CISO workshop slides
Notice Bored
AUGUST 5, 2022
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Notice Bored
AUGUST 5, 2022
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.

Troy Hunt
SEPTEMBER 17, 2019
Allow me to be controversial for a moment: arbitrary password restrictions on banks such as short max lengths and disallowed characters don't matter. Also, allow me to argue with myself for a moment: banks shouldn't have these restrictions in place anyway. 6 characters. for my *online banking*.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Troy Hunt
MARCH 13, 2020
I spend a good quarter hour at the start of this video talking about what I'll be doing, namely getting on with business and running a bunch of public workshops remotely in conjunction with Scott Helme. References You can register to do Scott Helme's and my "Hack Yourself First" workshop at NDC Copenhagen on April 1-2 right now!

Troy Hunt
NOVEMBER 17, 2019
References Scott Helme is running my Hack Yourself First workshop in Amsterdam on Dec 9 & 10 (he's getting awesome reviews on these too) Apparently, FinecoBank in Italy reckons you should Google your password and not use it if it appears 10 times or more (no, just don't) You'll also need to pay FinecoBank € 0.95

Troy Hunt
MAY 11, 2018
We cover off a bunch of bits and pieces related to things we're working on together (workshops and Report URI) as well as some (mostly) commonly held views about HTTPS, EV certs and visual indicators. Oh - and I forgot to mention killing off the non-anonymous endpoints for Pwned Passwords last week so that's in here this week too.

CyberSecurity Insiders
JUNE 13, 2023
Learn about strong password creation, multi-factor authentica-tion, secure browsing habits, and data encryption. Implement Strong Password Practices: Passwords serve as the first line of defense against unauthorized access to your online accounts. Utilize a password manager to securely store and generate strong passwords.

Troy Hunt
JANUARY 27, 2018
I talk about that below including the preceding days involving some pretty full on sledding in Norway, workshops, talks, ice, slush and snow. LastPass is sponsoring my blog this week (if you don't already have a password manager, you're doing it wrong!). iTunes podcast | Google Play Music podcast | RSS podcast.

Troy Hunt
FEBRUARY 23, 2019
Along with a private Sydney workshop earlier on, I'm talking about some free upcoming NDC meetup events in Brisbane and Melbourne and I'd love to get a great turnout for. In other news, there was old news appearing as new news about how hosed you are if your machine is compromised with the level of hosing extending to your password manager.
SecureWorld News
OCTOBER 13, 2022
In an effort to communicate the risks that come along with using internet-connected devices, the Council is gathering representatives from consumer product associations, technology think tanks, and manufacturing companies at the White House next week for a workshop. The move ties in nicely with October being Cybersecurity Awareness Month.
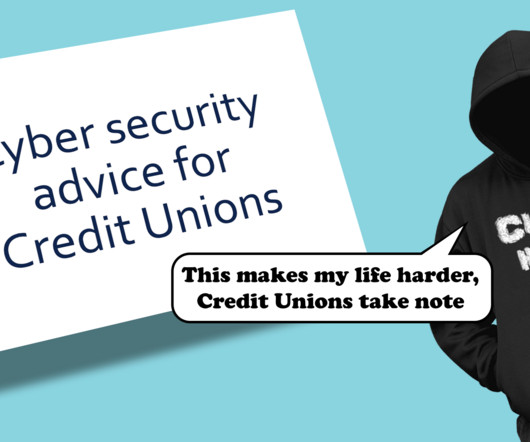
Pen Test Partners
FEBRUARY 19, 2024
credit unions, internal notes, and clients’ full names, home and email addresses, and plaintext passwords. Leverage trusted external partners for Risk Assessments, Team Training Workshops, TTX, bi-annual Penetration Tests, etc. Establish a continuous security mentality Security can’t simply be a point in time (e.g.,

Security Affairs
AUGUST 8, 2020
The analysis of the file system of the vehicle’s Telematics Control Unit (TCU), to which they gained access by obtaining an interactive shell with root privileges, they uncovered passwords and certificates for the backend server. ” continues the research. ” the paper concluded.

Hackology
NOVEMBER 15, 2023
The bedrock of these controls is enforcing password complexity requirements, ensuring that all users have unique, hard-to-crack passwords. While ensuring the set conditions are not so stringent that users start making sequential passwords which are even easier to brute-force. Yet, password measures alone may not suffice.

CyberSecurity Insiders
SEPTEMBER 24, 2021
Therefore, you need to invest in your employees by conducting cybersecurity workshops and training regularly. Let your staff know about the significance of maintaining strong and unique passwords. Create awareness about the IT policies surrounding data protection and loss. .

Troy Hunt
MARCH 1, 2018
My congressional testimony in the US was a very public example of that, less so are the dozens of conversations I've had in all sorts of settings including during conferences, workshops and over coffees and beers.

