Ivanti VPN Zero-Day Combo Chained ‘by China’
Security Boulevard
JANUARY 12, 2024
The post Ivanti VPN Zero-Day Combo Chained ‘by China’ appeared first on Security Boulevard. Under active exploitation since last year—but still no patch available.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
JANUARY 12, 2024
The post Ivanti VPN Zero-Day Combo Chained ‘by China’ appeared first on Security Boulevard. Under active exploitation since last year—but still no patch available.

eSecurity Planet
JANUARY 11, 2024
These devices exist outside of direct corporate management and provide a ransomware gang with unchecked platforms for encrypting data. Ransomware remains just one of many different threats and as security teams eliminate key vectors of attack, adversaries will shift tactics. How does remote encryption work?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
JUNE 21, 2021
The Taiwanese memory and storage chip maker ADATA was hit by the Ragnar Locker ransomware gang that also published more than 700GB of stolen data. The Ragnar Locker ransomware gang has published on its leak sites more than 700GB of data stolen from Taiwanese memory and storage chip maker ADATA. Consider installing and using a VPN.

Security Boulevard
MAY 12, 2021
The good thing is that with a virtual private network (VPN), you can protect your information from unauthorized persons to regain your privacy online. The post Why VPN Is Vital in Securing Your Online Privacy appeared first on CCSI. Well, that is fair given the kind of forces arrayed against your privacy.
Security Affairs
NOVEMBER 23, 2020
FBI is warning private industry partners of a surge in Ragnar Locker ransomware activity following a confirmed attack from April 2020. Federal Bureau of Investigation (FBI) issued a flash alert (MU-000140-MW) to warn private industry partners of an increase of the Ragnar Locker ransomware activity following a confirmed attack from April 2020.

eSecurity Planet
OCTOBER 20, 2021
Recent news headlines have shown how vulnerable even large companies with many resources at their disposal are to ransomware. One vendor says application security may be the key to stopping ransomware. Preventing Ransomware with Application Security. How Ransomware Accesses a Network.

Malwarebytes
JULY 15, 2021
SonicWall has issued an urgent security notice warning users of unpatched End-Of-Life (EOL) SRA & SMA 8.X X remote access devices that they have been made aware of an imminent ransomware campaign using stolen credentials. SonicWall is a company that specializes in securing networks. Security devices as a way in.

Security Affairs
MARCH 8, 2022
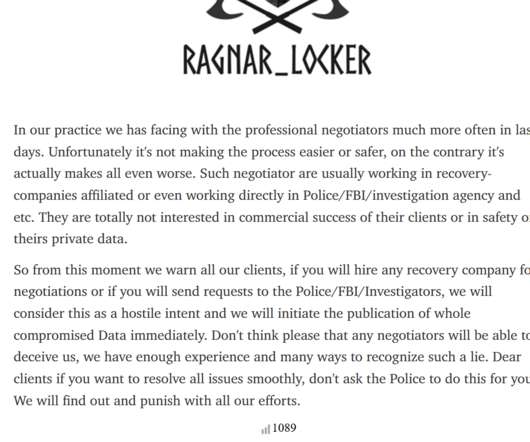
The US FBI warns that the Ragnar Locker ransomware gang has breached the networks of at least 52 organizations from multiple US critical infrastructure sectors. “RagnarLocker ransomware actors work as part of a ransomware family, frequently changing obfuscation techniques to avoid detection and prevention.”

eSecurity Planet
JULY 12, 2022
The first signs of the ransomware attack at data storage vendor Spectra Logic were reports from a number of IT staffers about little things going wrong at the beginning of the day. Screens then started to display a ransom demand, which said files had been encrypted by the NetWalker ransomware virus. The ransom demand was $3.6

Malwarebytes
MAY 23, 2023
The Cybersecurity and Infrastructure Security Agency (CISA) has updated its #StopRansomware guide to account for the fact that ransomware actors have accelerated their tactics and techniques since the original guide was released in September of 2020. Anomalous VPN device logins or other suspicious logins. Prevent intrusions.

eSecurity Planet
SEPTEMBER 5, 2023
Major cybersecurity events in the last week make clear that hackers just keep getting savvier — and security teams need to be vigilant to keep up. Ransomware groups continue to exploit unpatched vulnerabilities. Now ransomware attackers, possibly affiliated with FIN8, are exploiting unpatched Citrix products to launch attacks.

