Overcoming the Challenges of Enterprise Key Management
Security Boulevard
OCTOBER 1, 2021
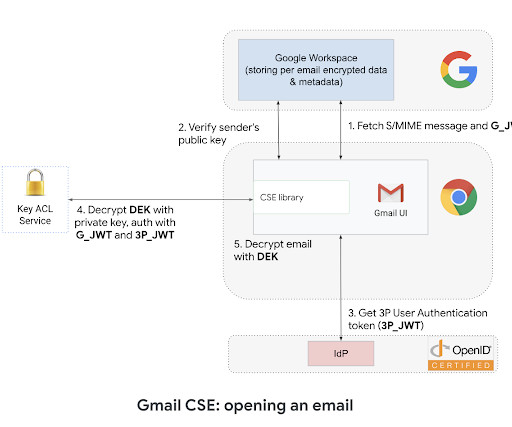
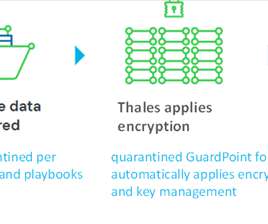
Let’s face it: Encryption key management can seem daunting. Sure, it’s easy to connect a hardware security module (HSM) to a database and generate a key, but that’s not how it works in the real world, where mission-critical cryptography is needed and required. Let’s talk pain points and dispel some of the myths.







































Let's personalize your content