GDPR Solutions: Cybersecurity Vendors Offer New Compliance Products
eSecurity Planet
JUNE 1, 2018
GDPR is here, and cybersecurity vendors are responding with privacy and security compliance solutions.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 solutions compliance gdpr
solutions compliance gdpr 
eSecurity Planet
JUNE 1, 2018
GDPR is here, and cybersecurity vendors are responding with privacy and security compliance solutions.

eSecurity Planet
DECEMBER 22, 2021
But in order for businesses to maintain compliance with major privacy laws , they have to have security measures in place before an attack. The regulations from GDPR, PIPL, and CCPA are especially prevalent to MSPs and software vendors because they get access to data from so many organizations, but all businesses need to comply with them.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
AUGUST 9, 2022
Regulatory compliance and data privacy issues have long been an IT security nightmare. And since the EU’s General Data Protection Regulation (GDPR) took effect May 25, 2018, IT compliance issues have been at the forefront of corporate concerns. GDPR-style data privacy laws came to the U.S.

The Last Watchdog
AUGUST 7, 2023
Information Security Enforcer (ISE) GhangorCloud’s ISE is a 4th Generation Data Leak and Exfiltration Prevention (DLEP) solution that enables robust security and compliance enforcement against both malicious and inadvertent disclosure and/or theft of sensitive and confidential information. San Jose, Calif.,

BH Consulting
AUGUST 31, 2022
Since the EU General Data Protection Regulation came into force in May 2018, there hasn’t yet been a way to prove compliance with it. Luxembourg’s GDPR-CARPA is the first officially recognised certification scheme to be adopted under the regulation. So why has it taken this long for a GDPR certification scheme to launch?

Thales Cloud Protection & Licensing
AUGUST 30, 2023
The bright side of data privacy compliance: 5 value-driven opportunities for retailers madhav Thu, 08/31/2023 - 05:20 Failing to keep up with data privacy legislations, such as General Data Protection Regulation (GDPR) or the California Consumer Privacy Act (CCPA) can harm a brand’s bottom-line and public reputation. Let’s unpack this.

Security Boulevard
FEBRUARY 18, 2024
Organisations should leverage identity and access management (IAM) solutions that provide multi-factor authentication (MFA), role-based access control (RBAC), and the principle of least privilege, to minimize the risk of compromise. Clearly, the cloud is not the panacea some thought it would be.

CyberSecurity Insiders
MAY 12, 2023
Streamlining the audit process is not the only benefit compliance automation. From higher productivity to stronger security posture, automation improves your compliance program. Learn more about the benefits of compliance automation and then schedule a demo to see how you can streamline your audit processes.

Thales Cloud Protection & Licensing
NOVEMBER 6, 2023
Many countries and regions have implemented strict data protection laws, such as the European Union's General Data Protection Regulation (GDPR), requiring organizations to adhere to specific data protection standards. The Monsido tool operates entirely on the Google Cloud Platform.
Thales Cloud Protection & Licensing
JUNE 15, 2023
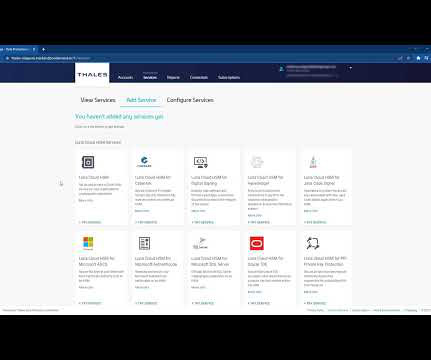
Key Management as a Service (KMaaS) allows companies to manage encryption keys more effectively through a cloud-based solution instead of running the service on physical, on-premises hardware. A third-party service provider manages a KMaaS solution to alleviate the burden of cryptographic key management.

CyberSecurity Insiders
MAY 17, 2023
Cybersecurity compliance refers to the process of ensuring that an organization’s cybersecurity measures meet relevant regulations and industry standards. Importance of cybersecurity compliance Compliance with relevant cybersecurity regulations and standards is essential for several reasons.

