How Data Changes the Cyber-Insurance Market Outlook
Dark Reading
OCTOBER 16, 2023
By using data to drive policy underwriting, cyber-insurance companies can offer coverage without a price tag that drives customers away.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag policy
tag policy 
Dark Reading
OCTOBER 16, 2023
By using data to drive policy underwriting, cyber-insurance companies can offer coverage without a price tag that drives customers away.

Bleeping Computer
MAY 16, 2023
Apple's App Store team prevented more than $2 billion in transactions tagged as potentially fraudulent and blocked almost 1.7 million app submissions for privacy, security, and content policy violations in 2022. [.]
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
SEPTEMBER 8, 2023
The attacks that took place in the past weeks were detected by researchers at Google’s Threat Analysis Group (TAG). “Recently, TAG became aware of a new campaign likely from the same actors based on similarities with the previous campaign. ” reads the advisory published by Google TAG.

eSecurity Planet
JUNE 1, 2023
Dependent Email Authentication Standards DMARC depends upon the successful establishment of the Sender Policy Framework (SPF) and the DomainKeys Identified Mail (DKIM) authentication standards. It is possible to define a DMARC policy in a DNS record without first setting up SPF and DKIM, but it won’t be able to do anything.

The Hacker News
APRIL 5, 2023
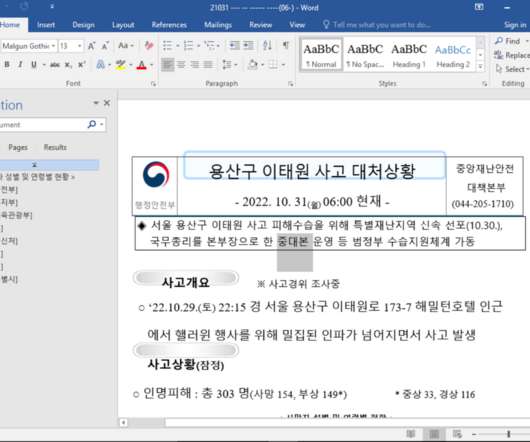
A North Korean government-backed threat actor has been linked to attacks targeting government and military personnel, think tanks, policy makers, academics, and researchers in South Korea and the U.S.
Security Affairs
DECEMBER 8, 2022
Our policy is to quickly report vulnerabilities to vendors, and within a few hours of discovering this 0-day, we reported it to Microsoft and patches were released to protect users from these attacks.” ” reads the post published by TAG. Google TAG shared indicators of compromise (IOCs) for this campaign.

Security Affairs
FEBRUARY 5, 2024
Last week Ivanti warned of two new high-severity vulnerabilities in its Connect Secure and Policy Secure solutions respectively tracked as CVE-2024-21888 (CVSS score: 8.8) x), Policy Secure (9.x, and CVE-2024-21893 (CVSS score: 8.2). x) and Neurons for ZTA.
Security Affairs
APRIL 6, 2023
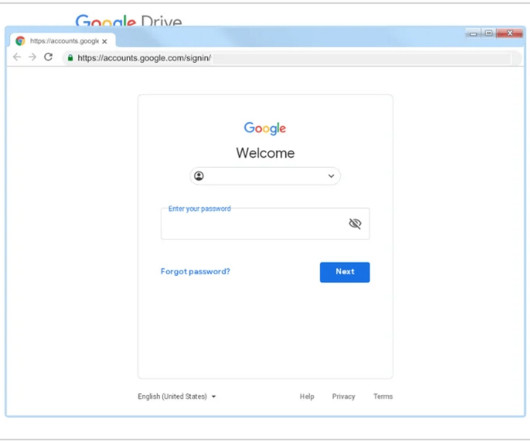
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. Google experts are tracking ARCHIPELAGO since 2012 and have observed the group targeting individuals with expertise in North Korea policy issues. ” reads the analysis published by Google TAG.
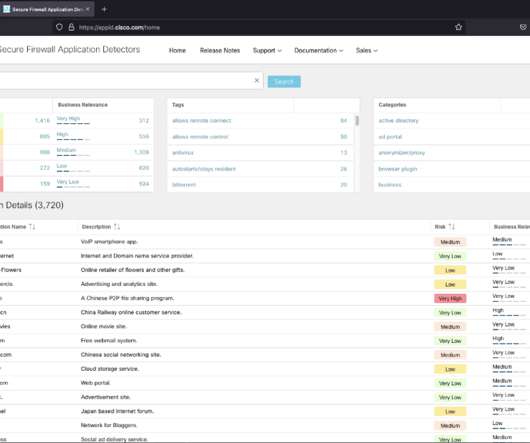
Cisco Security
SEPTEMBER 23, 2021
Enforce quality-of-service (QoS) policies and service guarantees for latency-sensitive applications (such as voice over IP [VoIP] and interactive gaming). Implement fair-use policies and manage network congestion by optimizing application-level traffic. An application can have zero, one, or more tags.