Security Boulevard
JUNE 11, 2021
Senate committee that the ransomware attack that disrupted fuel distribution to the majority of the eastern United States was caused by attackers stealing a single password that protected the enterprise’s VPN. “In Colonial Pipeline CEO Joseph Blount told a U.S. infrastructure. .

The Last Watchdog
DECEMBER 13, 2020
Gartner refers to this as the Secure Access Service Edge (SASE), which is a framework combining the functionality of Wide Area Network (WAN) with network security services to shield against any cyber threats or cloud-enabled SaaS. It incorporates zero-trust technologies and software-defined wide area networking (SD-WAN).

Security Affairs
JUNE 23, 2021
A critical vulnerability, tracked as CVE-2021-20019 , in SonicWall VPN appliances was only partially patched last year and could allow a remote attacker to steal sensitive data. The flaw resides in the HTTP/HTTPS service used for product management as well as SSL VPN remote access. “An SecurityAffairs – hacking, ransomware).
Security Affairs
SEPTEMBER 7, 2021
The Ragnar Locker ransomware operators threaten to leak stolen data if the victims attempt to contact law enforcement agencies. The Ragnar Locker ransomware gang is adopting a new technique to force victims to pay the ransom, the operators threaten to leak stolen data if the victims contact law enforcement agencies. Pierluigi Paganini.

eSecurity Planet
AUGUST 28, 2023
They shouldn’t be connected to any networks because of the risk they still pose, despite attempted patches. August 24, 2023 Akira ransomware targeting Cisco, but MFA helps Akira ransomware groups have been exploiting Cisco’s virtual private network ( VPN ) tools.

SC Magazine
FEBRUARY 17, 2021
Growing security risks have prompted companies to move away from virtual private networks (VPNs) in favor of a zero-trust model. Most organizations, 72 percent, plan to ditch VPNs , according to Zscaler’s 2021 VPN Risk Report , which found that 67 percent of organizations are considering remote access alternatives.

eSecurity Planet
AUGUST 28, 2023
They shouldn’t be connected to any networks because of the risk they still pose, despite attempted patches. August 24, 2023 Akira ransomware targeting Cisco, but MFA helps Akira ransomware groups have been exploiting Cisco’s virtual private network ( VPN ) tools.

eSecurity Planet
AUGUST 21, 2023
Note that not all of these venues are inherently or perfectly secure — they have vulnerabilities and require additional protective measures. Even VPN, while marketed as a security tool, has weaknesses of its own. Why Is Securing Access for Remote Workers So Important? Read more about the different types of remote access.

CyberSecurity Insiders
DECEMBER 24, 2021
Some of the issues faced by cybersecurity professionals in 2022 will include (but are not limited to) the evolving landscape of privacy (especially related to COVID-19 tracing), ransomware and the ongoing necessity for remote access. Remote access, 5G, and VPN. SASE (Secure Access Service Edge). Secure Web Development.

eSecurity Planet
MARCH 14, 2023
Network security creates shielded, monitored, and secure communications between users and assets. Securing the expanding, sprawling, and sometimes conflicting collection of technologies that make up network security provides constant challenges for security professionals.