Security Boulevard
FEBRUARY 27, 2024
FireMon: Built for Compliance Reporting Real-Time Compliance Management at Scale Advanced Asset Discovery In Conclusion Get a Demo In today’s digital age, cybercrime has become big business and no industry is immune. Additional fines can be imposed due to data breaches, even if the organization is in compliance. What's at Stake?

Centraleyes
JANUARY 21, 2024
With the introduction of NIS2 , the European Union has moved beyond the GDPR’s focus on data protection measures to strengthen the entirety of the digital infrastructure that underpins critical sectors. Conduct a gap assessment to evaluate current compliance with NIS2 requirements.

Security Boulevard
FEBRUARY 14, 2024
How is FireMon Better Book a Demo Healthcare companies have a responsibility to protect sensitive patient data and ensure compliance with regulations like HIPAA. FireMon, a leader in network security policy management, offers solutions tailored to the needs of healthcare companies. Why Act Now? Why Choose FireMon?

IT Security Guru
MARCH 27, 2024
Prior to DORA, financial institutions primarily relied on compliance-driven capital allocation to prove they were mitigating operational risks, but this alone did not prove a suitable level of operational resilience. The post Tackling DORA Compliance With a Focus on PAM first appeared on IT Security Guru.
Centraleyes
APRIL 8, 2024
In light of these statistics, organizations are developing new data privacy and governance policies to deal with security breaches and regulatory compliance requirements. Reducing Company Risk: By locating, identifying, classifying, minimizing , and securing sensitive data, firms can r educe the risk of security, privacy, and compliance.

CSO Magazine
MAY 2, 2023
Data security authorization vendor Veza has announced a new solution for access security and governance across SaaS applications including Salesforce, GitHub, and Slack.

The Last Watchdog
JULY 12, 2023
While SaaS has revolutionized the way organizations operate by providing access to cutting-edge technologies and boosting cost-efficiency, they often lack a robust data backup/recovery solution. Without an effective data protection strategy, businesses are vulnerable to data loss, breaches, and regulatory non-compliance.
CyberSecurity Insiders
FEBRUARY 9, 2021
These categories of sensitive information are protected by regulations such as the GDPR, CCPA, HIPAA, and PCI DSS. The following checklist intends to provide a general framework for your DLP strategy and help you choose the right DLP solution for your company. Identify & assess compliance obligations. Set up DLP policies.

The Last Watchdog
OCTOBER 19, 2020
They are responding to a trend of companies moving to meet rising compliance requirements, such as PCI-DSS and GDPR. All of this activity has put a strain on how companies buy and sell cybersecurity solutions. Traditional channels for choosing the right security solutions are proving to be increasingly ineffective.

Thales Cloud Protection & Licensing
MAY 31, 2022
More than 120 governments have already implemented data privacy regulation to that very purpose, as stated in Recital 1 of the GDPR in the EU (General Data Protection Regulation). Data Protection Officers expressed the difficulties they have to accomplish their mission: to advise on and monitor compliance (as defined in GDPR Article 39).

Thales Cloud Protection & Licensing
JULY 28, 2021
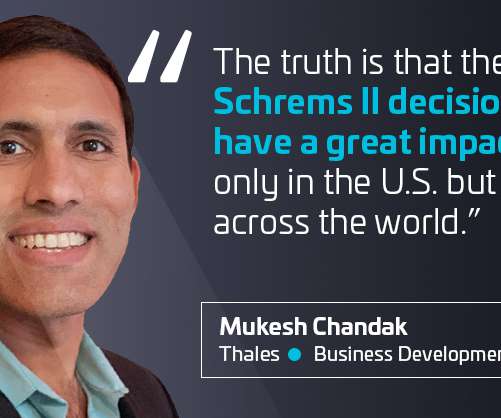
Why agnostic access security is critical for compliance in the post Schrems II landscape. In this regard, a cloud agnostic, flexible, and controlled access security solution may come in very handy for organizations. Instead, businesses should implement data protection solutions that can adequately protect global commerce.

