OSTE-Meta-Scanner: A comprehensive web vulnerability scanner
Penetration Testing
MARCH 20, 2024
OSTE-Meta-Scanner This project aims to simplify the field of Dynamic Application Security Testing.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 vulnerability-scanner
vulnerability-scanner 
Penetration Testing
MARCH 20, 2024
OSTE-Meta-Scanner This project aims to simplify the field of Dynamic Application Security Testing.
Google Security
DECEMBER 13, 2022
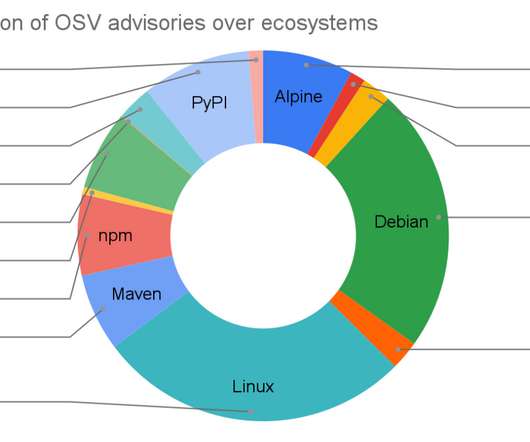
Posted by Rex Pan, software engineer, Google Open Source Security Team Today, we’re launching the OSV-Scanner , a free tool that gives open source developers easy access to vulnerability information relevant to their project. Scanners bring incredible benefits to project security, which is why the 2021 U.S.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

NetSpi Executives
MARCH 19, 2024
Vulnerability scanners help scan known assets, but what about the assets you don’t know exist? Why vulnerability scanners aren’t enough The issue lies in the fact that vulnerability scanners can only scan entities you tell them to. That’s where NetSPI ASM comes in.

Veracode Security
JANUARY 4, 2024
An open source vulnerability scanner (for scanning OSS) helps you discover risk in the third-party code you use. Background on Vulnerabilities in Open Source and What the Risk Looks Like Before we can talk about what to look for in a scanning solution, we need to talk about the vulnerabilities the tools are looking for.

Penetration Testing
DECEMBER 12, 2023
Egyscan Egyscan is The Best web vulnerability scanner; it’s a multifaceted security powerhouse designed to fortify your web applications against malicious threats.

Acunetix
JULY 17, 2022
DAST vulnerability scanners are not that different from virus scanners. A virus scanner scans a computer’s local resources and storage to find potentially malicious software. The post How scanners find vulnerabilities appeared first on Acunetix.
Bleeping Computer
DECEMBER 22, 2021
The Cybersecurity and Infrastructure Security Agency (CISA) has announced the release of a scanner for identifying web services impacted by& two Apache Log4j remote code execution vulnerabilities, tracked as CVE-2021-44228 and CVE-2021-45046. [.].
Security Affairs
JULY 9, 2020
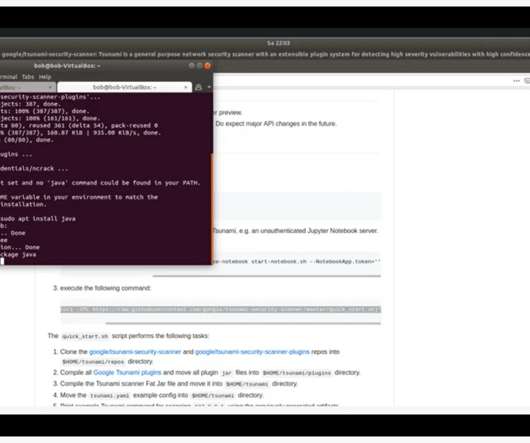
Google announced that its Tsunami vulnerability scanner for large-scale enterprise networks is going to be open-sourced. Google has decided to release as open-source a vulnerability scanner for large-scale enterprise networks named Tsunami. We hope that the engine can help other organizations protect their users’ data.

Tech Republic Security
SEPTEMBER 30, 2021
If you're looking for one of the best vulnerability scanners on the market, Nessus might be the ticket. Jack Wallen shows you how to install this platform on Rocky Linux.

Dark Reading
DECEMBER 13, 2022
OSV-Scanner generates a list of dependencies in a project and checks the OSV database for known vulnerabilities, Google says.

Security Boulevard
FEBRUARY 15, 2022
Log4j CVE-2021-44228 Since its discovery, much has already been said about the vulnerability discovered within the Log4j logging framework, CVE-2021-44228. The post Detecting Automated Vulnerability Scanners: Log4j Zero-Day Vulnerability Case Study appeared first on Security Boulevard.

NopSec
MARCH 14, 2023
Under the umbrella of risked-based vulnerability management (RBVM) live a host of tools who’s applications correspond to various stages of the vulnerability management lifecycle. Vulnerability assessment scanners discover the vulnerabilities in your environment.

