New Intel CPU-level threat detection capabilities target ransomware
CSO Magazine
JANUARY 19, 2021
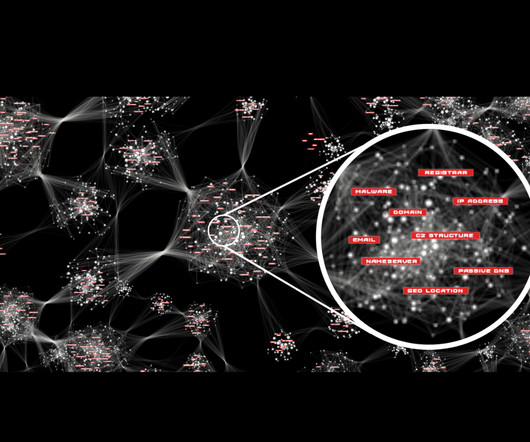
Security vendors can now leverage new telemetry and machine learning processing capabilities built into Intel's 11th Gen mobile processors to better detect and block sophisticated ransomware programs that attempt to evade traditional detection techniques. To read this article in full, please click here















































Let's personalize your content