WHEN IS CYBERSECURITY IS WEEK
Hacker's King
OCTOBER 26, 2024
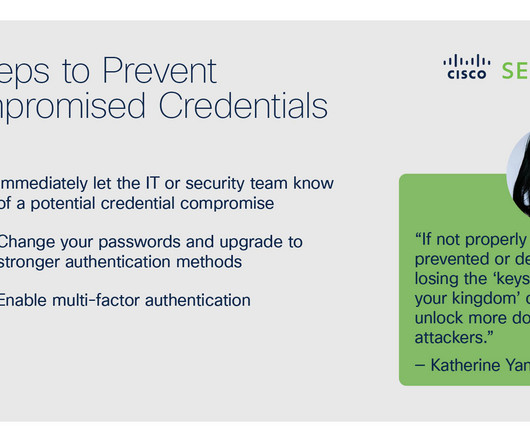
Activities during this week include engaging workshops, informative webinars, and community events, all designed to empower individuals with the knowledge and skills necessary to navigate today’s cyber threats effectively. Be Cautious with Email Attachments: Phishing attacks often come disguised as legitimate emails.







































Let's personalize your content