Thales Cloud Protection & Licensing
APRIL 14, 2021
Just when you thought that you had a working solution compliant with General Data Protection Regulation (GDPR), for sharing data between EU and non-EU countries as part of your regular business communications, the Schrems II ruling appears out of nowhere and moves the goalposts! Thu, 04/15/2021 - 05:17.

Thales Cloud Protection & Licensing
DECEMBER 22, 2020
Traditionally, privacy has taken the form of a policy document created, housed, and referenced by the offices of general counsel and compliance at most organizations. Data privacy is not a check-the-box compliance or security item. The problem is not limited to the requirements of GDPR. Multinationals Face Unique Challenges.

The Last Watchdog
JANUARY 28, 2024
Europe’s General Data Protection Regulation (GDPR) and California’s Consumer Privacy Act (CCPA,) for instance, are two significant pieces of legislation aimed at protecting consumer privacy in the digital age. In addition to developing and getting in position to supply the technology, Boyle says.

Cisco Security
NOVEMBER 2, 2021
With the 2018 General Data Protection Regulation (GDPR), Europe marked a big step in strengthening individuals’ privacy rights. While the GDPR aims to bring consistency to the data protection landscape, incorporating well-recognized privacy principles like transparency, fairness, and accountability – operationalizing it has been a challenge.

The Last Watchdog
APRIL 3, 2023
In addition to real-time protection, effective VM can also help with compliance at a time when data security rules are increasing in regulatory policies like NIST, PCI, HIPAA and GDPR. With traditional VM, achieving compliance is a struggle. Cyber attacks can also invite lawsuits and can even be fatal.

Thales Cloud Protection & Licensing
JUNE 24, 2021
How FIDO 2 authentication can help achieve regulatory compliance. As such, FIDO2 can become an enabler for regulatory compliance. In the following paragraphs we will examine use cases where FIDO2 simplifies compliance with privacy and security regulations, namely GDPR, CCPA and PSD2. Compliance with GDPR and CCPA.

Security Affairs
SEPTEMBER 26, 2023
Compliance and Regulatory Challenges Organizations today must adhere to many data privacy and security regulations. The consequences of non-compliance can be severe, including hefty fines and reputational damage. Data lineage is not just a fancy visualization tool; it’s a critical solution to many data management challenges.

Centraleyes
NOVEMBER 23, 2023
At the heart of every organization’s pursuit of compliance lies the critical need to meet regulatory expectations and consistently maintain that state of compliance. Achieving compliance is like reaching a summit, but staying there requires ongoing effort and vigilance.

Thales Cloud Protection & Licensing
AUGUST 21, 2018
The enactment of the European Union’s General Data Protection Regulation (GDPR) is a significant milestone for virtually every international business. The following overview touches on some of the most critical elements that are required for GDPR compliance. Fine-Grained Access Control. Data Autonomy and Sovereignty.

Thales Cloud Protection & Licensing
DECEMBER 7, 2022
As security breaches continue with alarming regularity and compliance mandates become more pervasive, companies must discover and protect sensitive data across on premises, hybrid, and multi-cloud environments. Hosting resources in an on premises datacenter is sometimes mandatory because of technical, regulatory, or compliance requirements.
Thales Cloud Protection & Licensing
MARCH 1, 2021
companies rely to conduct trans-Atlantic trade in compliance with EU data protection rules. However, the level of the impact depends on the geography and the vertical of each organization and the strategic privacy planning they have done for sustaining compliance with GDPR. Compliance. Data security. Government.
Thales Cloud Protection & Licensing
FEBRUARY 2, 2022
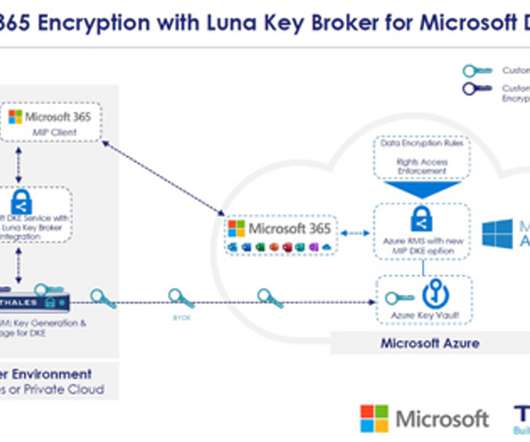
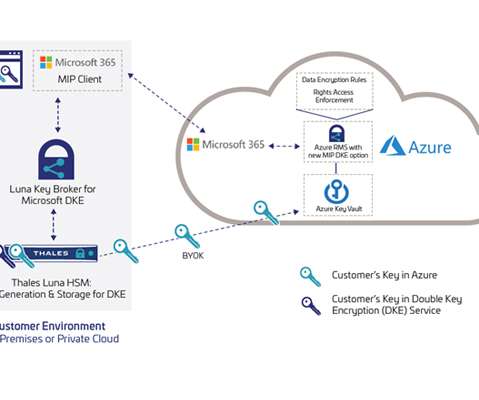
How Microsoft and Thales Offer Enhanced Security and Compliance for Microsoft Office 365. Our discussion covered topics like customer concerns and expectations, data sensitivity, regulatory compliance, and fully integrated security through DKE and Luna Key Broker. CSP foreign government compliance obligations.

