Next-Generation Firewalls: A comprehensive guide for network security modernization
CyberSecurity Insiders
JUNE 20, 2023
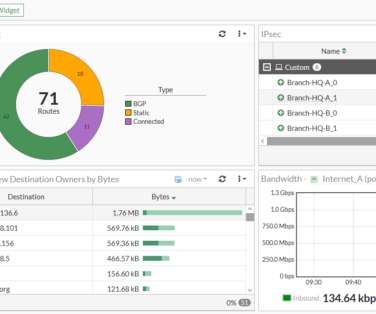
Next-Generation Firewalls (NGFWs), free from legacy technology constraints, take advantage of significant advancements in computational power, memory, and storage. NGFWs boast critical security features such as intrusion prevention, VPN, anti-virus, and encrypted web traffic inspection. Ready to Enhance Your Firewall Protection?









































Let's personalize your content