GUEST ESSAY: The promise and pitfalls of using augmented reality– ‘AR’ — in cybersecurity
The Last Watchdog
NOVEMBER 11, 2024
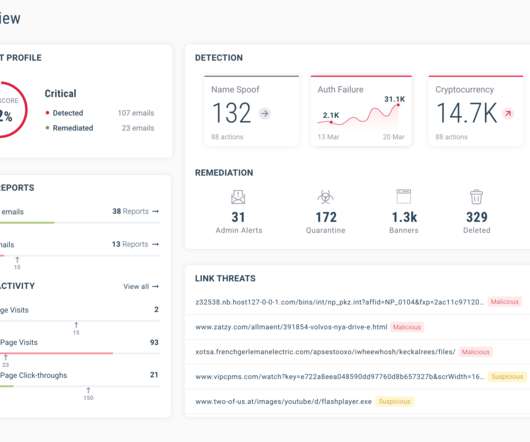
This is primarily because AR is still relatively new and a rapidly evolving technology, which ultimately means that it is bound to bring about unprecedented opportunities, challenges, and even risks to cybersecurity. Waqas Apart from the training aspect, AR technology can also be used to enhance threat detection in real-time.











































Let's personalize your content