SecureWorld News
JULY 27, 2021
We are still in the middle of the aftermath of the Colonial Pipeline ransomware incident. In one of the lawsuits, North Carolina gas station EZ Mart brings a Class Action Complaint against Colonial Pipeline, alleging the company's failure to properly secure its pipeline, which negatively affected the business and 11,000 other gas stations.

eSecurity Planet
APRIL 26, 2024
Network security architecture is a strategy that provides formal processes to design robust and secure networks. Effective implementation improves data throughput, system reliability, and overall security for any organization.

eSecurity Planet
MARCH 17, 2023
Whether you’re operating a global enterprise network or a small family business, your network’s security needs to be optimized with tools, teams, and processes to protect customer data and valuable business assets. Many of these tools protect resources connected to networks, thus shutting down threats as early as possible.

eSecurity Planet
FEBRUARY 16, 2024
In November 2021, the FBI disclosed a FatPipe VPN exploit that enabled backdoor access via web shells. It’s an in-depth assessment of the target’s network infrastructure, with a focus on discovering vulnerable devices such as routers and VPNs. Read the common types of network security solutions next.

eSecurity Planet
OCTOBER 28, 2022
The obvious but still valuable recommendation is to check any code before running it on your machine, especially when it’s for an exploit kit or ransomware. Most security experts recommend using separate environments for sensitive activities and daily tasks. How to Avoid Malicious PoCs.

eSecurity Planet
MARCH 16, 2023
Network security threats weaken the defenses of an enterprise network, endangering proprietary data, critical applications, and the entire IT infrastructure. This guide to major network security threats covers detection methods as well as mitigation strategies for your organization to follow.

CyberSecurity Insiders
APRIL 17, 2023
The first security measure businesses adopted during the pandemic was using VPNs that allowed employees to work remotely while still enjoying connectivity and security. To combat these vulnerabilities, organizations must consider establishing hybrid workplace network security.

SecureWorld News
NOVEMBER 12, 2020
Ransomware. During the reporting period, Emotet evolved into a botnet, increased its activity, and initiated new localized spam campaigns with spear-phishing functionality to install ransomware or steal information.". Researchers also found that file-less ransomware skyrocketed and that trend makes sense. Identity Theft.
eSecurity Planet
MARCH 16, 2023
Block TCP 445/SMB outbound from your network by using a perimeter firewall, a local firewall, and via your VPN settings. ” Also read: Ransomware Protection: How to Prevent Ransomware Attacks SmartScreen Zero-Day The SmartScreen zero-day, CVE-2023-24880 , is also being actively exploited but has a much lower CVSS score of 5.4.

Security Boulevard
AUGUST 12, 2022
Cisco got hacked by a ransomware gang—a broker for the UNC2447 threat actor, which has “a nexus to Russia.”. The post Cisco Pwned by ‘Russian’ Gang — Data Leaked, Egg on Face appeared first on Security Boulevard.
eSecurity Planet
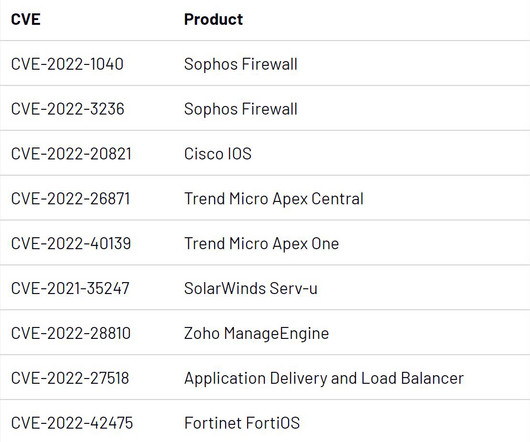
MARCH 27, 2023
A quarter were financially motivated, and three of those were linked to ransomware operations. Targeting Firewalls and IPS/IDS Appliances In the case of CVE-2022-42475, a flaw in Fortinet’s FortiOS SSL-VPN, Mandiant observed a Chinese state-sponsored group exploiting the vulnerability in late 2022.

Security Boulevard
JUNE 11, 2021
On top of that, you should install a virtual private network (VPN), which will disguise your location and encrypt all of your precious information. Along with keeping your data secure, you will also want to keep all-important personal and client data stored on a dependable backup server.

