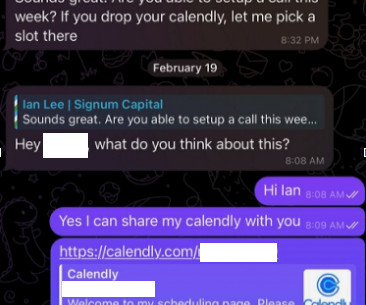
FEBRUARY 28, 2024
Lee was trying to scam people on Telegram. Unfortunately for us, Doug freaked out after deciding he’d been tricked — backing up his important documents, changing his passwords, and then reinstalling macOS on his computer. ” Image: SlowMist. Image: SlowMist.
Krebs on Security
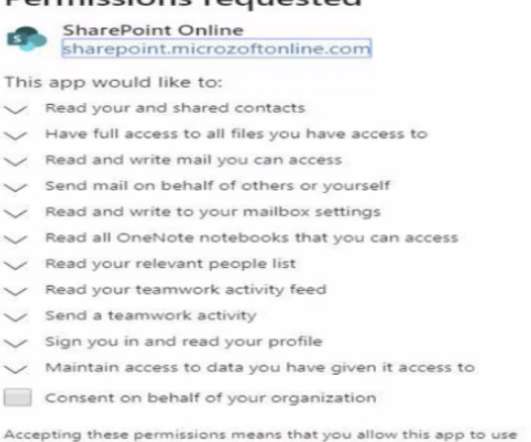
MAY 5, 2021
After a user logs in, the link prompts them to install a malicious but innocuously-named app that gives the attacker persistent, password-free access to any of the user’s emails and files, both of which are then plundered to launch malware and phishing scams against others.
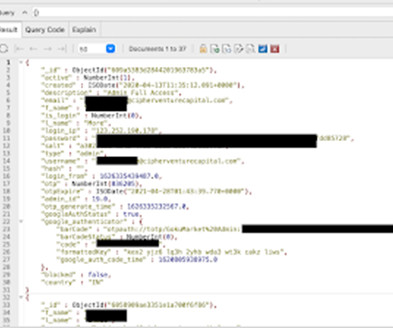
Security Affairs
DECEMBER 15, 2023
Businesses employ MongoDB to organize and store large swaths of document-oriented information, and in GokuMarket’s case, the details of over a million customers and admin users. The leak comes after the team discovered an unprotected MongoDB instance, which stored information on GokuMarket crypto exchange users.

Security Affairs
FEBRUARY 12, 2024
Once they’re in, they can grab your emails, usernames, passwords, and more. They might even lock you out of your own accounts by resetting your passwords. While they can’t directly read your password, they can still download malware or gather enough information to steal your identity.

CyberSecurity Insiders
JUNE 19, 2022
There are several types of phishing attacks, which are just one form of cybercrime. . A phishing attack takes place when a criminal pretends to be someone they’re not to trick people into giving over their personal information, such as their credit card details. Email phishing is also known as deception phishing.

Webroot
FEBRUARY 15, 2024
Protect yourself by shredding documents with any personal information, and, when possible, avoid sharing this information over the phone or via email. Use strong and unique passwords Passwords are your first line of defense to protecting your online accounts from hackers.

SecureWorld News
AUGUST 2, 2021
Earlier this year, Robinhood sent out a message to its users, warning of some phishing emails claiming to be a "Security Alert" with links to fake Robinhood websites. Phishing attempts come via email where scammers use different social engineering tactics to pose as a reputable sender like the IRS, your bank or brokerage firm.

Hot for Security
JULY 2, 2021
According to Bitdefender Antispam Lab researchers, cyber thieves are actively targeting DocuSign and Sharepoint users in phishing attacks designed to mimic legitimate correspondence from the two web-based platforms. The phishing attack spotted on June 24 appears to have originated from the United States.

Webroot
MAY 9, 2024
From important resumes and portfolios to personal documents, your digital footprint needs robust protection. Real-time antivirus protection Install robust antivirus software that provides continuous protection against emerging threats like malware, ransomware, and phishing scams.

CyberSecurity Insiders
JANUARY 11, 2022
Are you a user of Google Documents aka Google Docs? Then you might have become a victim to a spear-phishing scam that steals people’s login credentials. as most of the services offered by Alphabet Inc’s subsidiary can be accessed using a single login username and password.

