More Than 90 Percent of Malware in Q2 Came Via Encrypted Traffic: WatchGuard
eSecurity Planet
OCTOBER 4, 2021
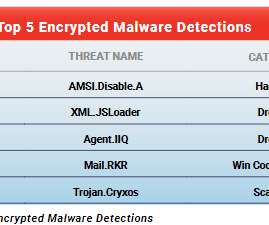
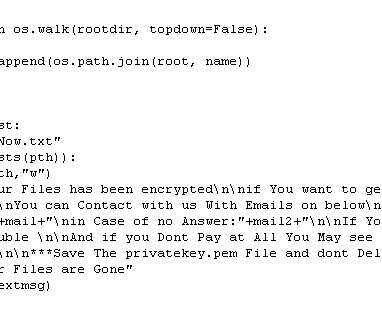
percent of all malware detected on networks of WatchGuard Technologies customers in the second quarter came over encrypted connections, raising the security risk for the 80 percent of such organizations that lack processes for decrypting and scanning HTTPS traffic for threats. Malware in Encrypted Traffic. AMS.Disable.A
















































Let's personalize your content