News alert: Arsen’s rolls out AI-powered phishing tests to improve social engineering resilience
The Last Watchdog
MARCH 24, 2025
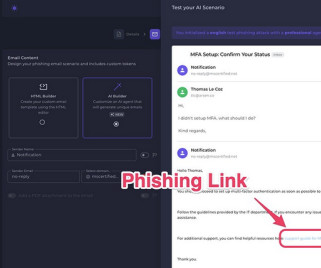
24, 2025, CyberNewswire — Arsen , a leading cybersecurity company specializing in social engineering defense, today announced the full release of Conversational Phishing, a groundbreaking feature embedded in its phishing simulation platform. Media contact: Thomas Le Coz, CEO, Arsen, marketing@arsen.co Paris, France, Mar.











































Let's personalize your content