Tech Republic Security
DECEMBER 6, 2022
Eliminate outages and minimize data loss for Tier 1 VMware workloads with built-in Continuous Data Protection (CDP) and get instant restores to the most recent state or point in time, plus: Easily install the filter driver on a vSphere cluster Use vSphere tags for a policy-based approach to securing workloads Learn how CDP protects Tier‑1.

Tech Republic Security
DECEMBER 6, 2022
Eliminate outages and minimize data loss for Tier 1 VMware workloads with built-in Continuous Data Protection (CDP) and get instant restores to the most recent state or point in time, plus: Easily install the filter driver on a vSphere cluster Use vSphere tags for a policy-based approach to securing workloads Learn how CDP protects Tier‑1.

Security Affairs
NOVEMBER 12, 2021
Google TAG researchers discovered that threat actors leveraged a zero-day vulnerability in macOS in a watering hole campaign aimed at delivering malware to users in Hong Kong. “To protect our users, TAG routinely hunts for 0-day vulnerabilities exploited in-the-wild. ” reads the analysis published by Google.

Security Boulevard
MARCH 17, 2021
tag=Cybersecurity'>Cybersecurity</a> <a href='/blog?tag=Data tag=Data Loss Prevention'>Data Loss Prevention</a> <a href='/blog?tag=IT tag=IT Security'>IT Security</a> Protecting customer data from loss and leakage has become a top priority for enterprises over the past decade.

NetSpi Technical
MARCH 11, 2024
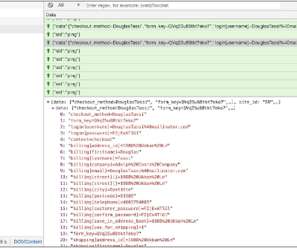
This property tag contained the COM GUID that we have assigned in the configuration file, which ultimately defines what COM CLSID the form was eventually registered as. Again, SensePost provides an overview of these property tags and their importance so we will refrain from re-stating the same here. What makes that determination?”

eSecurity Planet
MARCH 15, 2021
Microsegmentation is about identifying your organization’s most valuable network segments, establishing strict communication policies, and becoming the master of your network flows. This agent-based method translates to real-time protection of your policies. Tag Your Workloads. Outsource Endpoint Protection.
Approachable Cyber Threats
JULY 19, 2022
RFID uses electromagnetic fields in the form of radio waves to establish communication links between an RFID tag or transmitter and an RFID reader or receiver. Pieces of information are transmitted through the link that the reader uses to establish authenticity of the tag or transmitter and authorize access. Is RFID secure?

Security Affairs
AUGUST 7, 2020
Google published its second Threat Analysis Group (TAG) report which reveals the company has taken down ten coordinated operations in Q2 2020. Google has published its second Threat Analysis Group (TAG) report , a bulletin that includes coordinated influence operation campaigns tracked in Q2 of 2020. response to COVID-19.
CyberSecurity Insiders
FEBRUARY 9, 2021
It should cover both structured and unstructured data, tagging it based on its level of sensitivity and making it easier to find, track, and safeguard. Applying persistent classification tags to data is essential and allows your organizations to track their use. Set up DLP policies. Identify & assess compliance obligations.

Security Boulevard
AUGUST 30, 2021
tag=Endpoint Protection'>Endpoint Protection</a> <a href='/blog?tag=Data tag=Data Loss Prevention'>Data Loss Prevention</a> <a href='/blog?tag=File tag=File Transfers'>File Transfers</a> <a href='/blog?tag=Advanced <a href='/blog?tag=Endpoint Additional Resources. Featured: .

