June 2023 Security Update for Android fixed Arm Mali GPU bug used by spyware?
Security Affairs
JUNE 7, 2023
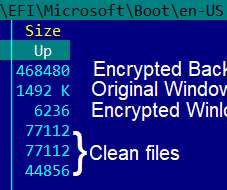
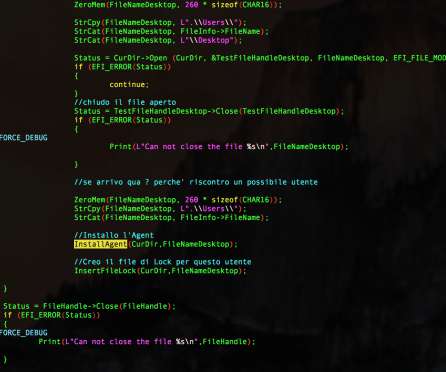
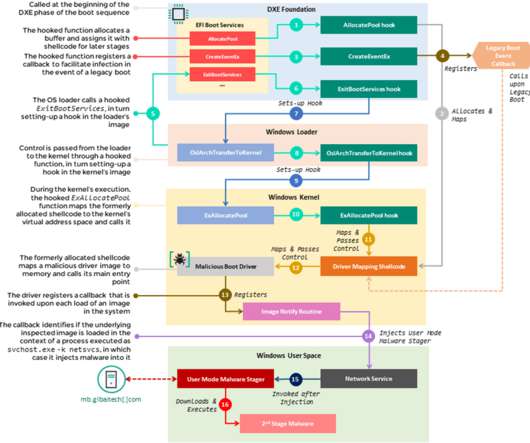
June 2023 security update for Android released by Google fixes about fifty flaws, including an Arm Mali GPU bug exploited by surveillance firms in their spyware. The flaw made headlines because it was exploited by surveillance firms for their spyware. This vulnerability grants the attacker system access.















Let's personalize your content