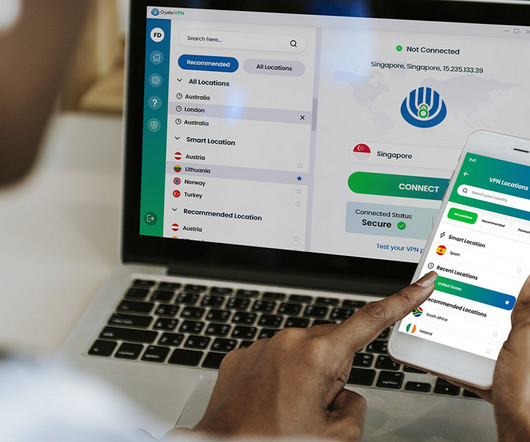
Malwarebytes acquires AzireVPN to fuel additional VPN features and functionalities
Malwarebytes
NOVEMBER 7, 2024
Today I have great news to share: We’ve acquired AzireVPN, a privacy-focused VPN provider based in Sweden. Malwarebytes has long been an advocate for user privacy (think Malwarebytes Privacy VPN and our free web extension Malwarebytes Browser Guard). What does this mean for existing Malwarebytes Privacy VPN customers?







































Let's personalize your content