The Last Watchdog
SEPTEMBER 25, 2023
According to Verizon’s 2023 Data Breach Investigations Report, 74% of breaches were caused by human error, with phishing and text message phishing scams being some of the leading causes. Taking an active role Your cybersecurity policy should address your employees and technology systems. Employee training is crucial.

Thales Cloud Protection & Licensing
OCTOBER 25, 2023
Many organizations train employees to spot phishing emails, but few raise awareness of vishing phone scams. Most people are familiar with the term phishing, but not everyone knows about vishing. It is a type of fraudulent activity that falls under the general phishing category and aims to achieve the same objectives.

Malwarebytes
SEPTEMBER 25, 2023
Researchers at Perception Point recently documented a sophisticated phishing campaign targeting hotels and travel agencies. To add a touch of legitimacy and to evade detection, they even provide the hotel representative with a password to unlock these so-called “important files.” Never click on unsolicited links.

SiteLock
AUGUST 27, 2021
In fact, 97% of us can’t tell a phishing email from a legitimate one. Cybercriminals know this, which is why phishing attacks account for more than 80% of reported security incidents and why 54% of companies say their data breaches were caused by “negligent employees. ”. Humans can be distracted, intimidated and especially – misled.

Malwarebytes
FEBRUARY 14, 2022
Today is Valentine’s Day, so we thought we’d show you how cybercriminals use special times like this one for phishing attacks. The email urges them to open an attached file, and also contains well formatted content that tries to divert attention from the real scam: Phising email. This malicious document is an HTML file.

SecureList
NOVEMBER 23, 2022
The risk of being scammed runs even higher. While on ordinary days, the customer can easily see that if the product is too cheap, it is most likely a scam, during the Black Friday sales, it gets harder to tell. Over the first ten months of 2022, Kaspersky prevented 38,596,555 financial phishing attacks. Methodology.

Identity IQ
FEBRUARY 16, 2024
How Does a Phone Cloning Scam Work? Change your passwords on the apps on your phone every couple of months. Sometimes scammers are just waiting for the right moment to attack, but without the password they are less likely to be able to access your information. But it is possible.
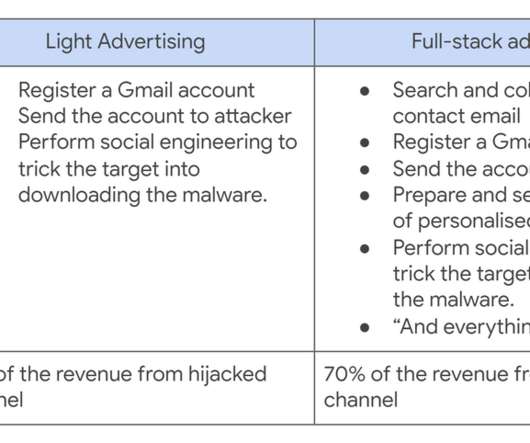
Security Affairs
OCTOBER 20, 2021
A Cookie Theft malware was employed in phishing attacks against YouTube creators, Google’s Threat Analysis Group (TAG) warns. Financially motivated threat actors are using Cookie Theft malware in phishing attacks against YouTube creators since late 2019. ” reads the analysis published by Google TAG.

Security Through Education
JANUARY 18, 2023
Impersonation Scams. These range from simple to sophisticated scams to convince you they are genuine, in hopes that you feel comfortable sharing personal or financial information whether on the phone, via email, or text. Although BEC attacks may be targeted at business, they can also be used to scam individual people.
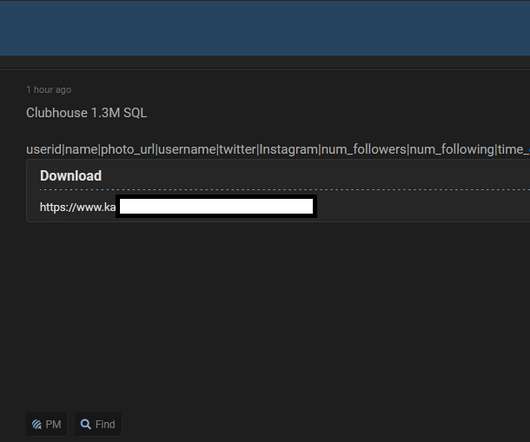
Security Affairs
APRIL 11, 2021
Leak data could be abused by threat actors to carry out malicious activities, such as phishing/spear-phishing attacks, identity theft, and scams. Using a strong and unique password for each web service, a password manager could help you. ” continues the experts.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content