CyberSecurity Insiders
JUNE 17, 2023
These authentication factors can range from something you know (like a password), something you have (like a hardware token or a mobile device), to something you are (biometric data like fingerprint or face recognition). This makes unauthorized access exponentially more challenging, thereby offering enhanced protection against identity theft.

Identity IQ
SEPTEMBER 15, 2023
Teach them about the dangers of sharing personal information online and guide them in setting strong, unique passwords. Workshops or informational sessions about fraud prevention, perhaps given by community centers or local law enforcement, can be beneficial. When it comes to passwords, go the extra mile. Change them regularly.

CyberSecurity Insiders
MARCH 25, 2021
Although this does take time, with training and upskilling programs , insightful workshops, and “Hacker Fridays” (where employees can try to hack a specific smart device), team members will become more capable of dealing with the new diagnostics support work, as well as any general IoT problems. 5 Be aware of your operating landscape.

BH Consulting
AUGUST 9, 2022
The ongoing campaign has targeted more than 10,000 Office 365 organisations since September 2021, using ‘adversary in the middle’ (AiTM) sites to steal passwords and hijack login sessions. The two-year part-time course will mainly be delivered through distance learning, with occasional one-day workshops on campus.
Security Through Education
MARCH 3, 2021
For example, a phony email stating that your online bank account has been compromised and requires a new password will elicit fear in most people. In addition, the emotion of fear can be elicited by a phony email stating that your online bank account has been compromised and requires the password. Still on the fence about attending?

Identity IQ
JUNE 1, 2023
Phishing attacks refer to fraudulent attempts, usually through email or messaging platforms, to deceive individuals into revealing sensitive information like passwords, credit card details, or Social Security numbers. Use a password manager to securely store and manage your passwords. Phishing attacks.

Troy Hunt
DECEMBER 20, 2017
It was being sold for 5 Bitcoins: That's over US$80k in today's money but back then, it was only a couple of grand (which actually, seems like pretty good value for 167 million accounts and passwords stored as unsalted SHA1 hashes). When I run workshops , at the end of the second day I like to talk about automating security.

Troy Hunt
FEBRUARY 6, 2018
I've been giving a bunch of thought to passwords lately. Some won't let you paste a password. I particularly focused on how today's thinking is at odds with many of the traditional views of how passwords should be handled. Now, here's my great insight from all of this: Every single minimum password length is an even number!

eSecurity Planet
APRIL 12, 2024
Customize training materials to address these specific concerns, including data handling protocols, password management , and phishing attempt identification. Encourage regular talks, training, and awareness workshops to help integrate DLP practices into the organization’s culture.

Troy Hunt
JULY 12, 2019
So "Plan A" was to publish Pwned Passwords V5 on Tuesday but a last-minute check showed control characters had snuck in due to the quality (or lack thereof) of the source data. References Scott will be running my Hack Yourself First workshop in Glasgow next week (this is the last stop on the UK tour, get in while you still can!)
Krebs on Security
AUGUST 12, 2022
The DHS warning came in advance of a workshop to be held this weekend at the DEFCON security conference in Las Vegas, where a security researcher is slated to demonstrate multiple weaknesses in the nationwide alert system. It had the username and password for the system printed on the machine.

Thales Cloud Protection & Licensing
APRIL 7, 2022
The reputation is well-deserved when you consider that we (the cybersecurity team) tell users to create a unique password for each account to increase security. According to Gartner, 20 – 50% of help desk calls are for password reset – which is an expensive burden for any help desk.
Troy Hunt
APRIL 24, 2020
References The COVID19 Australia Twitter account is a great source of empirical data (we're weathering the pandemic exceptionally well down here) The next workshop I'll be doing is "in" Oslo for NDC in June (this will be my 7th NDC Oslo, just the first one, well, not actually in Oslo!) Nanoleaf is kinda cool ?? (I

Troy Hunt
SEPTEMBER 26, 2020
(I'll gradually go through the house and replace all the wall sockets with these) Was Activision "hacked" or do people just choose bad passwords?

Troy Hunt
NOVEMBER 25, 2020
I can't blame this on the teddy bears themselves, rather the fact that the MongoDB holding all the collected data was left publicly facing without a password. It made it easy for all the existing devices to jump onto the new network (I used the same password from the v1 network) and it gives me the option to segment traffic later on.

