Secure Business-Critical Resources with a Web Application Firewall
Tech Republic Security
JULY 18, 2023
Request a demo of an Array web application firewall to learn how you can protect your business from DDoS & zero-day attacks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 request-a-demo
request-a-demo 
Tech Republic Security
JULY 18, 2023
Request a demo of an Array web application firewall to learn how you can protect your business from DDoS & zero-day attacks.

Troy Hunt
APRIL 1, 2023
Pwned Passwords has now surpassed 4 billion monthly requests! (I'm Book a demo today. Most of this week's video went on talking about the UniFi Dream Wall. What a unit! I mean it's big, but then it wraps a lot of stuff up in the one device too. Sponsored by: Kolide ensures only secure devices can access your cloud apps.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
JULY 18, 2023
Request a demo now. Array Networks offers SSL VPN gateways to meet a variety of needs for small and medium enterprises.

Tech Republic Security
JULY 18, 2023
Request a demo of load balancing from Array Networks, purpose-built for the requirements of small and medium enterprises.

Troy Hunt
JUNE 8, 2023
I spent most of this week's update on the tweaking I went through with Azure's API Management service and then using Cloudflare to stop a whole bunch of requests that really didn't need to go all the way to the origin (or at least all the way to the API gateway sitting in front of the origin Azure Function instance).
Troy Hunt
MARCH 10, 2023
Book a demo today. Amazing 😍 pic.twitter.com/wOl4kpK841 — Troy Hunt (@troyhunt) March 3, 2023 When I talked about the McLaren in this week's video, Frits made the comment "the smile on your face says it all", which absolutely nailed it. It's so much fun 😊 Less fun is dealing with Eye4Fraud.

NetSpi Technical
SEPTEMBER 22, 2023
Basics of Macros Gathering Dynamic Values Macros for Complex Situations Basics of Macros In this first video, I cover a couple of basics of Macros: what they are, why we might use them, and 2 demos of basic usage. Note that the tricky thing with that is the login request doesn’t contain a “Set-Cookie” header in the response.
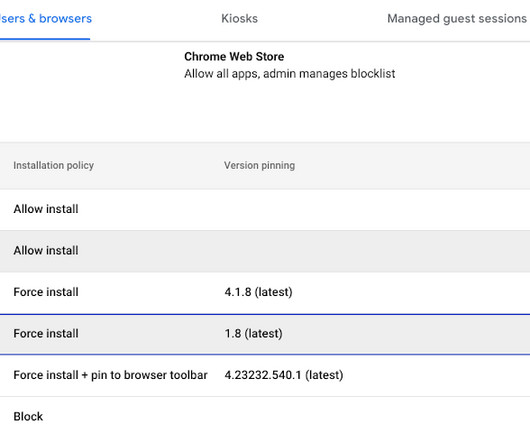
Google Security
JUNE 20, 2023
Extension workflow Extension workflow allows end users to request extensions for review. We recently added a prompt for business justification for documenting why users are requesting the extension. We recently added a prompt for business justification for documenting why users are requesting the extension.

Troy Hunt
JULY 12, 2018
So that's precisely what I've done - intercepted my own traffic passed over an insecure connection and put together a string of demos in a 24-minute video explaining why HTTPS is necessary on a static website. Here's the video and there's references and code samples for all the demos used immediately after that: HTTPS Is Easy.
Security Affairs
FEBRUARY 17, 2020
A serious flaw in the ThemeGrill Demo Importer WordPress theme plugin with over 200,000 active installs can be exploited to wipe sites and gain admin access to the site. Experts from the security firm WebARX have discovered a serious flaw in the WordPress theme plugin ThemeGrill Demo Importer with over 200,000 active installs.

Security Boulevard
FEBRUARY 14, 2024
How is FireMon Better Book a Demo Healthcare companies have a responsibility to protect sensitive patient data and ensure compliance with regulations like HIPAA. To learn more about how FireMon can help your healthcare organization, request a demo today. Why Act Now? Why Choose FireMon?
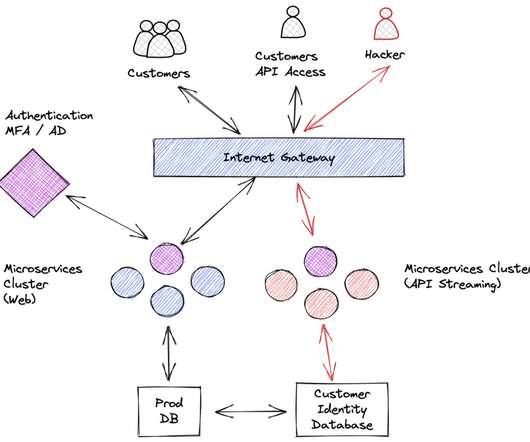
Security Boulevard
SEPTEMBER 26, 2022
Essentially anyone in public domain is allowed to send a request asking the server “fetch contact details for Optus customer with contactid=XXXXXXXXX”. Lack of authorization checks for every user request. Sending sensitive information in the URL of a request: When in doubt, send parameters within the body of a POST request.