CyberSecurity Insiders
APRIL 20, 2023
Bank of America has expressed its concerns over Lloyd’s recent policy decision to exclude cyber insurance coverage for large corporations hit by cyber attacks funded by adversary states. As of now, it offers a standard policy under which a company needs to follow all security procedures to be covered under the attack.
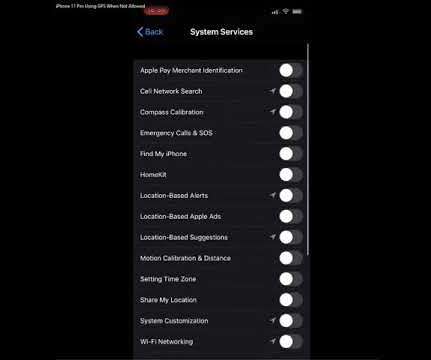
Krebs on Security
DECEMBER 4, 2019
Apple says this is by design, but that response seems at odds with the company’s own privacy policy. ” The policy explains users can disable all location services entirely with one swipe (by navigating to Settings > Privacy > Location Services, then switching “Location Services” to “off”).
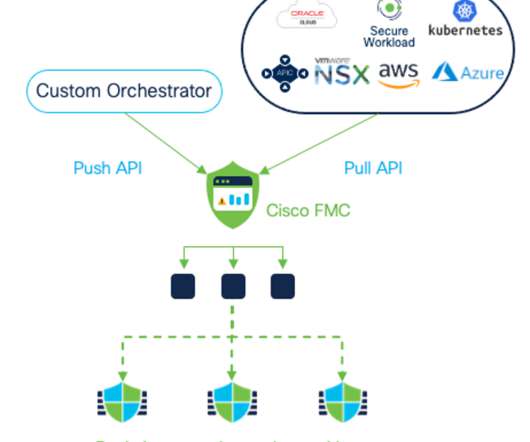
Cisco Security
JULY 26, 2021
Workloads spin up and down faster than traditional security policy change management can accommodate, straining NetOps and SecOps teams with the rapid pace of change and continuous adjustments in a constantly changing environment. Policy enforcement as dynamic as your environment. Secure Firewall Threat Defense 7.0

Troy Hunt
FEBRUARY 1, 2018
I've long been a proponent of Content Security Policies (CSPs). However, you can add a CSP via meta tag and indeed that's what I originally did with the upgrade-insecure-requests implementation I mentioned earlier when I fixed the Disqus issue. There's no faster way to generate a baseline policy than this!

The Last Watchdog
AUGUST 8, 2023
With support for Microsoft CA and AWS Private CA, DigiCert Trust Lifecycle Manager enables discovery, issuance, automation and revocation, including the ability to tag, filter and apply policy to imported and discovered third-party digital certificates.

SecureWorld News
JANUARY 26, 2021
Google's Threat Analysis Group (TAG) has been working for several months to try to identify who is behind an ongoing campaign targeting security researchers, specifically those who work on vulnerability research and development at a variety of organizations. Google's TAG team discovery: cyberattack motive.
Cisco Security
JUNE 8, 2021
In Part One of the Cisco TrustSec Policy Analytics blog series, Samuel Brown addressed some of the challenges related to designing group-based security policies and introduced one of the new feature sets of Cisco Secure Network Analytics – TrustSec Analytics reports. I’d like to do segmentation, but I don’t want to get fired.

Cisco Security
MAY 17, 2021
Comprehensive visibility and awareness of changes in your application communications drive automated firewall policy recommendations.Unlike other firewall providers, only Cisco has integrated firewall and microsegmentation capability. enabling robust policies in environments where fixed IP addresses don’t exist. Threat Defense 7.0

CyberSecurity Insiders
SEPTEMBER 23, 2021
The email blunder occurred because of an irresponsible behavior of an employee serving UK’s Afghan Relocations and Assistance Policy(ARAP) team. As a second data breach occurred at the end of last week, leaking details of Afghan nationals eligible to relocate to UK.
Security Affairs
NOVEMBER 15, 2020
Once executed, a malicious JavaScript file is requested from the a C2 server (at https[:]//tags-manager[.]com/gtags/script2 The distinctive aspect of this attack is the use of WebSockets, instead of HTML tags or XHR requests, to extract the information from the compromised site that makes this technique more stealth.
Security Affairs
JULY 14, 2021
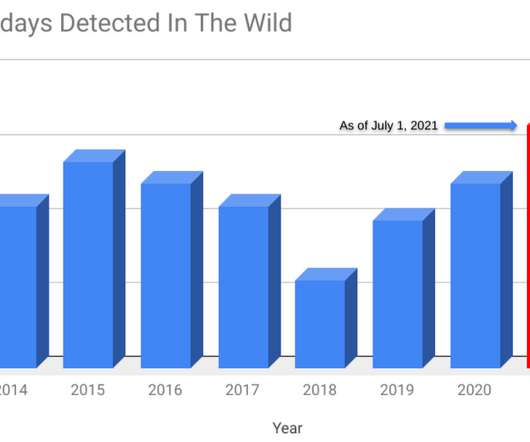
Security researchers from Google Threat Analysis Group (TAG) and Google Project Zero revealed that four zero-day vulnerabilities have been exploited in the wild earlier this year. As is our policy, after discovering these 0-days, we quickly reported to the vendor and patches were released to users to protect them from these attacks.”

