Teach a Man to Phish and He’s Set for Life
Krebs on Security
AUGUST 4, 2023
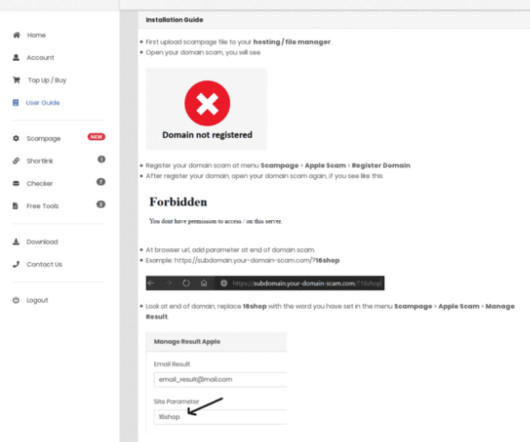
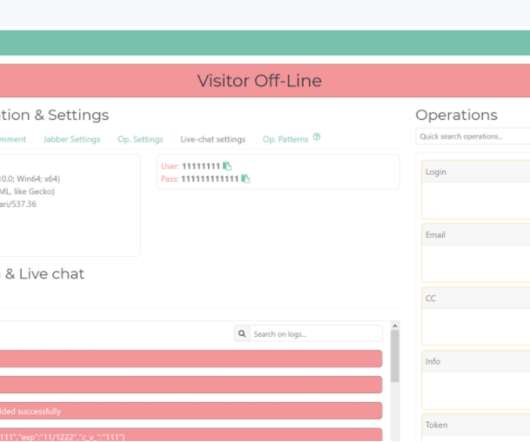
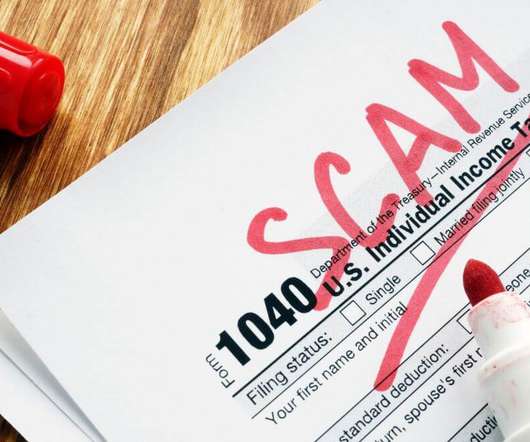
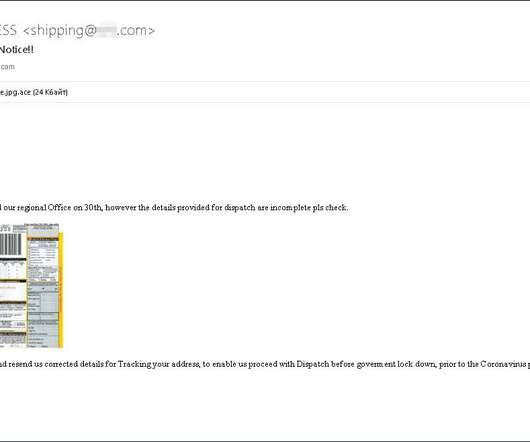
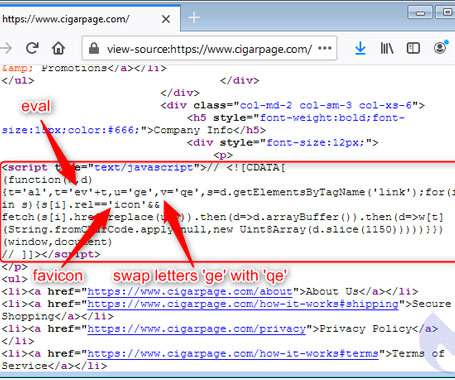
One frustrating aspect of email phishing is the frequency with which scammers fall back on tried-and-true methods that really have no business working these days. The file included in this phishing scam uses what’s known as a “right-to-left override” or RLO character.







































Let's personalize your content