Duo's Security Blog
FEBRUARY 19, 2024
Think of it like having a dedicated advocate behind the curtain who is highlighting the ideas that you’ve submitted as feature requests and proactively looking out for new functionalities that might be of interest to you or that might help you better achieve your security goals. It could be a combination of conversations and demos.

CyberSecurity Insiders
SEPTEMBER 23, 2021
In this demo, let's try capturing and analyzing ARP traffic. Find existing ARP cache -> Delete the existing one to understand the demo -> Check ARP cache for verification. Analyze an ARP Request. Click the ICMP echo-request packet from the Wireshark capture window and start observing the information.

CyberSecurity Insiders
MAY 12, 2023
Learn more about the benefits of compliance automation and then schedule a demo to see how you can streamline your audit processes. Learn more about the benefits of compliance automation and then schedule a demo to see how you can streamline your audit processes. Automation transforms the audit experience.
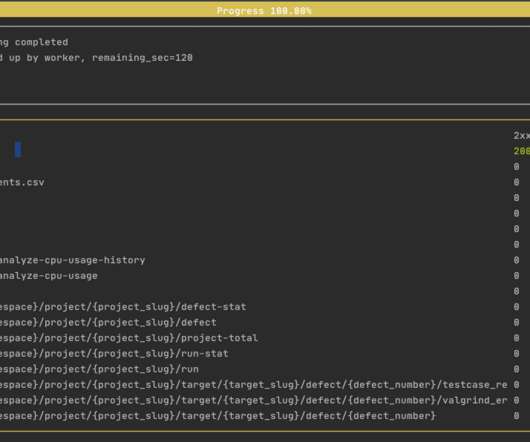
ForAllSecure
OCTOBER 25, 2022
Tells the fuzzer to base its testing on the OpenAPI 3 specification of the petstore demo API, which is hosted on our site for demo purposes. --url Tells the fuzzer, which is running locally on your computer, to address its tests to the petstore demo API on our network. Get Free Request A Demo. url "[link].
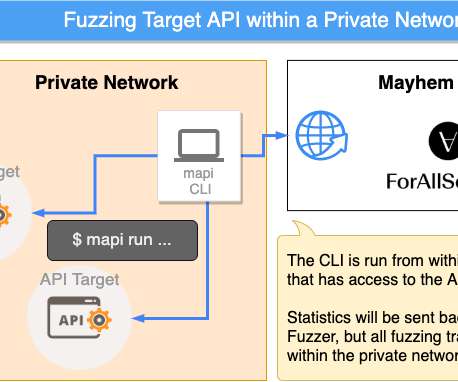
ForAllSecure
SEPTEMBER 30, 2022
You've seen what Mayhem for API can do in a demo. Because the requests come directly from the mapi CLI tool running locally on your computer, this will work for APIs that are: Behind a corporate firewall. Get Free Request A Demo. Now it's time to fuzz your own! x collection in place of an OpenAPI spec, and work with that.
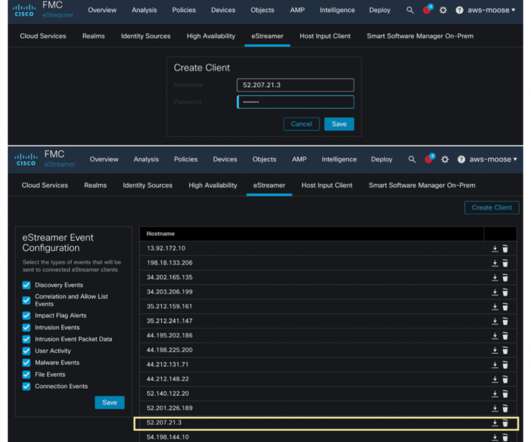
Cisco Security
NOVEMBER 29, 2022
The eNcore client can request event and host profile data from a Management Center, and intrusion event data only from a managed device. The eNcore client can request event and host profile data from a Management Center, and intrusion event data only from a managed device. Cisco Secure and AWS Security Lake. Cisco Secure Firewall.
Malwarebytes
JANUARY 19, 2022
It also houses a database of consent history for app requests. Here’s a link to the demo video of how it now works in Monterey. If you have been forgoing updating your Mac, this article might make you think twice. The Microsoft team is said to have reported Powerdir to Apple in mid-July 2021, and Apple patched it 6 months after.
Security Affairs
MARCH 14, 2021
Below the description of the demo published on a site set up by Google to host the PoC code. “This demo is split into three parts: Calibrating the timer to observe side effects of the CPU’s speculative execution. . Google released proof-of-concept code for conducting a Spectre attack against its Chrome browser on GitHub.

