CrowdStrike Class Action Lawsuit for Massive Software Outage
eSecurity Planet
AUGUST 8, 2024
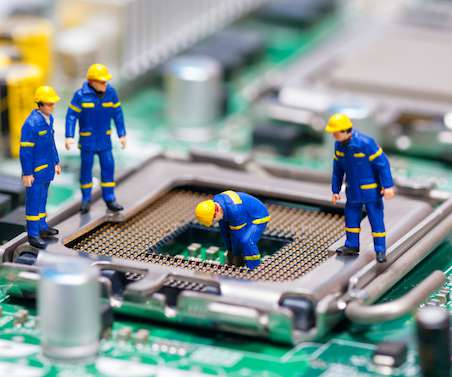
A catastrophic software update unleashed a domino effect of disruptions, paralyzing millions of computers across the globe. A class-action lawsuit has been filed against CrowdStrike, alleging that the company misled investors about the robustness of its software testing procedures.
















































Let's personalize your content