New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. As with the rest of the IoT landscape, there's a lot of scope for improvement here and also just like the other IoT posts, it gets very complex for normal people very quickly.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
APRIL 30, 2024
The post Brits Ban Default Passwords — and More IoT Stupidity appeared first on Security Boulevard. The UK’s Product Security and Telecommunications Infrastructure Act aims to improve the security of net-connected consumer gear.

IT Security Guru
JANUARY 26, 2024
The arrival of the IoT has made fleet management systems very popular among organizations that have a fleet of vehicles as part of their operations. Nevertheless, the development of IoT and fleet management systems brings up issues with cybersecurity risks.

Security Affairs
AUGUST 17, 2021
FireEye Mandiant researchers have discovered a critical vulnerability in the Kalay cloud platform that exposes millions of IoT devices to attacks. The flaw could be easily exploited by a remote attacker to take over an IoT device, the only info needed for the attack is the Kalay unique identifier (UID) of the targeted user.

Security Boulevard
JUNE 23, 2022
Why Businesses Can’t Afford Anything Less Than Zero Trust in IoT. The IoT Landscape and Threats. Considering the inherent insecurity of connected devices, the threats facing organizations today often involve weakly-defended IoT equipment as the first line of attack. 39% see malware and ransomware as their biggest risk.

Security Affairs
DECEMBER 30, 2023
The private data leak was identified on September 26th and indexed by public IoT search engines on the same day. The leak was caused by a misconfiguration on MongoDB, a document-oriented database platform, that left TuneFab’s data passwordless and publicly accessible. Total exposure time was no longer than 24 hours.

Malwarebytes
APRIL 30, 2021
BadAlloc is a large set of remote code execution (RCE) vulnerabilities found by Microsoft’s Section 52 : These remote code execution (RCE) vulnerabilities cover more than 25 CVEs and potentially affect a wide range of domains, from consumer and medical IoT to Industrial IoT, Operational Technology (OT), and industrial control systems.

SC Magazine
APRIL 30, 2021
The IoT security team at the Microsoft Security Response Center said vulnerabilities discovered affect at least 25 different products made by more than a dozen organizations, including Amazon, ARM, Google Cloud, Samsung, RedHat, Apache and others. A signage of Microsoft is seen on March 13, 2020 in New York City. Jeenah Moon/Getty Images).

eSecurity Planet
FEBRUARY 23, 2022
These are not uncommon risks. The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. Industries with very expensive operational technology (OT) and Internet of Things (IoT) devices, such as healthcare or industrial manufacturing, can be especially vulnerable.

CyberSecurity Insiders
APRIL 29, 2022
Identify assets and their associated risks. The best asset management software sets up a stock of your organization’s assets, phases of their entire life cycles, most recent software upgrades, the risks they could face, and the approaches to ensure their security. . . Handle the threats’ possible risks. .

The Security Ledger
JUNE 29, 2023
The post Episode 251: Kry10 CEO Boyd Multerer on building a secure OS for the IoT appeared first on The Security Ledger with Paul F. Related Stories Episode 250: Window Snyder of Thistle on Making IoT Security Easy Forget the IoT. billion active IoT endpoints. Click the icon below to listen.
Security Affairs
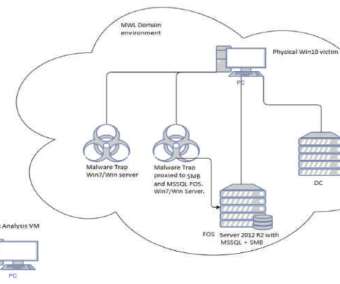
FEBRUARY 8, 2020
Hackers have infected with a piece of malware some IoT devices running Windows 7 designed by three of the world’s largest manufacturers. Security experts from TrapX reported that some IoT devices running Windows 7 have been infected with a piece of malware, is it a supply chain attack? Pierluigi Paganini.

The Last Watchdog
DECEMBER 31, 2019
Related: Good to know about IoT Physical security is often a second thought when it comes to information security. The internet of things (IoT) is widening the sphere of physical security as smart devices connected to business systems via the internet may be located outside of established secure perimeters.

Trend Micro
JUNE 14, 2023
We looked into the documented behavior of SeroXen malware and noted the inclusion of the latest iteration of the batch obfuscation engine BatCloak to generate a fully undetectable (FUD).bat bat loader.

SC Magazine
APRIL 14, 2021
The rapid growth of IoT over the past decade has sent billions of poorly-secured widgets and gadgets into the homes of consumers. Other IoT asset tracking schemes are also used by some security vendors to do asset inventory and keep track of specific products that may have been impacted by software or hardware security vulnerabilities.