Dark Reading
OCTOBER 26, 2022
Majority of vulnerability scanner tools overwhelming teams with false positives and missing exploitable vulnerabilities.

Penetration Testing
DECEMBER 20, 2022
OSV-Scanner Use OSV-Scanner to find existing vulnerabilities affecting your project’s dependencies. OSV-Scanner provides an officially supported frontend to the OSV database that connects a project’s list of dependencies with the vulnerabilities that affect them. Since... The post osv-scanner v1.5

Penetration Testing
MARCH 28, 2023
Artemis A modular web reconnaissance tool and vulnerability scanner based on Karton. releases: modular web reconnaissance tool and vulnerability scanner appeared first on Penetration Testing.

Penetration Testing
NOVEMBER 3, 2021
Web Cache Vulnerability Scanner Web Cache Vulnerability Scanner (WCVS) is a fast and versatile CLI scanner for web cache poisoning developed by Hackmanit. The scanner supports many different web cache poisoning techniques, includes a crawler to identify... The post Web Cache Vulnerability Scanner v1.1.1

Penetration Testing
APRIL 26, 2024
pphack pphack is a CLI tool for scanning websites for client-side prototype pollution vulnerabilities.

Bleeping Computer
MARCH 8, 2023
Both penetration testing and vulnerability scanning are essential to upholding and maintaining a strong security posture. Here are the benefits of combining both to maximize coverage and your web application security. [.]

eSecurity Planet
SEPTEMBER 24, 2019
PortSwigger Web Security's Burp is a top-rated web vulnerability scanner used in many organizations and is found in most penetration testing toolkits.

Security Affairs
MARCH 18, 2024
A critical vulnerability in WordPress miniOrange’s Malware Scanner and Web Application Firewall plugins can allow site takeover. The researchers at the Wordfence Threat Intelligence team also identified the same vulnerability in miniOrange’s Web Application Firewall plugin that has more than 300+ active installations.

SecurityTrails
NOVEMBER 8, 2021
Learn how to install Uniscan, and how to perform LFI, RFI, and RCE vulnerability scanning easily from Kali Linux.

The Hacker News
DECEMBER 23, 2021
on Wednesday released a joint advisory in response to widespread exploitation of multiple vulnerabilities in Apache's Log4j software library by nefarious adversaries. These vulnerabilities, especially Log4Shell, are severe," the intelligence agencies said in the new guidance. and the U.K. Sophisticated cyber threat actors

The Hacker News
DECEMBER 26, 2023
Poorly secured Linux SSH servers are being targeted by bad actors to install port scanners and dictionary attack tools with the goal of targeting other vulnerable servers and co-opting them into a network to carry out cryptocurrency mining and distributed denial-of-service (DDoS) attacks.

Tech Republic Security
OCTOBER 7, 2021
Vulnerability scanners are not enough, according to an expert who champions an all-encompassing holistic approach to vulnerability management as a means to eliminate surprises.

Bleeping Computer
FEBRUARY 15, 2024
In this article, Outpost24 explains three key limitations of automated vulnerability scanners, emphasizing the significance of manual pen testing in enhancing security. [.]

Penetration Testing
JULY 24, 2019
Brakeman Brakeman is an open-source static analysis tool that checks Ruby on Rails applications for security vulnerabilities. released: A static analysis security vulnerability scanner for Ruby on Rails applications appeared first on Penetration Testing.

CyberSecurity Insiders
NOVEMBER 19, 2022
Researchers at Cyber Security Works, Ivanti, and Cyware identify new vulnerabilities, blindspots in popular network scanners, and emerging Advanced Persistent Threat (APT) groups in a joint ransomware report. The total number of ransomware vulnerabilities out there has climbed to 323. New vulnerabilities, new threat actors.

Veracode Security
JANUARY 8, 2024
In this blog, we will explore vulnerabilities in JavaScript, best practices to secure your code, and tools to prevent attacks. Understanding JavaScript Vulnerabilities This article explores the common vulnerabilities related to JavaScript security and provides best practices to secure your code.
InfoWorld on Security
MARCH 20, 2024
GitHub is previewing code scanning autofix, a feature that combines its GitHub Copilot AI assistant with its CodeQL code scanner to provide suggested fixes to discovered vulnerabilities. Launched March 20 , code scanning autofix makes vulnerability fixes available right away as a developer is coding, GitHub said.

The Hacker News
DECEMBER 13, 2022
Google on Tuesday announced the open source availability of OSV-Scanner, a scanner that aims to offer easy access to vulnerability information about various projects.

