CISO workshop slides
Notice Bored
AUGUST 5, 2022
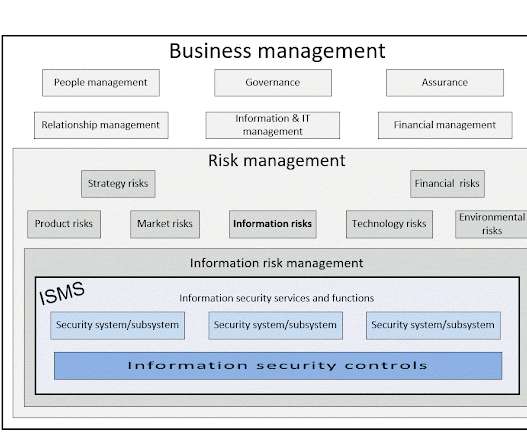
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.
Notice Bored
AUGUST 5, 2022
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.

ForAllSecure
APRIL 7, 2021
You’d think that having an amazing resume, a couple of bug bounties, or a CTF win would land you that dream infosec job. Welcome to the hacker mind and original podcast from for all secure, it's about challenging our expectations about the people who hack for a living. There's a serious shortage of InfoSec professionals.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

ForAllSecure
APRIL 7, 2021
You’d think that having an amazing resume, a couple of bug bounties, or a CTF win would land you that dream infosec job. Welcome to the hacker mind and original podcast from for all secure, it's about challenging our expectations about the people who hack for a living. There's a serious shortage of InfoSec professionals.

ForAllSecure
MARCH 14, 2022
Can you hack an airplane? Vamosi: Maybe you remember this: In 2014, researchers Charlie Miller and Chris Valasek succeeded in hacking a Jeep Cherokee while a reporter was driving it on a freeway during rush hour in St Louis, Missouri. So, given that we can now hack into cars remotely, could we hack into other systems as well?

ForAllSecure
SEPTEMBER 10, 2021
PPP wanted to give their past high school selves the infosec education they didn’t have. Megan Kerns of Carnegie-Mellon University joins The Hacker Mind to talk about the early days and the continued evolution of this popular online infosec competition site. in InfoSec however, learning happens 365 days a year.

The Security Ledger
SEPTEMBER 4, 2019
In July, the Federal Trade Commission hosted a workshop dubbed “ Nixing the Fix ” that delved into industry restrictions on repair. Then, in August, right to repair advocates (including yours truly) traveled to Las Vegas to speak as part of Ethics Village at the annual DEF CON hacking conference.

Troy Hunt
JANUARY 10, 2018
Which brings us back to Aadhaar and some rather unpleasant headlines of late, particularly the likes of The World's Largest Biometric ID System Keeps Getting Hacked. They claim that they're hack-proof. But claiming the service is "hack-proof", that's something I definitely have an issue with. Can you prove otherwise?
Let's personalize your content