Malwarebytes
SEPTEMBER 22, 2022
The HTTP Feature-Policy header provides a mechanism to allow and deny the use of browser features in its own frame, and in content within any iframe elements in the document. CVE-2022-40956 : (Low) Content-Security-Policy (CSP) base-uri bypass. CVE-2022-40960 : (High) Data-race when parsing non-UTF-8 URLs in threads. Thunderbird.

IT Security Guru
MAY 24, 2021
They need automation when they want it, so that action is taken automatically based on the security risk policies they have put in place. Simple policies like “No databases should run on webservers” can become a complex challenge to implement. These changes need to be monitored. Adding the Security Focus to IT Asset Inventory.

Security Boulevard
AUGUST 24, 2021
tag='></a> <a href='/blog?tag='></a> tag='></a> <a href='/blog?tag='></a> tag='></a> Protecting customer data from loss and leakage has become a top priority for enterprises over the past decade. <a href='/blog?tag='></a> Request a Demo.
SiteLock
AUGUST 27, 2021
First, packet filtering is the action of inspecting the traffic traversing the firewall’s network to determine if the traffic is meeting the firewall’s security policy. Traffic conforming to the firewall’s security policy is allowed to proceed, while traffic not meeting the policy (e.g. a malicious attempt) is blocked.

Cisco Security
JUNE 28, 2021
This detailed list of industrial devices is shared in real-time with Cisco Identity Services Engine (ISE) where security policies are created. Once IT and OT have defined the industrial zones or production cells they want to secure, IT will create Security Group Tags (SGT) in ISE to specify which communications are allowed between zones.
Centraleyes
APRIL 16, 2024
Beyond being a set of security protocols, data loss prevention policies are a strategic approach that involves identifying, monitoring, and protecting sensitive data throughout its lifecycle. This involves defining clear policies, procedures, and data ownership throughout its lifecycle.

Malwarebytes
JULY 28, 2023
Reportedly , Maddie Stone from the Google Threat Analysis Group (TAG)—which first reported the vulnerability—confirmed that this issue was used by an Advanced Persistent Threat (APT) group in targeted attacks. 509 certificate chains that include policy constraints. The OpenSSL package has been upgraded.

Malwarebytes
APRIL 3, 2023
By exploiting this, the attacker can bypass the browser’s same origin policy and is able to steal private information from a victim associated with the website. As a possible consequence, a visitor of that website will execute that code in his browser and it will be treated (read: trusted) as if it originated from the site they visited.

eSecurity Planet
MARCH 21, 2022
“Our approach is that the visibility and the policy actually surrounds the data and define it for a particular type of data itself. ” Skyhigh’s approach is to determine what data is important and sensitive, how it’s being used, and who has access to it, and then base security policies on that.

Malwarebytes
JANUARY 16, 2023
The malicious code injected was inside a Google Tag Manager (GTM) snippet encoded as Base64. Malwarebytes’ Director of Threat Intelligence Jérôme Segura commented: The attack on LCBO's online portal follows a trend we've seen before of injecting malicious code disguised as legitimate snippets such as Google Tag Manager.

Security Boulevard
AUGUST 4, 2021
When the Scorecard project was announced in November 2020, OpenSSF explained that some fundamental evaluation metrics included: well-defined security policy. Security Policy. The root directory should have a security policy file named “SECURITY.md” (not case sensitive). Signed Tags. code review process.
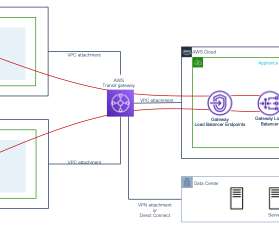
Cisco Security
NOVEMBER 29, 2021
Customers also benefit from support for dynamic policies for AWS tags, plus improved threat detection, simplified customization, and enhanced performance of our latest, industry-leading open-source IPS, Snort3. We recognize some customers want a fully managed service while others wish to configure their own policy.

Security Boulevard
MAY 19, 2021
In one sentence, the Same-Origin Policy is this: A script from one page can only access data from another page if they have the same origin. The SOP does not limit javascript code, and the HTML <script> tag is allowed to load Javascript code from any origin. And that’s the basics of the same-origin policy!

eSecurity Planet
JANUARY 30, 2023
There are also manual additions for projects that lack labels in the GitHub API (tags, topics). According to Wang, this is how sophisticated security teams operate these days, by “managing security policies and operations like code.” Wang said the ranking excludes bots and anonymous accounts from the number of contributors.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content