Security Affairs
AUGUST 6, 2019
The STRONTIUM Russia-linked APT group is compromising common IoT devices to gain access to several corporate networks. Researchers at Microsoft observed the Russia-linked APT group STRONTIUM abusing IoT devices to gain access to several corporate networks. ” IoT risk must be taken seriously.
Security Boulevard
MARCH 1, 2024
EKEN IoT FAIL: Amazon, Sears and Shein still sell security swerving stuff. The post Cheap Video Doorbell Cams: Tools of Stalkers and Thieves appeared first on Security Boulevard.

ForAllSecure
APRIL 22, 2021
It seems everything smart is hackable, with IoT startups sometimes repeating security mistakes first made decades ago. The next day I cut the string, There's a parallel here to IoT light bulbs that change colors. And what then are the tools and knowledge that you need to get started hacking IoT devices. Funny thing.

ForAllSecure
APRIL 22, 2021
It seems everything smart is hackable, with IoT startups sometimes repeating security mistakes first made decades ago. The next day I cut the string, There's a parallel here to IoT light bulbs that change colors. And what then are the tools and knowledge that you need to get started hacking IoT devices. Funny thing.

Malwarebytes
APRIL 6, 2023
If someone finds out what it is, either from a list online or by socially engineering the victim, the game is indeed up. CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures. Well, one of the biggest is that hard coded credentials are used to talk to Nexx servers.

CyberSecurity Insiders
MAY 28, 2023
Social Engineering: Investigate the human element of cybersecurity by exploring social engineering techniques and tactics used to manipulate individuals. Internet of Things (IoT) Security: Examine the security risks associated with IoT devices, including privacy concerns, data integrity, and device authentication.

Cisco Security
NOVEMBER 3, 2021
OT bias: “Cybersecurity is just another engineering task”. Industrial control systems (ICS) engineers have dealt with complex process controls for years. As for safety and reliability engineering, invest in skills, people, and processes. Make it a priority to train every ICS engineer. Regularly assess and remediate risks.

Malwarebytes
MARCH 29, 2023
This attack relies on abusing the high sensitivity of microphones found in these IoT devices. In terms of being successful via NUIT attack, social engineering plays a large part. NUIT is designed to attack voice assistants with malicious commands remotely via the internet.

Adam Shostack
MARCH 5, 2020
.” I want to look at these as a specific way to express a threat model, which is threat modeling along the supply chain, talk about the proliferation of this different kind of model, and what it means for engineering. There’s a tremendous amount of guidance for IoT makers, and the lists are not well aligned.

SecureWorld News
OCTOBER 20, 2021
Cyberrisk is business risk. But how should we communicate this risk to the business, to clients, or to investors? Accenture annual report: risks we face from cyberattacks. However, we were most interested in seeing how Accenture articulated a particular business risk: the risk from a cyberattack.

Security Boulevard
SEPTEMBER 9, 2022
The post Cybersecurity Woes, Lax Patching Put Media Companies At Risk appeared first on Security Boulevard. The report revealed 30% of media vendors are susceptible to compromise via vulnerabilities discovered in their internet-facing publicly accessible footprints. The percentage of media vendors.

Adam Levin
MARCH 17, 2020
Internet of Things (IoT) devices in general have earned a reputation for poor cybersecurity, and internet-connected cameras are no exception. Case in point: unsecured webcams make up the top three out of the five most popular searches on Shodan , an IoT-centric search engine that specializes in identifying unsecure devices online.

Security Through Education
JANUARY 18, 2023
IBM describes the internet of things (IoT) as the “the concept of connecting any device … to the Internet and to other connected devices.” Basically, the IoT encompasses anything from smart microwaves and fridges to self-driving cars and fitness devices (to name a few). Impersonation Scams. Rosa Rowles.

CyberSecurity Insiders
MAY 21, 2023
This research can focus on developing automated tools and algorithms to identify emerging threats, assess their severity, and proactively mitigate potential risks. IoT Security: Examine the vulnerabilities and challenges associated with securing the Internet of Things (IoT) devices and networks.

