City of Pensacola Hit By Cyberattack Following Shooting
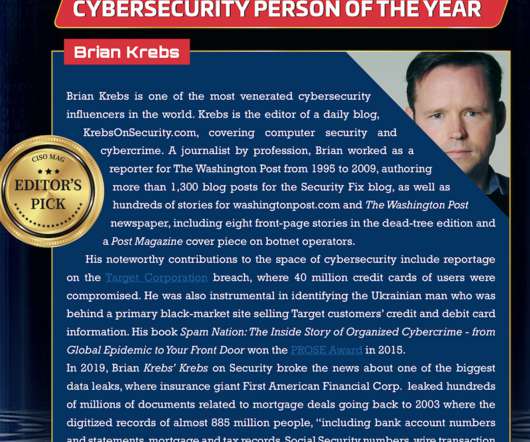
Adam Levin
DECEMBER 10, 2019
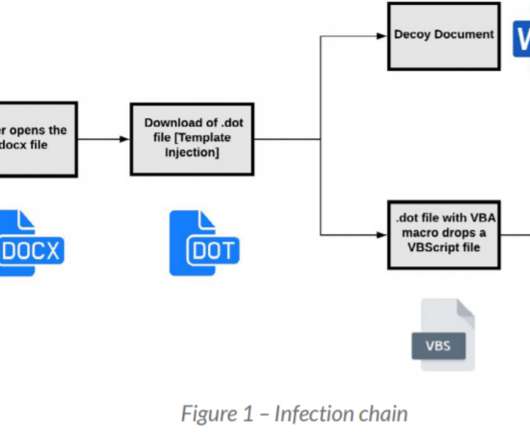
Pensacola, FL was hit by a cyberattack in the wake of what has been described as a terrorist shooting. “The city of Pensacola is experiencing a cyberattack that began this weekend that is impacting our city network, including phones and email at City Hall and some of our other buildings,” said Mayor Grover Robinson. . The cyberattack began early Saturday morning days after a shooting at the nearby Pensacola Naval Air Station that left four dead and eight wounded.




































Let's personalize your content