Troy Hunt
JANUARY 3, 2019
So yes, travel went up but I also did a bunch of remote workshops which helped keep that down, as well sending Scott Helme to run in-person ones that contributed to keeping me on Aussie soil. SSW in Sydney: How safe is your #password ?! TECHpalooza on the Gold Coast: We’ve got a password problem. troyhunt is here to help.
Duo's Security Blog
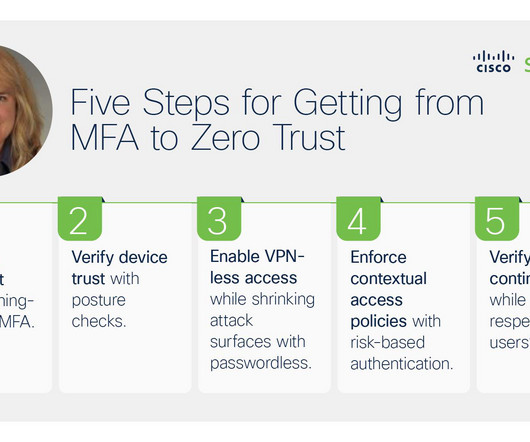
OCTOBER 6, 2023
Shrink the attack surface by reducing password usage with passwordless SSO and make it faster and more convenient for users to get to the apps they need – whether SaaS-based or private. For strategic guidance and access to hands-on labs, register for one of our free Zero Trust Workshops. ZTNA) – regardless of location or protocol.
eSecurity Planet
APRIL 14, 2023
By requiring users to provide two forms of authentication, such as a password and a security token , 2FA can significantly reduce the risk of unauthorized access to online accounts and other resources. Bot protection requires a multi-layered approach that involves a combination of these techniques and measures.

Jane Frankland
OCTOBER 17, 2023
Then there’s the promise of free content, software, and products; and using unsecured public wi-fi networks, or weak passwords. Alternatively, reusing passwords, sharing passwords; and simply ignoring browser software updates. Provide access to relevant training courses, certifications, workshops, or conferences.

Troy Hunt
DECEMBER 17, 2017
Let me demonstrate precisely the problem: have a look at this code from a blog post about how to build a password reset feature (incidentally, read the comment from me and you'll understand why I'm happy sharing this here): There are two SQL statements here: the first one is resilient to SQL injection. "god rights").
Troy Hunt
JANUARY 3, 2020
NewPassword: passw0rd ConfirmPassword: passw0rd This is a real request from my Hack Yourself First website I use as part of the workshops Scott Helme and I run. You can go and create an account there then try to change the password and watch the request that's sent via your browser's dev tools. Why is this possible?

eSecurity Planet
APRIL 9, 2024
Is there cybersecurity training on best practices, including setting strong passwords in accordance with the organization’s policy? Encourage strong password practices: Provide tips on how to create complex passwords and use password management tools. Teach them how to verify the sender’s address and URL.

Troy Hunt
JANUARY 10, 2018
Much of this is simply due to lack of awareness; I must have taught 50 security workshops where the vast majority of attendees had simply never heard of CSP before. This is poor form as it can break tools that encourage good security practices such as password managers. Let them paste passwords! Why do websites do this?

ForAllSecure
SEPTEMBER 21, 2021
Black Mirror brainstorms, a workshop in which you create Black Mirror episodes. Who else has access to something that's, that's not uncommon, interviewed that, for example, someone still had someone share Facebook passwords. Don't share your phone, don't share your password with your partner. Things are complicated.

McAfee
FEBRUARY 3, 2020
Global single sign-on services can ensure that users’ access is removed from all services when they leave the organization, as well as reduce the risk of data loss from password reuse. In a non-SSO service, users often call the helpdesk team when they’ve forgotten their passwords , so SSO has the added benefit of reducing call volume.

Pen Test Partners
OCTOBER 9, 2023
Mind maps can be a good way to collaboratively develop this phase within a threat modelling workshop. For example: a user enumeration vulnerability, a weak password policy, and a lack of brute force protection and lockout can still lead to an attacker gaining access to an account. Encryption is important when: Sending a password.
Duo's Security Blog
MARCH 3, 2021
The annals of cybersecurity are particularly filled with attacks that were facilitated by devices that didn’t have their data stores encrypted, devices that didn’t have their firewalls enabled, and devices that didn’t even have a viable password. Learn more by visiting Duo Zero Trust Security.

Troy Hunt
NOVEMBER 8, 2021
They'd left a MongoDB instance exposed to the public without a password and someone had snagged all their data. When someone passed me hundreds of thousands of records on kids taken from CloudPets a few years ago , I had a nightmare of a time getting in touch with the company. But I can make mistakes. Coding mistakes.

Troy Hunt
JUNE 10, 2019
Increasingly, I was writing about what I thought was a pretty fascinating segment of the infosec industry; password reuse across Gawker and Twitter resulting in a breach of the former sending Acai berry spam via the latter. And while I'm on Sony, the prevalence with which their users applied the same password to their Yahoo!

Adam Levin
AUGUST 21, 2019
A non-profit called the National Cyber Security Alliance offers a series of in-person, highly interactive and easy-to-understand workshops based on the National Institute of Standards and Technology (NIST) Cybersecurity Framework. Make sure employees know what good password practices look like. For-profit choices are legion.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content