ESET detailed a flaw that could allow a bypass of the Secure Boot in UEFI systems
Security Affairs
JANUARY 17, 2025
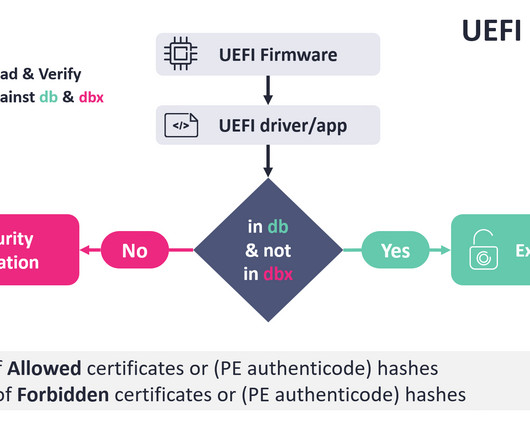
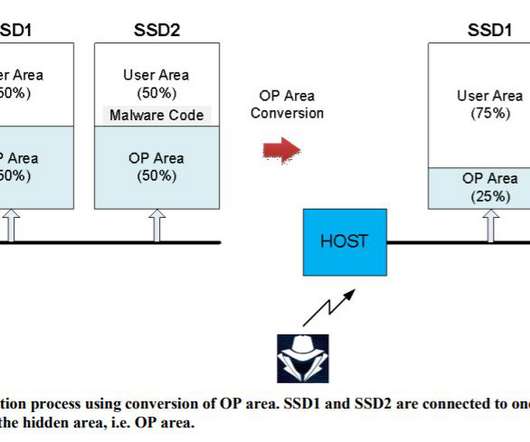
ESET disclosed details of a now-patched vulnerability, tracked as CVE-2024-7344 (CVSS score: 6.7), that could allow a bypass of the Secure Boot mechanism in UEFI systems. The Unified Extensible Firmware Interface (UEFI) is a specification that defines a software interface between an operating system and platform firmware.



































Let's personalize your content