Dark Reading
DECEMBER 22, 2021
The open-sourced scanner was derived from scanners built by members across the open source community, CISA reports.
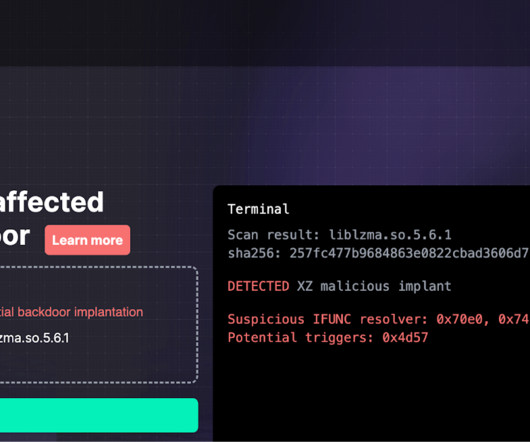
Security Affairs
APRIL 2, 2024
Researchers from the firmware security firm Binarly released a free online scanner to detect the CVE-2024-3094 Backdoor Last week, Microsoft engineer Andres Freund discovered a backdoor issue in the latest versions of the “xz” tools and libraries. The vulnerability was tracked as CVE-2024-3094 and received a CVSS score of 10.

Security Affairs
DECEMBER 22, 2021
US CISA release of a scanner for identifying web services affected by two Apache Log4j remote code execution vulnerabilities. We published an open-sourced log4j-scanner derived from scanners created by other members of the open-source community. Supports DNS callback for vulnerability discovery and validation.
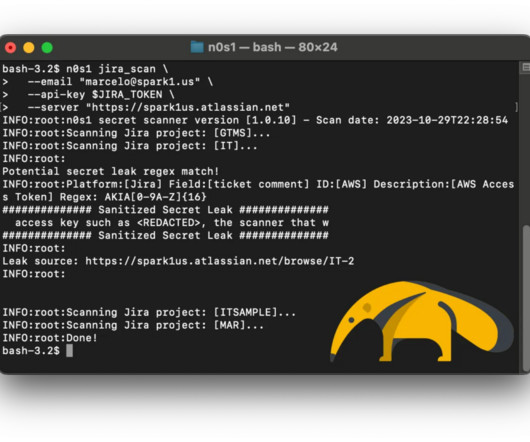
Pen Test
NOVEMBER 7, 2023
TLDR; Upgrade Confluence to a patched version and employ the open-source security scanner n0s1 to proactively address potential secret leaks. Why do I need a secret scanner? Both the vendor (Atlassian) and the US government have issued warnings regarding active exploitation of this vulnerability by nation-state actors.

Bleeping Computer
AUGUST 15, 2023
Mandiant has released a scanner to check if a Citrix NetScaler Application Delivery Controller (ADC) or NetScaler Gateway Appliance was compromised in widespread attacks exploiting the CVE-2023-3519 vulnerability. [.]
Security Affairs
APRIL 7, 2024
Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Bleeping Computer
DECEMBER 13, 2022
Google has launched OSV Scanner, a new tool that allows developers to scan for vulnerabilities in open-source software dependencies used in their project. [.].

eSecurity Planet
JULY 7, 2023
Vulnerability scanning is critically important for identifying security flaws in hardware and software, but vulnerability scanning types are as varied as the IT environments they’re designed to protect. Agent-Server: The scanner installs agent software on the target host in an agent-server architecture.

NopSec
SEPTEMBER 13, 2013
It not only has the capability to perform native scans on a wide variety of assets (external, internal, configuration, web application, wireless and more to come) but it also has the flexibility to import scan results from external scanners. The post Importing Vulnerability Scanner Results into Unified VRM appeared first on NopSec.
eSecurity Planet
APRIL 15, 2022
Unlike penetration tests , vulnerability tests do not consist of performing real attacks. However, they’re no less valuable, as they can spot vulnerabilities missed by a penetration test and provide a baseline for comparison. In addition, vulnerability tests allow IT teams to identify weaknesses before they become an actual problem.
Adam Levin
DECEMBER 9, 2020
FireEye’s breach disclosed that the threat actors behind the attack had acquired “scripts, tools, scanners, and techniques” used by FireEye security experts to simulate data breaches and cyberattacks. None of the hacking tools exploited “zero day” vulnerabilities. The hacking toolkit used by FireEye’s “Red Team” was compromised.

Google Security
APRIL 13, 2023
Posted by Julie Qiu, Go Security & Reliability and Oliver Chang, Google Open Source Security Team High profile open source vulnerabilities have made it clear that securing the supply chains underpinning modern software is an urgent, yet enormous, undertaking. All vulnerability database entries are reviewed and curated by the Go security team.

CyberSecurity Insiders
MARCH 9, 2023
Traditional vulnerability management is in need of a desperate change due to the lack of effectiveness in combating modern cyberattacks. Putting the monetary effect aside, a successful cyberattack from ineffective vulnerability management can fatally hit an organization’s reputation.

Dark Reading
NOVEMBER 2, 2021
Tenable added Raspberry Pi support to Nessus v10.0 to help security professionals conduct audits and assessments remotely.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content