ForAllSecure
OCTOBER 12, 2022
Ultimately, if your Postman request works, we want Mayhem to just work. Try running the demo yourself against the Pet Store API: mapi run. --url postman-integration-demo 30. Some of the endpoints are crashing when the request is mutated, and are returning 500 errors. You will need to create an API key in postman.

Security Boulevard
MARCH 17, 2021
<a href='/blog?tag=Cybersecurity'>Cybersecurity</a> tag=Cybersecurity'>Cybersecurity</a> <a href='/blog?tag=Data tag=Data Loss Prevention'>Data Loss Prevention</a> <a href='/blog?tag=IT DLP can be either network or endpoint-based and plays an important role in keeping data secure.

Security Boulevard
MARCH 19, 2021
<a href='/blog?tag=Inbound tag=Inbound Threats'>Inbound Threats</a> <a href='/blog?tag=File tag=File Transfers'>File Transfers</a> <a href='/blog?tag=Email This caused many issues. Luckier people had a home office or spare room to work from, while others had to make do with the kitchen table or the sofa.

Spinone
JUNE 2, 2020
Request a demo and get them answered! Request a Demo The post SpinOne Application Auditing Capabilities first appeared on SpinOne. Are all SaaS applications for G Suite safe? Unfortunately, no. Some apps may be fake and some have potential security gaps or other risks. And we are here to help you.

Krebs on Security
JUNE 19, 2018
At issue are companies known in the wireless industry as “location aggregators,” entities that manage requests for real-time customer location data for a variety of purposes, such as roadside assistance and emergency response. LocationSmart disabled its demo page shortly after that story. mobile networks. mobile networks.

eSecurity Planet
FEBRUARY 26, 2021
This information is then analyzed to determine if the client request is from a human user or a bot. . This information is then analyzed to determine if the client request is from a human user or a bot. . You can request a demo or contact the company for a quote. Kasada plans. Kasada plans. Kasada case studies.

Security Affairs
MAY 27, 2021
A demo app to access this register is available here.” one side writes 1x to send data, the other side writes 00 to request the next bit). . one side writes 1x to send data, the other side writes 00 to request the next bit). This is a per-cluster register that can be simultaneously accessed by all cores in a cluster.
Security Affairs
FEBRUARY 19, 2020
When doing so, it does not verify that a request is coming from an administrative user. 2020 – Over 200K WordPress sites are exposed to attacks due to a high severity cross-site request forgery (CSRF) bug in Code Snippets plugin. According to WordFence, the ThemeREX Addons zero-day is currently installed on at least 44,000 websites.

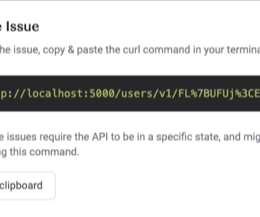
Pentester Academy
APRIL 20, 2023
This can be confirmed by sending a curl request to the available candidate ports. Step 3: Send a request to the Java application on port 8080. Request contents for that link: Command: curl [link] The response says forbidden. Introduction What is Spring Security? It is the de-facto standard for securing Spring-based applications.

eSecurity Planet
FEBRUARY 26, 2021
This information is then analyzed to determine if the client request is from a human user or a bot. . This information is then analyzed to determine if the client request is from a human user or a bot. . You can request a demo or contact the company for a quote. Kasada plans. Kasada plans. Kasada case studies.
ForAllSecure
SEPTEMBER 8, 2022
Security - With a growing list of Security Checkers , Mayhem for API can discover issues such as Server Side Request Forgery (SSRF) and SQL Injection. Get Free Request A Demo. With the guidance of an API specification , Mayhem for API provides accurate and informative test coverage tailored to any REST API. How does it work?

The Last Watchdog
AUGUST 31, 2023
A demo is available upon request. San Francisco, Calif., 30, 2023 — Every year over 340m workers suffer a workplace injury: slips and falls, strains and sprains, vehicle collisions and crashes. The future of work is not just about doing more, but doing it safer in an environment fit for purpose”.