eSecurity Planet
JANUARY 18, 2024
It’s a scalable and cost-effective storage solution for businesses offered through a subscription service. When assessing the overall security of cloud storage and choosing a solution tailored to your business, it helps to determine its features, potential risks, security measures, and other considerations.

Thales Cloud Protection & Licensing
MARCH 1, 2018
Around the world, enterprises are anxious about May 25, 2018, the day enforcement begins for the European Union’s General Data Protection Regulation (GDPR). And, with potential fines of up to four percent of global revenues or 20 million EUR (whichever is higher), the GDPR has the attention of CEOs and Boards of Directors.

eSecurity Planet
FEBRUARY 14, 2023
It was also a drag on the sales cycle, and then there was the need for maintaining compliance. The vision was to automate security and compliance across 14 frameworks, including SOC 2, ISO 27001, HIPAA and GDPR. GRC Market Defies Downturn There are some powerful drivers for the compliance and security automation market.

Centraleyes
MARCH 3, 2024
Compliance Risk Assessments For a Dynamic Regulatory Terrain Crafting an effective compliance program is no one-size-fits-all endeavor; it involves tailoring a comprehensive strategy that addresses your company’s unique needs and confronts specific challenges head-on. Compliance Risk Assessment: Who, What, Where, When, and How?
Thales Cloud Protection & Licensing
APRIL 1, 2021
Today’s remote working environment relies heavily on the collaborative sharing of information, challenging organizations to maintain the security of confidential data and regulatory compliance while driving employee productivity. The DKE solution uses two keys to protect highly-sensitive data.

Security Affairs
OCTOBER 20, 2020
According to a report by the International Association of Privacy Professionals, 33% of respondents have considered revamping their technology solutions around data privacy. Data privacy regulations such as the CCPA and GDPR require organizations to take responsibility for their consumers’ data.

CyberSecurity Insiders
OCTOBER 19, 2022
Many healthcare organizations are using their IAM systems to address their ongoing complex compliance requirements, combat persistent cybersecurity threats, and securely share medical records with patients and within the healthcare network. Consumer Expectations.

Centraleyes
FEBRUARY 5, 2024
Do you find yourself tempted to postpone your compliance duties? The sighs and eye-rolls that often accompany the mention of compliance reveal a common sentiment: it’s viewed as an unwanted chore, a necessary evil that demands time, resources, and attention. What is Cyber Security Compliance?

eSecurity Planet
NOVEMBER 20, 2019
GDPR is the latest compliance and data privacy reg to affect IT security. We list many more – along with legal issues and GRC solutions to consider.

Thales Cloud Protection & Licensing
MARCH 1, 2023
When Europe published GDPR, a similar issue emerged since sites operating in Europe were required to abide by its regulations, even if they weren't based in Europe. The Cyber Resilience Act mandates that the most critical products have their compliance with EU security standards evaluated by a third party.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content