Adam Levin
JANUARY 18, 2019
The leak itself was discovered by a researcher from the cybersecurity firm UpGuard, who detected it in early December on the IoT-centric search engine Shodan.
Security Affairs
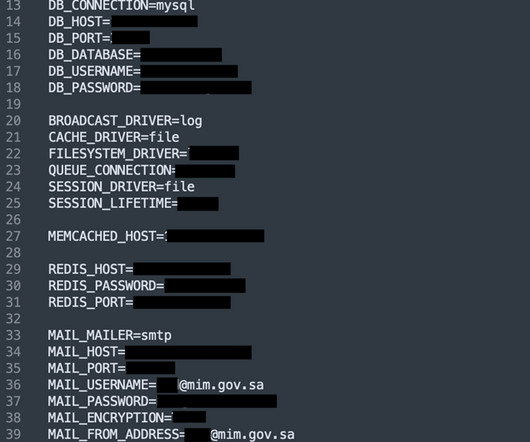
JANUARY 8, 2024
file was indexed by IoT search engines was in March 2022, meaning that the data was exposed for at least 15 months. With access to government SMTP credentials, attackers can impersonate government officials or employees to conduct social engineering attacks. According to the team, the first time the env.
Thales Cloud Protection & Licensing
SEPTEMBER 11, 2023
A cloud-native 5G turns (mainly) physical network components into software to connect subscribers in previously remote locations, support billions of IoT devices, and slice up bandwidth for enterprises to run their private networks. According to the GSMA, the world’s telcos will spend around $1 trillion on 5G launches.

SecureWorld News
JUNE 29, 2023
However, as reliance on mobile technology grows, so does the risk of cyber threats targeting these devices. These types of attacks often depend on social engineering to trick users into clicking malicious links or downloading malware.

The Last Watchdog
NOVEMBER 30, 2018
Grimm CEO Brain Demuth told me he hopes the work Grimm has commenced in Sparta will also contribute to generally elevating the security of all types of IoT systems. This is measured by the Society of Automotive Engineers’ zero to five scale of vehicle autonomy. Lifecycle risks.

The Last Watchdog
DECEMBER 13, 2023
Related: Why IoT standards matter Digital Trust refers to the level of confidence both businesses and consumers hold in digital products and services – not just that they are suitably reliable, but also that they are as private and secure as they need to be. Notable progress was made in 2023 in the quest to elevate Digital Trust.

eSecurity Planet
NOVEMBER 19, 2021
IoT security is where endpoint detection and response ( EDR ) and enterprise mobility management ( EMM ) meet the challenges of a rapidly expanding edge computing infrastructure. As the enterprise attack surface grows, IoT is yet another attack vector organizations aren’t fully prepared to defend.

SC Magazine
JUNE 17, 2021
The dashboard is designed for the biomedical engineering departments within the hospital environment. The flaw also maintains the account ID in a plaintext browser cookie, increasing the risk of exposure if a device is compromised.

The Security Ledger
NOVEMBER 26, 2018
And, just as important, what are the security implications of massively distributed IoT endpoints connected to capacious 5G cellular infrastructure? And, just as important, what are the security implications of massively distributed IoT endpoints connected to capacious 5G cellular infrastructure? Read the whole entry. »
CyberSecurity Insiders
OCTOBER 21, 2021
One of the biggest fears is that combining physical and cyber assets through OT/IT convergence creates new risks for OT, which is then subject to the same cyber threats as the other systems. Another step toward better security, he said, involves the concept of consequence-driven Cyber-informed Engineering (CCE).

Security Boulevard
MAY 17, 2024
The decision engine works out of the box as an immediate first-line defense against a network breach. Users can fine-tune the protective DNS engine through list management, content filtering policy and advanced rule sets. This is a passive or “test case” deployment to show you how the decision engine is evaluating certain queries.

Jane Frankland
MAY 8, 2024
With the emergence of new attack methods such as (but not limited to) ransomware, supply chain, fileless attacks, and IoT botnets, traditional cybersecurity measures are struggling to keep up. This not only frees up valuable time for security professionals to focus on more complex tasks but also reduces the risk of human error.
IT Security Guru
DECEMBER 1, 2022
After all, cybersecurity is a matter of proper human risk management. Several reports, such as the World Economic Forum Global Risk Report 2022 and Verizon’s 2022 Data Breach Investigations Report highlight that human error is by far the biggest and dominant cause of illicit actions and cybersecurity issues. Reduce human risk.

Malwarebytes
JULY 5, 2021
Researchers explore the insecure world of the subdomain (Source: Can i take your subdomain) Cyber insurance model is broken, consider banning ransomware payments (Source: The Register) How facial recognition solutions can safeguard the hybrid workplace (Source: Help Net Security) Capital One hacker faces fresh charges for 2019 hacking spree (Source: (..)
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content