Working Remotely? Remember to Secure Your Webcam
Adam Levin
MARCH 17, 2020
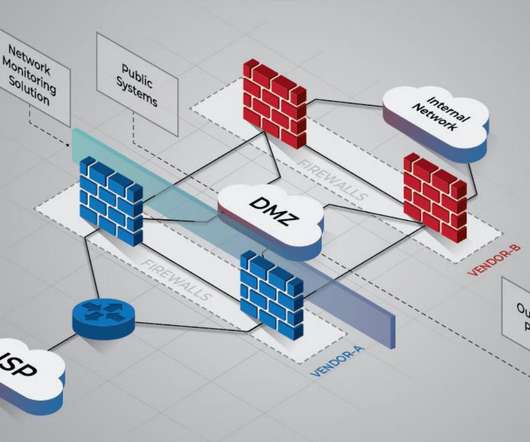
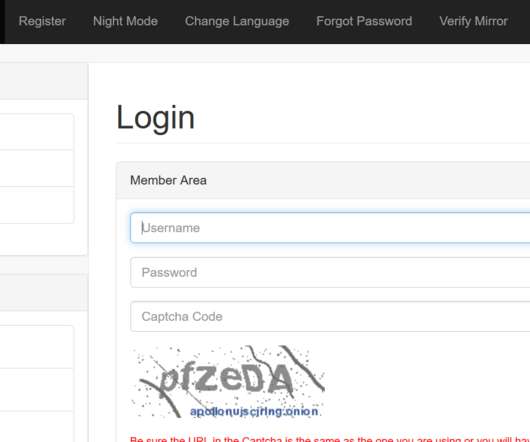
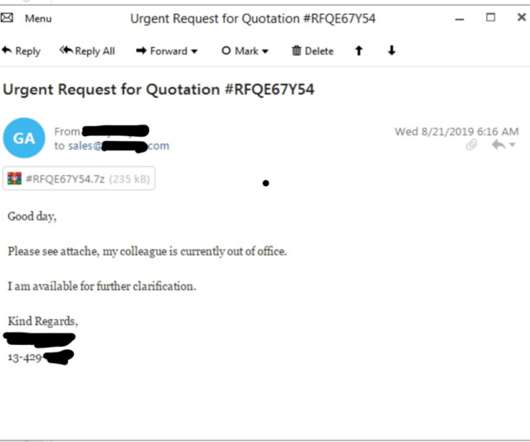
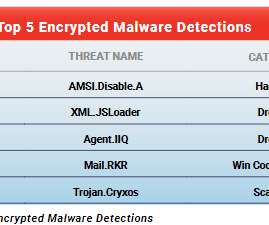
Internet of Things (IoT) devices in general have earned a reputation for poor cybersecurity, and internet-connected cameras are no exception. Case in point: unsecured webcams make up the top three out of the five most popular searches on Shodan , an IoT-centric search engine that specializes in identifying unsecure devices online.












































Let's personalize your content