Pentester Academy
MARCH 10, 2023
To learn more about how INE Business Solutions can solve your business’s IT training challenges, request a free demo of our platform. In this day and age, cyber attacks are a risk for everyone and anyone. We’ve all seen headlines in the news about cyber attacks. You’ve likely experienced a breach of your own.

Security Boulevard
FEBRUARY 7, 2022
Request a personalized demo. Winners again? For the second year in a row, Cybersecurity Insiders™ has recognized Salt Security and our Salt Security API Protection Platform with Cybersecurity Excellence Awards. This year, we won for Best Cybersecurity Company and Best Cybersecurity Product in API Security. undefined.
Security Affairs
MAY 1, 2020
The developers behind the Ninja Forms WordPress plugin have addressed a Cross-Site Request Forgery (CSRF) vulnerability that could lead to Stored Cross-Site Scripting (Stored XSS) attacks. Experts noticed that two of these functions failed to check nonces, this means that they don’t verify the identity of the user that sent a request.

Security Affairs
MARCH 9, 2019
The researchers discovered that the APIs for both applications failed to authenticate requests allowing attackers to take over customers’ accounts due to insecure direct object references (IDORs) issues. Both products allow anyone to create a test/demo account. ” reads the report published by Pen Test Partners.

CyberSecurity Insiders
DECEMBER 1, 2021
Introduction. Recently I received a call on my personal cellphone. The call started out as many do; with a slight pause after I answered. Initially I assumed this pause was caused by whatever auto-dialer software the spammer was using to initiate the call before their text-to-speech software starts talking about my car’s extended warranty.
Security Boulevard
DECEMBER 9, 2021
If you want to follow along with the demo, the vulnerable project Tarpit Java is here. Remote code execution vulnerabilities are also called RCE. They are a class of vulnerabilities that happen when attackers can execute their code on your machine. For instance, let’s say that the application creates new files based on user input.

Security Boulevard
MARCH 24, 2022
When allegations appeared on Twitter on March 22 that cloud identity services provider Okta had been breached, the tech world held its breath. CEO Todd McKinnon tweeted, “In late January 2022, Okta detected an attempt to compromise the account of a third-party customer support engineer working for one of our subprocessors.
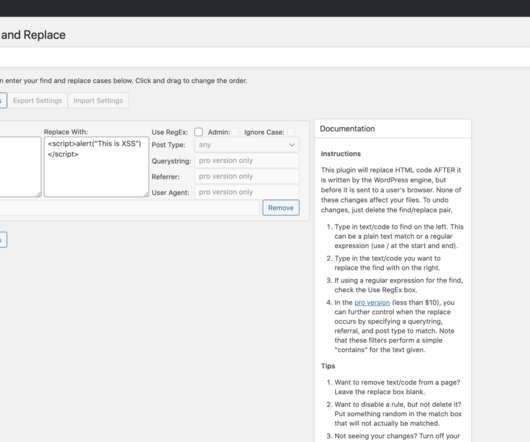
Security Affairs
APRIL 28, 2020
The vulnerability was discovered by Wordfence researchers, it is a Cross-Site Request Forgery flaw that could lead to Stored Cross-Site Scripting (Stored XSS) attacks. A bug in the Real-Time Find and Replace WordPress plugin could allow hackers to hackers to create rogue admin accounts on over 100,000 sites. ” continues the report.
Security Affairs
DECEMBER 8, 2020
The flaw could also open to phishing attacks by redirecting the victims to attackers’ site or requesting SSO credential input. Security expert disclosed technical details about a wormable, cross-platform flaw in Microsoft Teams that could allow stealth attacks. ” reads the advisory published by Vegeris. Pierluigi Paganini.

Spinone
MAY 13, 2020
Request a Demo Here you can read a detailed Domain Audit guide. SpinOne gives you more visibility and control over everything concerning your G Suite data. With SpinOne’s G Suite Domain Audit functionality, you can monitor various domain activities such as installed apps and data transfer. Otherwise, corporate data may be lost.

Security Boulevard
OCTOBER 7, 2021
User input locations such as HTTP request parameters, HTTP headers, HTTP request paths, database entries, file reads, and file uploads provide the entry points for attackers to exploit the application’s vulnerabilities. Getting started with a source code review using ShiftLeft CORE. Photo by Roman Synkevych on Unsplash.
Security Affairs
MARCH 11, 2020
“Access control and cross-site request forgery (CSRF) protection aside, the core of the problem was within the functionality of the code itself.” 2020 – Over 200K WordPress sites are exposed to attacks due to a high severity cross-site request forgery (CSRF) bug in Code Snippets plugin. php file. continues the analysis.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content