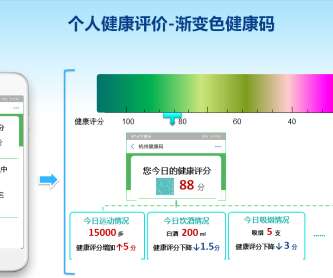
Experts Explain How to Bypass Recent Improvement of China’s Great Firewall
Security Affairs
JANUARY 31, 2021
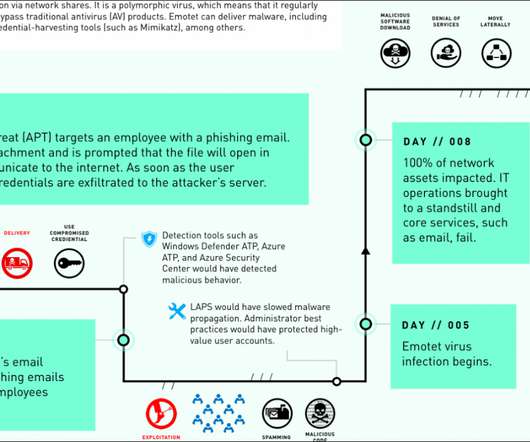
Experts from Great Firewall Report analyzed recent upgrades to China’s Great Firewall and revealed that it can be circumvented. Members of the Great Firewall Report group have analyzed the recent improvement implemented for China’s Great Firewall censorship system and revealed that it is possible to bypass it.






















Let's personalize your content