Malwarebytes
JUNE 7, 2021
Malicious hackers might use tools like computer viruses, spyware, ransomware, Trojan horses, and more to further their goals. An unethical hacker can use many techniques and tools to breach your computer or device’s network security. How do I protect myself from a hacker?

eSecurity Planet
MARCH 1, 2023
Most network access control (NAC) solutions support wireless networks in addition to wired ones, and many Wi-Fi routers include access controls like allowlisting or denylisting. Device security is also an important part of wireless network security. Segment parts of your network that are more sensitive than others.

eSecurity Planet
DECEMBER 2, 2022
Upon investigation, you discover it’s ransomware. You have the disaster recovery (DR) site, backups, and storage area network (SAN) snapshots. You look for your cold replica in your DR site, but like your production servers, it has also been encrypted by ransomware. Do you need to shore up email security?

Security Boulevard
MARCH 24, 2021
The Cybersecurity Cost of Human Error While many security executives agree that ransomware poses the greatest threat to security infrastructure, a majority believes that human error is the greatest risk to their business operations. Always use a virtual private network (VPN). Secure systems over cloud databases.

eSecurity Planet
SEPTEMBER 11, 2023
Android, Apple, Apache, Cisco, and Microsoft are among the names reporting significant security vulnerabilities and fixes in the last week, and some of those are already under assault by hackers. Here are some of the top vulnerabilities from the last week that security and IT teams should address. of the Atlas VPN Linux client.

Malwarebytes
OCTOBER 1, 2023
Speak to any organization infiltrated by ransomware—the most dangerous malware in the world—and they’ll be blunt: They’d do anything to avoid getting hit twice. But ransomware attacks have been ramping up in 2023 and reinfections are occurring all over the globe, forcing lean IT teams to prepare.

SecureList
MAY 12, 2021
As the world marks the second Anti-Ransomware Day, there’s no way to deny it: ransomware has become the buzzword in the security community. Yet, much of the media attention ransomware gets is focused on chronicling which companies fall prey to it. Part I: Three preconceived ideas about ransomware.

SC Magazine
MARCH 11, 2021
It also examined dozens of critical or high-impact vulnerabilities discovered throughout the past year, some of which have been turned into well-known exploits and others that are sitting quietly in the background, waiting to be weaponized for widespread use by the right hacking group or ransomware operator.
Malwarebytes
MARCH 9, 2022
In a FLASH publication issued by the FBI in coordination with DHS/CISA, the FBI says it has identified at least 52 organizations across 10 critical infrastructure sectors affected by RagnarLocker ransomware, including organizations in the critical manufacturing, energy, financial services, government, and information technology sectors.

eSecurity Planet
JULY 12, 2023
and thereby mitigating the vulnerability – a necessary step that could potentially impact performance, but that will ensure security and compliance until the server can be updated,” he said. . “This prevents the establishment of the secondary channel over UDP, eliminating the use of the deprecated DTLS 1.0

Security Boulevard
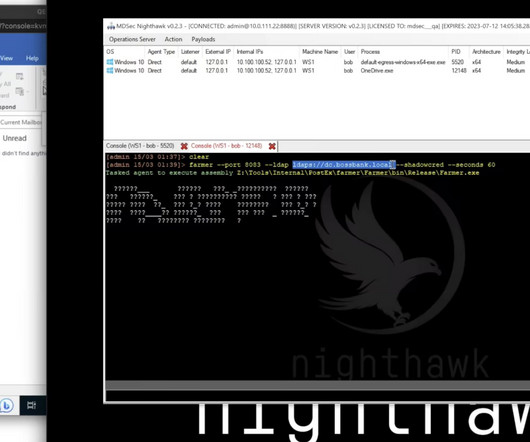
JULY 29, 2021
James Coote | Senior Consultant, F-Secure Consulting. Alfie Champion | Senior Consultant, F-Secure Consulting. Tracks : Network Security, Defense. Attackers are always looking for ways to get inside and move around your network undetected. Avoid Public WIFI and use mobile data always with a VPN.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content