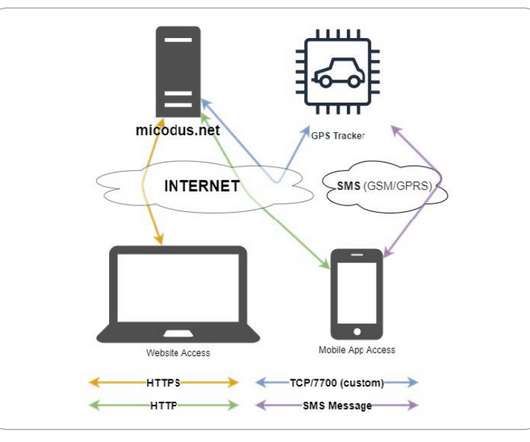
Verkada Surveillance Hack, Breach Highlights IoT Risks
Security Boulevard
MARCH 14, 2021
reported a breach of customer surveillance data to the U.S. The post Verkada Surveillance Hack, Breach Highlights IoT Risks appeared first on Security Boulevard. The post Verkada Surveillance Hack, Breach Highlights IoT Risks appeared first on Security Boulevard.











































Let's personalize your content